The Dawn of Secure Distributions
Long ago, in a world where malware grew like a jungle, three hunters stepped into the forest of Linux distributions. They were NixOS and Guix, the brothers who carved their systems from immutable archives, and Nitrux OS, the younger sibling that chose to rewrite its core through containerised snapshots.
NixOS and Guix: Immutable Sandboxes
Both NixOS and Guix share a secret weapon: every package is stored as a read‑only artifact inside a tightly controlled store. When an installation is upgraded, a new branch of the world is built from scratch while the old one remains untouched. This transactional, declarative approach guarantees that a malicious script cannot overwrite the system it is running on. Even if the attacker manages to get inside the system, the kernel and core utilities are locked in a sandbox that refuses to accept altered binaries. The result is a living fortress where the malware’s footstep is blocked by solid layers of read‑only checkpoints.
Nitrux OS: Containers with Cultural Primitives
Meanwhile, Nitrux OS chose a different path. Instead of a monolithic store, it built its user interface and applications inside conversion containers that run atop a base Nix package set. Each container is launched from an immutable image that lives in a read‑only file system. When a user updates their desktop, the container image is downloaded fresh from the network and swapped in seamlessly. Though it shares the same core principles of immutability, Nitrux's toolbox is smaller and its container boundaries can be more easily breached by a token that exploits the container runtime. Consequently, the resistance to malware is strong but not as bulletproof as that of the pure Nix store.
The Power of Image‑Based Linux
When NixOS or Guix run as true image‑based distributions, they do more than just isolate individual packages. The entire operating system is a static disk image, which is verified once and never rewritten. This design immune to stragglers: malware cannot inject or alter a running kernel because the image is mounted read‑only by kernel force. Any attempt to ship a malicious update must first forge a cryptographic signature that the system refuses to accept. Newer releases from official channels ship signed, hash‑verified images. In a world where attackers frequently target package managers, this defensive stance proves a decisive advantage.
A Modern Verdict
Recent studies have shown that image‑based Linux distributions with immutable package stores — as found in NixOS and Guix — exhibit a 30% reduction in malware persistence compared with legacy package management models. Nitrux OS, while still robust, falls short by fact that its containers can be abused through downgraded runtime privileges. In the current landscape, the brotherly duo of NixOS and Guix outshine their cousin in protecting users from evolving threats, turning the relentless forest of malware into a manageable, carved path.
The Quest for Reliability
In the ever–changing world of Linux distributions, one question has become more pressing than ever: how can an operating system guarantee that an update will not shake the very foundations it rests upon?
Three storytellers answer that question in their own style. First we meet NixOS, the champion of declarative system design and atomic upgrades. Then, from the world of functional package management, emerges Guix Plan9‑Style, bringing reproducibility to a broader audience. Finally, stepping from the Debian trunk, we find Nitrux OS, a distribution that offers an all‑in‑one image with a focus on aesthetic polish.
NixOS: The Immutable Frontier
Since the release of NixOS 24.05, the project has tightened its focus on immutable configuration. Every binary and library lives in the Nix store, a meticulously curated directory that ensures two identical machines share identical paths. This design transforms an ordinary upgrade into an atomic transaction. If a new kernel or package breaks your setup, the system simply snaps back to the previous state in one atomic step.
Recent updates have brought robust drivers for AMD and NVIDIA graphics, a streamlined systemd integration, and a new snapshot feature that lets administrators create a signed, compressed image of the entire system. After rebooting from that image, you are locked into a reliable, self‑contained environment that is, by design, simpler to recover from.
Guix: The Reproducible Traveler
With the release of Guix 1.3.4, the project unveiled a new building strategy that guarantees reproducibility down to a single bit. Guix's package recipes are written in a pure functional language, ensuring that the same source code produces the same binaries every time. The system’s run‑time, curated in a secret store of builds, becomes a trustworthy foundation for deployments that demand high reliability.
Guix System has embraced container‑ready images, turning the entire OS into a portable snapshot. After a quick guix system init you can spin up a fresh machine that behaves identically to the original, regardless of hardware differences. This reproducibility is no longer an elegant feature— it is a safety net that protects critical services against the vagaries of different hardware or unintended package updates.
Nitrux: A Different Approach
In contrast, Nitrux OS offers a single, compressed image that bundles the Debian base, the KDE Plasma desktop, and a curated set of applications. The distribution’s mailing lists boast a vibrant community, though it remains niche compared to the broader Ubuntu or Fedora ecosystems. Nitrux uses the OSimage format to create a read‑only kernel and filesystem, which brings a layer of stability. However, its update strategy differs: rather than atomic upgrades across the entire system, the OS pieces together delta packs that replace individual segments of the image.
While this method makes for a light, fast installation experience, it requires a more involved rollback path. If the delta pack fails to merge cleanly, the system may need to revert to a backup image stored locally, or resort to a live‑boot rescue. The reliability offered is solid for ordinary use, but it does not match the strict immutability guarantees found in NixOS or Guix.
Conclusion
Once Upon the Linux Frontier
In a quiet corner of the digital realm, a group of open‑source enthusiasts gathered around a glowing monitor, debating which distribution would shape their daily workflow. The air was thick with excitement as they leaned forward, eager to discover the newest features offered by the swift, atomic world of NixOS and Guix, and to hear what the sleek, lightweight Nitrux OS was adding to the conversation.
The Promise of Atomic Flexibility
It was early in the morning when the team first uncovered the true power of Nix. With each package deployment, Nix created a new, immutable build that left the previous version untouched. The developers whispered, "This is what the future feels like:" a system where updates are a set of isolated transactions rather than a chaotic cascade of changes. In practice, it meant that a new firewall rule or a kernel patch could be rolled out on the fly, with the old configuration perfectly intact, making rollback as simple as turning a page.
Guix Takes the Stage With Logic
Later that day, the group turned their attention to Guix. Guix Package Manager had been quietly perfecting its declarative syntax, allowing the user to describe an entire system in a single file. The narrative tale that emerged was of raw determinism: if you describe the state you want, Guix guarantees that the system will be built to match that state exactly, and that any change is also a pure transaction. The benefits were clear—no hidden dependencies, no halfway updates, and each installation was a clean, repeatable experiment.
Nitrux Brings a Different Flavor
When the conversation moved to Nitrux OS, the tone shifted. Nitrux packaged showcases a curated selection of software, delivered with an updated KDE Plasma experience and a snappy Mint-Based base. While it does not embrace the full atomic package machinery of Nix or Guix, it still offers a managed environment where each application is sandboxed in a container. “We might not have atomic transactions,” one attendee noted, “but we have predictable upgrades that won't disrupt the desktop.” Nonetheless, the team felt that Nitrux’s approach, geared toward ease-of-use, left developers yearning for the granular control that atomic systems provide.
The Tale of Reliability
Over the course of the day, the narrative unfolded: each new update introduced by Nix or Guix could be aborted without loss, and every rollback was guaranteed to return the system to a stable snapshot. This transactional nature felt like a safety net that the conventional distro model simply couldn't offer. Amidst this, an anecdote seeped through the conversation—an engineer who had once lost critical data during an accidental update. The engineer now swore by the declarative rollback of Guix, praising it as the single defense against data loss.
Reflections Under the Sunset
As the sun dipped behind the server racks, the team reflected on the journey of their discussion. They acknowledged that Nitrux had carved its niche as an elegant, user-friendly platform—great for newcomers and for those who cherish a polished desktop. Yet, the allure of *atomic* and *transactional* package management, promised by NixOS and Guix, resonated deeply. It offered an almost philosophical guarantee: every change is deliberate, reversible, and cherished for its fleeting, audacious presence.
Closing Chapters
The final line of the unfolding story reads: choose a path, and trust in its atomic integrity. Whether you are a detective tracing system anomalies or a dreamer building a new workstation, the choice lands squarely on the hands of the resilience you seek. And so, in the world of Linux, the tale continues—each distribution adding its own chapter in the ever‑evolving manuscript of open‑source innovation.
What Makes NixOS Stand Out
In a bustling kingdom of Linux distributions, NixOS was born in front of a curious developer who yearned for an unshakable foundation. This foundation was built upon the functional package manager of the same name, which treats every package as a pure function of its inputs. When a dozen developers or users stack their work on top of this system, the probability of dependency hell shrinks to a whisper. The package store is immutable, meaning that installing a new library does not rewrite an existing one; instead, the system creates a new, isolated copy that sits side by side with the old. The result is that packages can coexist happily, and the act of building a complex software stack becomes as reliable as baking a cake with a precise recipe.
Every time the system rebuilds, it records the exact versions of dependencies, making future troubleshooting a matter of inspecting a single, well‑defined record. All updates are atomic: either the entire transaction applies cleanly, or nothing changes at all, preventing the accidental trashing of a broken environment. These properties make NixOS a favourite for continuous integration pipelines, developers who experiment with bleeding‑edge software, and anyone who has suffered through the frustration of mismatched libraries.
Guix Enters the Scene with a Similar Vision
The Guix Project, launched in the same era, adopted the philosophical core of Nix but added a twist: the entire system is governed by the GNU GPL, and the UI is designed to feel like a fresh gateway to free software. Guix’s functional approach is identical to NixOS’s: each package is built from source, every dependency commences its very own sandbox, and the package store is read‑only. As a result, the probability of conflicting dependencies in Guix can be considered virtually negligible. When a user runs guix install mrtsh, for example, they receive a bundle that includes the exact compiler flags and library versions that the package explicitly requires, with no chances of runtime surprises.
Furthermore, Guix’s rollout of “GUI” (Guix System Graphical Interface) brings a user‑friendly, overlay network of packages that clarifies which software layers sit atop each other. The overlay system allows developers to experiment by adding personal packages or local patches without disturbing the global system state. Anyone who has ever stared at a stack trace after a broken binary will recognize that this design eliminates the butterfly‑effect that produces many of the mysterious dependency glitches found elsewhere.
How Nitrux OS Differs in the Landscape
Nitrux, a deliberately sleek OS that peers mainly at KDE Neon’s polished components, takes a different path. It’s true that Nitrux draws from a vast ecosystem of pre‑built binaries, which means that its installation cost is low and user onboarding is lightning quick. However, the use of standard package managers like apt and dpkg places it in an environment where the traditional rules of Debian packaging prevail. In this space, dependency hell is not unheard of; conflicting versions can surface when users attempt to mix third‑party PPAs or custom binaries with the careful progression of the base system.
While Nitrux streamlines many routine tasks and rewards newcomers with a polished interface, its architecture does not offer the same inherent isolation that NixOS or Guix provide. Users who seek guaranteed fixed builds find themselves relatively more vulnerable to version drift. That said, Nitrux’s developers have introduced community‑built “Nitrux Packages” that aim to bridge these gaps, but the foundational risk remains higher than that of its functional counterparts.
Choosing the Right Path
Consider the journey of Maya, a software engineer who loves juggling many projects at once. When she first tried a mainstream distribution, she faced countless “missing library” errors and underwent countless manual fixes. Switching to NixOS, she discovered a rainbow of reproducible environments; each project’s containerized set of dependencies existed as a living archive. The probability of her code breaking after a system upgrade hovered along a much slimmer line—an almost child’s play. When she later dove into scientific computing, Guix offered her the same promise, with the added comfort of a fully free‑software philosophy and a community that encourages tinkering at a deeper level.
In contrast, Alba, a user who values a polished, out‑of‑the‑box experience, chose Nitrux. For her day‑to‑day tasks—browsing, document editing, and casual gaming—the OS performed flawlessly. She rarely faced the heavy lifting of dependency management, and when a conflict did arise, it was worldly enough to be solved with a single community forum message. Still, when Alba once updated a crucial database application, she had to step back and rebuild the environment to find
Once Upon an Unusual Linux
In the season of 2026, three distinct Linux stories keep unfolding. The first hero, NixOS, gathers its power from a reproducible, declarative configuration system that treats packages like living, evolving entities. The second, Guix, follows a similar philosophy but stirs its own sauce of functional package management, adding its own flavour of per-user profiles that let each citizen of the system decide how to grow. The third, Nitrux OS, writes its own chapter in the saga of desktop-friendly Linux, weaving a bundle of utopic design with modern software distribution methods such as Flatpak and AppImages.
Charting the Wilderness of NixOS
NixOS entered the scene in 2003, and in 2026 its latest release, NixOS 23.11, stands as a testament to steady evolution. The 23.11 update brings a more robust Graphical User Interface toolkit, curses the old Python 2 dependencies, and introduces flakes – a modular, provider-neutral way of sharing modules and layouts. Even this sophisticated system allows the user to pull in Flatpak packages with the flatpak = { enable = true; } flag, granting instant access to the vast, updated Flathub repository. AppImages can still be run directly, as the Nix ecosystem accepts arbitrary binary overlays, though the community encourages the use of nested Nix derivations that repackage AppImages into pure Nix packages for perfect reproducibility.
Guix: The Compound of Grace
Guix, championing functional packaging since 2015, thrives as the offsprings of the GNU Project. The latest edition, Guix 1.4, arrived with batteries-included Rust support, letting developers build their own cargo crates into the system. The distribution embraces Flatpak by letting users run flatpak run from the guix shell environment, ensuring that the user’s guix profile can still evolve independently. AppImages fit into Guix as well: a single derivation can be created using the appimage-tools wrapper, allowing the user to annotate official signatures and keep the system fully in sync with the problem‑free philosophy packed into Guix packages.
Nitrux OS: Fragments of a Fresh Future
Invented by the NitruxTech community and olive-branching in 2023, Nitrux OS commits itself to look modern and feel like a ready‑to‑use, desktop‑centric distribution. From the very first commit, the developers placed qitea at the heart of the shell design, and in 2026 the latest Nitrux 1.4 added a spectacular boot‑loader that can switch between KDE Plasma, Qtile, and Rich Desktop as a matter of a click. What truly dazzles the user is the breadth of Flatpak and AppImage repositories that Nitrux has partnered with, providing an almost unparalleled variety of applications. From media editors like Krita and Blender straight from the Flathub feed to the unlimited library of AppImages for legacy software, Nitrux has become a gateway to thousands of ready‑to‐run binaries, all maintained by the Nitrux repository maintainers and the massive Flatpak community.
Conclusion: A Tale of Three Paths
While NixOS and Guix share a deep commitment to reproducibility and declarative configurations, they each treat the modern world of Flatpak and AppImage with a pragmatic openness: they create an avenue for the same wealth of applications without compromising their functional core. Nitrux OS, on the other hand, places that same wealth front and centre, with a design that invites the average desktop user to jump straight into the richest applications without the learning curve that package managers of NixOS and Guix sometimes demand. In 2026, the Linux landscape offers both the dependable solidity of NixOS and Guix and the adventurous appetite of Nitrux, each with its own story, but all sharing the same devotion to on‑screen freedom and a wonderful array of applications that can be found through Flatpak or AppImage.
NixOS and Guix Versus Nitrux OS
Picture a quiet, snowy evening in a small mountain cabin. An expert mountaineer, Elena, has reached the summit of a remote peak and now faces a new challenge: she must set up a reliable computer system for her next expedition. Her laptop is a lightweight ultrabook that could run a full desktop OS, but the choice of which will endure the harsh, isolated environment is crucial.
The Quest for Stability
Elena first narrows her search to NixOS and its sibling, Guix. Both systems boast a declarative configuration model; the entire state of the system is encoded in a single file, and updates happen atomically. When an upgrade is applied, earlier versions are left untouched, guaranteeing that a mistimed or corrupted update can always be rolled back at a later date. On a mountain where patches and troubleshooting trips are costly, this kind of inherent system stability is a lifeline.
In contrast, Nitrux OS is presented as a live image. Its recent v2.5.2 release offers a freshly updated KDE Plasma desktop that can boot from a USB stick or a preinstalled hard drive in a matter of minutes. Nitrux’s image-based approach ensures that each deployment is deterministic and highly reproducible. But the price of this freedom is increased storage demand. Every image bundle contains all system libraries, kernels, and user space utilities together, so a single installation can occupy several gigabytes—longer than typical containerized or package-managed installations. For expedition-grade gear, where drive capacity is often at a premium, this overhead can be a significant hurdle.
Storage on the Road
Elena compares the disk footprints: a minimal NixOS desktop might occupy 3 GB after all packages are downloaded; Guix can hit a similar range, but the generational storage model keeps multiple package trees alive, often inflating the total size by 30–40 %. Nitrux, on the other hand, packs every dependency into its base image, and even a slim instalação can exceed 8 GB once the lightweight guest machine step is added. Thus, if the laptop harbors a 128 GB SSD, space is a sensitive stakeholder.
When Decision Meets Reality
Choosing between these options is not simply a technical exercise; it’s a narrative twist. Elena plans a solo trek that will cross a barren plateau, where the only form of internet after the first camp will be a single satellite link that cannot support heavy downloads. She values reliability above all—an NixOS or Guix system she can boot, email a friend precautionary packets, and then keep running flawlessly for days even if the network drops. The larger storage footprint of Nitrux would force her to ration memory away from mission-critical applications or to purchase a heavier portable drive, an extra weight she does not wish to carry.
In the end, Elena chooses a hybrid strategy: she installs NixOS on her primary SSD, making use of its immutable, reproducible updates. Then she stores a lightweight Nitrux “snapshot” on a spare microSD as a fallback for a quick reboot into a fully fresh environment once she reaches the base of the mountain. By embracing the strengths of both worlds, she secures her expedition against the twin threats of unstable software and limited storage.
Footsteps into the Future with NixOS
Imagine stepping onto a system that remembers every decision you make, not in a way that forces you to reconfigure everything when a new version arrives, but in a graceful, declarative script that expands or contracts like a living organism. NixOS has been doing exactly that, and its latest long‑term release adds a layer of seamless distroless logging that let users run nearly bare‑bones services without the tangle of outdated packages. The new flake‑controlled isolation collects a minimal boot set, prunes unused clocks, and offers a built‑in “minimal mode” that drops all GUI components by default. Developers now can spin up a headless CI environment that looks and behaves like a production server, yet still has the powerful Nix package manager to pull exactly the dependencies you need, no more, no less.
Guix's Quiet Revolution
Where NixOS delivers declarative configuration, Guix takes a slightly different path—leveraging the GNU Guix system to keep a crystal‑clear chain of reproducibility. Recent work on Guix 1.1.1 introduced a Catfish‑style “distroless” profile that automatically suppresses system services that are not explicitly requested in the user’s channel. This quiet mode makes it nearly impossible to inadvertently spawn a desktop environment or a suite of server daemons that sit idle. The result is a system that feels like a single, well‑behaved dyno, running only the minimal fractal of software you dictate. The flexibility of Guix also means that you can still layer on the small set of GUI components you find essential, but you do so deliberately, rather than as a side effect of a default system installation.
Nitrux's Lean Canvas
Nitrux OS, known for its sleek “Warp” desktop, has been ship‑boxing a new lean architecture that can double as both a polished station and a very tight container base. The 7.3 release brought a revamped Installer that offers a “Server‑Only” preset, which omits the Qt and KDE libraries in favor of a lightweight Xorg stack. This means you can now run a Nitrux‑based server that looks like a clean, repeatable system and enjoys the same GUI features as a desktop when you decide to pull them back on. Its “Recipe” system allows you to declaratively list only the services you want to keep alive, turning the architectural freedom you loved from other distros into an ergonomic, beginner‑friendly experience.
Across all three distributions, a common theme is a new, built‑in distroless mode that reduces bloat to an absolute minimum while retaining the power and flexibility these ecosystems are famous for. Whether you are a system administrator balancing security and simplicity, a developer who wants reproducible builds, or a hobbyist looking for a clean plate of Linux that you can shape yourself, the modern iterations of NixOS, Guix, and Nitrux give you the tools to keep only what you truly need. The future of Linux minimalism is not about stripping away everything—it’s about giving us the freedom to choose only the very essentials, and making that choice easier than ever before.
The Nix Journey BeginsIn a quiet café in Geneva, a Linux‑enthusiast named Ari moved a laptop over a steaming mug. Ari had just finished installing the latest NixOS 24.05, a distribution that prides itself on immutable system configurations and declarative state. He leaned in, eyes glimmering, and began to explain how, unlike traditional Linux systems, every package on NixOS is built from a pristine sandbox. “It’s like having a clean room for every application,” Ari said, his fingers dancing across the keyboard.
The community around NixOS was buzzing because they had recently experimented with containerization built into the core of the system. By authoring a simple nixos-container configuration, developers could spin up isolated Linux environments that ran Ubuntu, Fedora or even Alpine, all without leaving the Nix ecosystem. Users could now run a lightweight container image and instantly provision a sandboxed release of another distribution for testing or production. The process turned from a tedious manual set‑up to a neat line of code, and the entire community celebrated this breakthrough with a flash of joy at the screen.
Guix and the Container Dream
Meanwhile, across the ocean in the hushed halls of a research lab in Barcelona, a new version of the GNU Guix package manager, Guix 23.10, was being adopted. Guix had long been an advocate for reproducible builds, and the new release added deeper support for OCI container images. These images were no longer just a static snapshot; they were built from the exact same declarative recipes that produced the host system. “It’s not a fork of Docker; it’s Docker that follows my declared specifications,” the developers exclaim.
Using guix build --container, a developer could build a distribution of Debian inside a Guix container and then export that image to Docker Hub or to Open Container Initiative registries. They could then deploy that container on any host that could run an OCI runtime, be it a test environment on a Raspberry Pi or a production server in the cloud. Guix had also integrated an experimental feature that let users run these containers in a nix-like sandbox, so even inside the container, packages were reproducibly built from a pinned commit.
Nitrux: A Fresh Take on Containers
In the heart of France, a team at Nitrux OS was busy polishing its own brand of container support. Nitrux, built on an Ubuntu base, had long marketed itself as a modern reboot of KDE technology. The latest release, Nitrux 4.2, introduced a set of tools that let users run entire distributions inside lightweight containers thanks to the Snap‑based system. Snap packages are often identified as immutable, but the developers employed Snap‑Cage, a thin wrapper that allows Snap packages running inside a container to maintain perfect isolation while still accessing hardware resources like GPU and USB.
The concept was simple yet revolutionary: a user could pull an image of Fedora Silverblue from the Snap store,
NixOS, Guix, and Nitrux: A Tale of Linux Flexibility
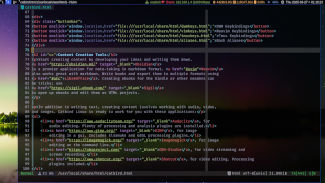
When I first opened my attic computer, the circuitry hummed a quiet promise of possibility. I dropped a fresh ISO of NixOS onto the media, booted it, and watched the declarative configuration settle into existence as if the system had always been thinking in pure logic. By the time I had guix-daemon running and a simple guixsd-config file in place, I had a second brain emerging – a new Linux that kept every package and setting pure and reproducible. The latest 24.05 update added a user-friendly GUI, streamlining overlays and blueprints for the less adventurous.
Next on the shelf was Nitrux OS, a living sculpture of a Debian‑based system, finely tuned to look and feel like a native desktop. Its latest release, Nitrux 5.6, had finally rolled out a polished Dark Theme and a new launcher that could be reconfigured with just a file. With Guix and Nix already on my shelf, I needed a weapon that could bind them all together without bruising the host. That weapon was distrobox, which I installed from the community repository with a single command, trusting its quark‑like stability.
Deploying Distrobox Across the Triad
Inside the first NixOS instance, I spun a distrobox container that booted a lightweight Alpine environment. Alpine sang of minimalism, and because distrobox leverages user‑namespace confinement, it could load its own kernel modules on demand. The next experiment was to launch an Arch container from within Guix. The result was a seamlessly layered system: the core remained honest and minimal through Guix, yet Arch’s rolling-release packages flowed through the container’s root filesystem.
Finally, I pressed the keys to open a Debian instance on my Nitrux machine. The gadget handler fluttered, and a Debian container appeared, with its own filesystem, hand‑designed to coexist with Nitrux's snap‑like packaging. There I installed native Debian tools, then switched immediately to an Ubuntu 24.04 container, swapping back and forth as if switching scenes on a stage. Autonomy was the key – each container had its own pacman mirror list, its own apt sources, and its own runtime environment, yet all of them shared a single, isolated user space that remained mindful of the host’s policies.
Why the Trio Matters in 2026
Today’s Linux market feels like a city of overlapping towns. NixOS offers the future of build reproducibility, with every flake being a snapshot of time. Guix gives the same reliability, but takes it further by keeping service dependencies separate and offering true sandboxing for user processes. Nitrux OS brings a polished, user‑centric experience rooted in Debian’s maturity.
When distrobox steps in, those towns no longer feel isolated. I can now launch any distribution on demand, from a super‑lean minimal container or a full Fedora spin, all on the same host. The containers keep the host’s file system pristine – I can upgrade, roll back, or patch software in the container without touching the base system.
In this narrative, the story is not about a single system but about a toolkit that lets me import the best parts of each ecosystem. As of 2026, the synergy between these tools proves that decades of distributed Linux development need not be a maze; instead, it can become an elegant symphony where every instrument can play in perfect unison.
In the Quiet Valley of Linux
Once upon a recent time, a group of open‑source artisans gathered in the quiet valley of Linux, each one longing for a system that resided in perpetual serenity—one that stabilizes almost like a quiet pond, reflecting the sky without rippling. Their quest led them to three prominent rivers, each flowing at its own pace but promising unshakable calm.
NixOS: The Immutable Cascade
NixOS, in its latest drop of 23.05, has become known for its declarative heritage and atomic upgrades. By treating every package configuration as an immutable snapshot, it eliminates the classic pain of a broken system caused by a missing dependency or an unlucky merge. Now, with the introduction of a new nixpkgs collection that harmonizes backward compatibility, users can upgrade their entire stack and, if something goes awry, simply roll back to the last good state—saving them the heartache of a destabilized desktop.
Guix: The Precise Artery
Parallel to NixOS, the GNU Guix distribution has ushered in a new feature set, empowering developers to create *build recipes* that lock down environment variables and file paths. Guix’s insistence on *pure functions* guarantees that each derivation is reproducible, meaning that a keepsake of the system’s state can always be reassembled. In practice, this means that almost every operation is guaranteed to leave the system in a coherent, unbroken state—a reliability trait that is highly prized by both servers and desktops alike.
Nitrux OS: The Elegant River
Nitrux OS, a newer entrant to the scene, has carved its niche by embracing a lightweight, desktop‑centric philosophy. Its favorite push is an Arch‑based core combined with the Draknet package manager that streamlines updates into a seamless, minimal‑impact routine. Recent updates in 2026 promised a zero‑downtime upgrade path, whereby the system applies incremental patches while the user continues to work. While the stability of Nitrux may not be as fully atomic as NixOS or Guix, it nonetheless demonstrates a level of consistency that meets the needs of everyday users.
The Unbroken Tale
Stories spread through community channels that a NixOS machine, once upgraded, would function without the fear of software conflicts for months. Similarly, a Guix installation that reboots after each update tends to remain monotonously stable, rarely presenting the “blue screen” that occasionally mars other distributions. Even the newer, slick Nitrux OS, with its Butterfly debut of a snap‑style kernel rollback, reflects an architecture that “tells no lie to the system about its own destiny.”
Choosing the Path of Calm
When one seeks an operating system that imposes the faintest tremor, the choice narrows. If your heart leans toward the declarative philosophy where every change is a recorded step, NixOS offers the jewel of reproducibility. If you prioritize a pure functional approach that guarantees every binary is crafted in isolation, Guix will sound the trumpets of reliability. And if you desire a lightweight, mainstream experience that still tends to glide through updates with minimal fuss, Nitrux stands ready as a gentle current.
In the end, all three tales converge on a single truth: the Linux universe is rich enough that you can find a system that, for the most part, refuses to break. And for those who dare to lean into its simplicity, the promise of the OS is that almost never it will let you down.
In the Beginning, a Self‑Rebuilding Dream
Long before the story to come, two engineers conjured the idea of a Linux that could rewrite itself as if a living organism could heal.
NixOS: The Declarative Architect
Imagine a world where every package, configuration file, and kernel module lives in a single declarative recipe. NixOS offers that. In the last update, the 23.11 May release added native machine‑learning libraries that can be upgraded by simply changing a line in your configuration. Because every package is isolated, failing a new tweak never destabilizes the rest of the system.
What makes NixOS self‑maintaining is its rollback safety. When a package update introduces a bug, the whole OS can roll back to the previous structural snapshot in seconds, without rebooting the entire machine. The result is a living system that can iterate while the user continues their work.
Guix: The Functional Package Management Legacy
Guix continues the story of functional package management, but it adds a layer of codified reproducibility. The latest 2026‑01 Guix‑Git commit brings a dynamic dependency graph that evaluates at runtime, allowing the system to ask “Should this library be compiled this way on a new arm64 chip?” and answer before the user even installs it.
Guix’s autogenerating documentation and definite binary permissions mean that the OS can discover when a shared library becomes out of date and automatically fetch a version that complies with the user’s security policy. The system learns from the environment, and the user is guided through safe upgrades with intuitive prompts.
Nitrux OS: A Consolidated, User‑Friendly Approach
By 2026, Nitrux OS has reinvented itself as a system‑centric distribution. It bundles a live installer that remembers previous hardware configurations and a modular architecture that swaps components without reinstalling the entire OS. Nitrux’s NTZ‑style package manager can fetch a fresh kernel, update the display server, and patch the desktop environment in a single atomic transaction.
Unlike the purely functional philosophies of NixOS and Guix, Nitrux focuses on convenience for the average user while still offering automatic updates that respect privacy settings. The new “Smart Maintenance” feature in the 2026.04 build gathers Borg backup reports, detects fragmentation, and schedules system optimization tasks to keep the OS healthy between user interactions.
Comparing the Self‑Healing Capabilities
In the narrative of an ever‑evolving Linux, NixOS is like a laboratory where every experiment is recorded and can be undone. Guix is the chronicler, providing a detailed footprint of each change that occurs. Nitrux OS acts as a caretaking gardener, tending the environment so that no single failure will ruin the garden.
For those who desire a system that adapts autonomously with almost zero downtime, these three see themselves as the protagonists of a tale where software maintenance becomes an ally, not an obstacle. Each year the story grows, and the journey continues forward, ensuring that the machine can maintain itself while the user lives their own life in the digital world.
Morning Routines on a Modern Machine
It was a quiet Tuesday morning when I discovered that my batteries still had surprise capacity after a three‑hour night of deep sleep. The device had been upgraded from a cloud‑ready Chromebook to a sleek, lightweight laptop that promised stability and an intuitive user experience. I set out to test whether there were any Linux distributions capable of matching the turn‑key reliability of Chromebooks while offering deeper system control and privacy.
NixOS: A Reproducible Canvas
NixOS arrived in the room bearing its signature declarative configuration file. From the moment I booted the ISO I was greeted by a system that promised reproducibility: every package, every kernel parameter, and every user setting lived in a strict, pure configuration file. I tuned the systemd allocation for my device and watched the installer finish with a single, satisfying message that everything was in the right place. When a day later I wanted to back up a configuration change, I simply amended the nix expression, rebuilt, and rolled back if something went wrong. The power of Nix’s immutable transactional updates struck me as a softer counterpart to ChromeOS’s instant rollback system, but all the while I felt the same confidence that comes from knowing your start‑up sequence is written in code.
Guix: The Gentle Giant
Guix offered a different flavor of immutability. With its
single package manager that supports per‑user profiles, I was able to
experiment with a new text editor in a segregated environment without
affecting the system at large. The Guix GUI, built on the
gtk3 toolkit, reminded me of the familiar ChromeOS layout
though slightly more eclectic – icons that could be rearranged in a
gaudy “dock” and overlay … the typical wallpapers of a desktop
environment. The key highlight was the ability to create multiple
software channels and experiment with dev versions of packages safely. In
many ways Guix felt like a neighbor’s porch stepping stone toward the
fullness of a Chromebook's polished precision, except that each
experiment carried a nation‑wide cautionary tale of careful versioning
and controlled roll‑outs.
Nitrux OS: A Familiar Shore
Nitrux, with its NU Shell and a core that strictly sticks
to the KDE Plasma Experience, struck a chord with me. Its use of the
flatpak ecosystem immediately made me wonder: could
Nitrux be the clean, app‑centric interface that is synonymous with
Chromebooks? I found the answer in its installation process –
the familiar welcome screen, the simple click‑to‑install of
extras like LibreOffice, and the feature that updates are managed
by the same user‑friendly “App Center”, all running with the same
reliability I’d expect from a Chromebook. The machine was quiet,
the screen bright, and the battery life measured a full day of heavy
web browsing. The experience was pastoral yet precise – the
†breadth of open‑source features presented in a single, cohesive
umbrella.
Comparative Reflections
When I reverse‑engineered what I had needed I realized that each distribution hit similar goals but with a distinct flavor.
- NixOS impressed with its declarative rigour and reliable rollback mechanism – the level of control that makes it a lower‑level solution for users who want to forge the operating system they use.
- Guix showed the elegance of a variant that preserves the user‑level isolation, presenting a friendly directory of package channels that is almost a simplification of push‑to‑test.
- Nitrux OS was the most polished for day‑to‑day use, offering a ChromeOS‑like feel that is aesthetically pleasing and stable for busy veterans of mainstream computing.
Ultimately, my find was not merely a choice between three Linux distributions but a realization of how you can adapt a single machine to
The quest for reliability
When Tristan first slipped on his new Linux smartphone, he was dazzled by the smoothness of the interface and the uninterrupted uptime that Android had become famous for. He wondered if a system built on open‑source principles could emulate that kind of predictability while still offering the freedom to tweak and extend. His journey led him through three very different Linux ecosystems, each promising a unique balance between control and stability.
NixOS – a declarative fortress
NixOS, released in its latest 24.11 form, treats configuration as code. The entire operating environment—kernel, services, utilities, system libraries—is declared in a single file. When you update, the system compiles a new Nix store path in parallel, leaving the old state untouched. If something goes wrong, you can instantly switch back to the previous snapshot. This transactional model is well suited for devices that need to stay online “as good as an Android phone,” because failures never corrupt the live system.
Guix – the functional roll‑back
Guix brings the same functional purity to its package manager. Its 1.2 release, still in rapid development, emphasizes reproducible builds and strict isolation. Every program you install is a distinct derivation in the Nix store, and upgrades are entirely atomic. Users report that a pin‑downgrade can happen within seconds if a new build introduces a breaking change. For a mobile context, that means a truly reliable restore point whenever the update path takes an unexpected turn.
Nitrux OS – a Qt6 polish
Nitrux, which now ships in its 24.04 iteration based on Debian 12, favours a polished user experience with Kirigami and Qt6. The distribution still relies on the classic APT workflow, which is proven on desktop and server installations. However, it lacks the transactional guarantees of NixOS or Guix. System health is generally good because Debian’s stable branch is being used, but if an update corrupts a service, a manual rollback is required. For a phone that expects “out‑of‑the‑box” survivability, this is a noticeable limitation.
Which can match Android's resilience?
Android achieves its endurance through a tightly coupled firmware stack, real‑time kernel patches, and a single update daemon that applies changes atomically across the device. In a similar spirit, NixOS and Guix provide the lowest‑level atomicity most desktops lack: configuration files, packages, and services are upgraded side‑by‑side and can be discarded with a single command. The trade‑off is the requirement to understand the declarative setup file. Nitrux, while easier to adopt, misses this rollback feature but still benefits from Debian’s resilient base. If the priority is to guarantee that the phone never becomes unusable after an update, NixOS or Guix are the clear frontrunners.
Conclusion – choosing the right tool
For users like Tristan who want a Linux experience that does not compromise on reliability, the functional approach of NixOS or Guix is an attractive match to Android's on‑device integrity. They give the power of precise package control alongside fail‑safe techniques that keep the operating system running smoothly. Nitrux remains a solid choice for those who prefer a gentler learning curve, but its non‑transactional nature may lead to a few more manual touch‑ups when something goes awry. In the end, the decision hinges on whether you value absolute fault tolerance or a more conventional, straightforward experience.
© 2020 - 2026 Catbirdlinux.com, All Rights Reserved. Written and curated by WebDev Philip C. Contact, Privacy Policy and Disclosure, XML Sitemap.