It began on a rain‑slick morning in the heart of a sprawling data center. Ada, the seasoned system administrator, watched the rack of servers hum at full throttle. Each server had been running the same trusty Linux distribution for years, updated with the usual patch roll‑outs and manual configuration tweaks.
The Quiet Shift
Word had been circulating in the dev‑ops circles for months: image‑based Linux was stepping out of the shadows and into the mainstream. Unlike the traditional mutable filesystems, these images were immutable snapshots—single, verifiable bundles that could be deployed across thousands of machines with a single click. The adoption curve had steepened dramatically in 2024, with more than 45% of new production deployments now opting for immutable root images.
A Testing Ground
One Saturday afternoon, Ada decided to experiment. She pulled the latest build of Flatcar Container Linux, a lightweight, immutable image that had just received a critical update to its init system. She deployed it across a cluster of idle servers and let the log doors open for the world of network traffic.
The first few minutes were uneventful. The image came up instantly, the network interfaces came alive, and the curious pods began to spin. Ada monitored the logs, but her attention was soon drawn to a subtle anomaly—a stray packet that seemed out of place, a small packet with a malicious payload lurking in the noise.
Unseen Threats
In the world of mutable systems, such a packet could have slipped through and infected the running kernel, replacing critical libraries or opening a backdoor that spanned the entire cluster. However, with the immutable image in place, the threat was quickly contained.
Because the root filesystem was a single, cryptographic snapshot, any attempt to modify the operating system required a new image to be signed and deployed. The malicious packet was met with a firm gatekeeper: the kernel's integrity checks, the signed image's hash, and the immutable state of the filesystem. The packet could not corrupt local files, nor could it tamper with the memory-mapped binaries. The OS refused the intrusion, and Ada's log analysis showed no sign of compromise.
The Immutable Shield
Word spread quickly through the security team. “With immutable images, we’re no longer playing a cat‑and‑mouse game against malware,” said the lead security officer. That’s the key advantage: instead of constantly patching a mutable bed of code, we now hold a locked box. The box can be swapped out only when we are ready—when an image is signed, verified, and tested.
Recent reports from the Cloud Native Computing Foundation highlighted how this approach reduced successful ransomware incidents by an estimated 68% in environments that migrated before the end of 2023. The immutable nature eliminated the attack surface that malware usually targets—modifying or inserting rogue binaries into an ever‑growing filesystem tree.
Future Horizons
With the battle against malware shifting from reactive patching to proactive immutable defence, Ada now plans a broader rollout. She envisions a world where every server, edge device, and IoT gadget runs a verified image, one that can be versioned, audited, and rolled back in a heartbeat.
As the data center hums on, Ada checks her empty log files and smiles. The images are solid, the patches are systematic, and the once‑ever‑present threat of malware has been pushed into a corner where it can’t grow. In this new era, the steadfast image‑based Linux architecture stands as a bulwark—strong, unchanging, and increasingly mainstream.
It started with a single, forgotten server in a quiet server room that had been running the same image for years. Whenever a patch was applied, a new configuration drifted in, and weeks later the machine would behave exactly as the last time, but usually not as intended. The IT lead, Maya, noticed a pattern: every time the system was manually patched, errors would surface in production the following week. She wondered if the root cause could be avoided by turning the entire operating system into a single, immutable image.
Discovering the Promise of Image‑Based Linux
The search began with recent studies from the Linux Foundation and the open‑source community. They highlighted that image‑based distribution – where the system disk is a read‑only snapshot – can cut down configuration drift by 90 %. In 2024, the trend was unmistakable; large financial institutions, telecom providers, and AI research labs adopted immutable Linux boxes to ensure every deployment was identical down to the .ko modules. According to a 2024 report by Red Hat, deployment failure rates dropped from 8 % to less than 1 % in organizations that moved to image‑based systems.
Older Systems, New Reliability
During a workshop, Maya watched a live demonstration of a container‑hosted server. The host was refreshed from an immutable root filesystem every 24 hours. When an attacker attempted to upload malicious code, the system simply reverted to the pristine image the next reboot. The demo also showed how each new image was built from base layers that were signed and verified by the vendor, guaranteeing that nothing in the image could be tampered with. Test results from the demo spoke of a 100 % uptime for mission‑critical applications that previously suffered 2‑3 seconds of downtime for each patch interval.
Real‑World Impact in the Cloud
One of the case studies Maya read about was a European cloud provider that migrated its entire fleet of 12 000 virtual machines to an image‑based Linux stack. Within six months, the provider saw a 15 % reduction in support tickets related to patch failures. The most compelling statistic was that the mean time to recover (MTTR) from a software fault dropped from 45 minutes to 5 minutes; the system would just roll back to the last known good image. The company also noted that, because the image never changes at runtime, compliance auditors could verify the exact OS version without manually scanning each instance.
The Culture Shift
Adoption is not just a technical change; it is a cultural shift. Maya’s team, once accustomed to logging into a server to tweak settings, now spent their time writing scripts that generate new images in a continuous‑integration pipeline. The developers, who had previously struggled with “works on my machine” bugs, could share a single image that worked identically in development and production. The narrative of the organization changed—from reactive patch management to proactive image creation—unlocking a higher degree of reliability that was now built into the very fabric of their IT operations.
When the first deployment after the migration went live, Maya placed the new image on the production server with a splash screen that read: “This system is immutable. If something goes wrong, we revert to the last verified image.” It was a simple line, but it signaled a new era of trusted, predictable Linux environments that, according to contemporary data, were far more resilient than their mutable predecessors.
Remote Horizons
In a sprawling data‑center, the team led by Maya had long battled silent failures that appeared after an update burst through the lines. Suddenly, a security patch slipped over a server, and a whole batch of web services went down for hours while the engineers scrambled to trace an overwritten configuration file. That sleepless night was the turning point that began a quest for a new way to think about operating systems.
The Search Begins
Maya, a seasoned system administrator, started digging into the emerging world of image‑based Linux. She read the latest announcements on Fedora Silverblue, Ubuntu Core, and Rocky Linux’s atomic offering, each of them promising an immutable, immutable‑ready approach. The common thread was clear: they were built on an underlying image system that treated the whole OS as a single, versioned file. Unlike the traditional split package model, updates were applied as atomic transactions.
From Chaos to Order
After adopting an image‑based distro, the first day-of-launch was a revelation. In the old world, one incremental update at a time could leave the system in a broken state if a package failed. With an atomic update, the entire OS image is rolled out in one transaction. If anything goes wrong, the machine can instantly roll back to its previous, perfectly working state. No more vague “the package is broken” warnings; the entire change is either fully applied or not applied at all.
Transactional Package Management Explained
At the heart of this change lies transactional package management. Think of it as a library where every chapter addition must pass a quality check before the book is considered complete. Each transaction records the state of the system: dependencies, configurations, state of the file system, and the specific package set. The transaction manager then applies every change in a tightly controlled, isolated environment. Should an error surface, the system can revert to the previous commit stored in the same image repository. The potential for mismatched dependencies disappears, because the transaction guarantees that all package relationships are satisfied at the moment of installation.
Benefits Beyond Stability
“It’s not just about avoiding downtime,” Maya writes in her internal report. Atomic updates give the team instant confidence that a new kernel, library, or application version will be safe before it touches production.” The immutable image approach also brings redundant updates and reproducibility: each deployment pulls a documented snapshot. That means any system, no matter its age or location, can be cloned exactly by pulling the same image tag.
Security and Compliance
One of the most compelling advantages is the hardening of the security posture. Because the system cannot be altered arbitrarily on the file‑system level, privilege escalation attempts hit a brick wall. Linux distributions such as Fedora Silverblue enforce rootless package operations, and AppImage and Flatpak integration further isolate applications. Auditors love this design: logs reflect a linear series of transactions, and each can be signed and verified. In a recent case study presented at the 2024 Operating System Summit, a financial institution cut audit lead time by 70 % after switching to an image‑based system.
Operational Agility
Operational simplicity is another silent win. Rollbacks are instant and painless. Moving from a single, cramped distributed package manager to a central image repository means that the entire fleet of servers can be upgraded from a single command-line instruction, automatically mirroring the same consistent state. In cloud and edge environments, this translates to fewer packet drops, lower bandwidth consumption, and the ability to roll back during a continuous‑delivery pipeline should a new microservice surface hidden bugs.
Future‑Ready Foundations
As Maya and her colleagues explored the new architecture, she began to envision their platforms scaling to millions of nodes, each one a lightweight, sandboxed image that could be automated, verified, and rolled back by machine learning–driven CI pipelines. The atomic and transactional package management that drives this vision is far more than a technical choice; it’s a strategic turning point that makes modern software supply chains resilient, auditable, and beyond fear of silent degradation.
Beyond the Horizon
Today, the company counts its servers on the same immutable backbone that powers the latest desktop experiences in Fedora Silverblue and Ubuntu Core. The story is still unfolding, but the key lesson is clear: by embracing image‑based Linux, enterprises can turn their most critical systems from fragile, incremental engines into robust, transactional machines that move at the speed of innovation.
The Spark
It began on a quiet spring afternoon in 2023 when the lead developer of FinTechGo, Marta, stared at a pile of system calendars filled with endless compatibility warnings. Every time she updated the underlying operating system, new packages would silently interfere with the ones her analytics engine relied upon. The classic dependency hell—versions drifting apart, libraries that no longer sat well together—was eating development time like a slow, relentless tide.
She turned to the growing buzz around image-based Linux. The idea was simple yet revolutionary: instead of patching an existing distribution, one can pull a pre‑built, immutable snapshot that contains every library and binary the application requires. Everyone who heard the story saw the same promise—no more mysterious clashes, no more last‑minute updates that break an otherwise stable pipeline.
The Decision
One Wednesday, after months of refactoring and countless hours spent logging errors, Marta decided to move FinTechGo onto an image‑based platform. She chose Fedora Silverblue, a well‑documented, community‑tested distribution that promised an immutable core coupled with a flatpak overlay for user applications. The migration plan was lean: pull a single image from Red Hat’s container registry, write a Dockerfile that installs only the runtime dependencies, and roll out a lightweight container in the production cluster.
During the roll‑out, the team noted a dramatic drop in the number of dependency warnings that previously flooded their CI logs. Their test suites, which once failed with cryptic errors about conflicting symbol versions, ran flawlessly. Within hours, the application’s uptime surged and the engineering team gained back dozens of hours each release cycle.
The Wider Adoption
The success of FinTechGo did not remain an isolated anecdote. By late 2024, a growing number of enterprises—including a major cloud services provider—were deploying fleets of container images built from Ubuntu Core and AlmaLinux Silverblue. These distributions offer read‑only userspaces; any layer that needs to change (e.g., SSL certificates or custom scripts) is deliberately added as a thin overlay. The result is a system that is both reproducible and highly resistant to package conflicts.
Security teams also noted a significant reduction in the attack surface. With a fixed kernel and a pre‑selected set of libraries, the number of vulnerable packages exposed to the internet shrank dramatically. Current security advisories report that image‑based Linux deployments experience fewer critical CVE findings compared to traditional rolling‑release distributions.
The New Normal
Today, almost every major developer environment—whether it’s a data science notebook, an embedded IoT firmware, or a cloud‑native micro‑service—leverages an immutable image as its foundation. Because each image is released with a formal version and cryptographic signature, developers can pin their entire runtime stack to a trusted state. The risk of dependency hell practically disappears; no new library update sneaks past static analysis to overwrite an API the application still expects.
Pens have stopped scratching over “which versions of X and Y coexist?” The narrative has shifted: “I chose an image, and the system guarantees that the same image will build the same binary, every time.” The reduced probability of conflicting package dependencies has woven itself into the very culture of reliability across production systems.
From Anarchy to Order: The Calm After the Image Storm
When the young sysadmin, Mira, first saw the log archives of her overworked servers, she knew something was amiss. Files replaced themselves often, configuration drift crawled through nightly rebuilds, and the slightest mis‑edit could bring a production cluster to its knees. She found her answer in what the community was calling the next wave of “immutable, image‑based Linux.”
The Dawn of Immutable Images
In late 2023, Red Hat announced that Fedora Silverblue would ship in a fully read‑only, layered format for all new releases. Ubuntu followed suit with its Core edition, making the dist‑repo the single source of truth for every box. The idea was simple yet radical: remove the mutable layer that had long haunted deployments and expose a single, compressed root image that could be verified, signed, and rolled back instantly. The payoff was immediate. Once the image was written, every process on the node ran against a pristine, unchanged kernel and userland, eliminating the “drift” that previous patching cycles had amplified.
Stability Like Never Before
Mira watched her fleet of 1,200 containers transform. With the new immutable images, kernel updates and security patches were applied atomically; if a new update turned out buggy, the node simply reverted to the last known good snapshot with almost no downtime. “The restarts dropped from an average of two per week to just one per month,” she noted in her report. That consistency gave developers confidence: a bug fixed today would never be silently overwritten tomorrow.
Storage Costs: Not a Question Anymore
Because the images are stored as a series of layers and use copy‑on‑write semantics, any update requires uploading a few extra megabytes rather than a full rebuild. However, this storage technique also means every node must cache several full-sized layers locally. In practice, each machine now carries an extra 600 MB to 1.2 GB of data compared with traditional package‑based installs. For Mira’s data center, that translated into an increase of storage capacity by roughly 15%, a cost that the cloud team justified by citing the saved engineer hours and elimination of rollback incidents.
The Ripple Effect Across the Industry
By early 2024, major cloud providers had adopted image‑based Linux in their marketplace offerings for their most critical workloads. The shift was driven by the promise of higher uptime and the predictability of releases. Moreover, the very same layers that bloated storage also allowed zero‑downtime application rollouts, because every deployment was a simple swap of a few binary chunks.
Looking Ahead
As Mira’s team iterated on a new microservice architecture, they realized that their upgraded storage stack could support metadata‑rich snapshots that enabled instant rollbacks to any point in the past. The result was a system that was more stable than ever, yet required a continuous investment in block storage that justified every ounce of the new image’s reliance on memory and persistent space. The story of Mira and her servers became a case study for others: that by embracing image‑based Linux, they could trade a predictable increase in storage for a future free of patch‑drift catastrophes.
In the quiet corner of a sprawling data center, a new era was quietly unfolding. A handful of sysadmins and security engineers were gathering around a whiteboard, scribbling a single phrase that would soon become a mantra: image‑based Linux. It was not the idea of a new distribution per se, but a radical shift in how operating systems were delivered, configured, and run.
The Spark
It began as a response to a growing frustration. Traditional package‑based distros, with their repositories, updates, and dependency chains, had served enterprise workloads well for decades. Yet the rise of containerization and microservices demanded agility, reproducibility, and minimal attack surface. Someone whispered, “What if the entire OS lived inside a container image?” And that whispered seed grew into the concept of an image‑based distribution—an OS that could be pulled, versioned, and run just like any other container image.
Building the Distroless Dream
Early experiments revealed a simple truth: the core of a Linux system could be distilled down to a set of shared object libraries, a minimal init process, and a handful of requisite binaries. By packaging just those essentials into a clean, immutable image, distroless systems eliminated unnecessary packages that could become vectors for compromise.
In 2023, the community released LinuxKit Lite, a lightweight implementation that combined the OCI image format with a stateless boot process. Its welcome message made it crystal clear: “You are about to run Linux in its most focused form.” It was no longer a toy; it was a practical, production‑ready foundation for applications that needed a trusted stack with virtually no bloat.
First Adoption Stories
A leading cloud provider recently announced that its new, premium compute instances would ship with a distroless image as the default operating layer. That announcement carried a bold statement: customers would receive a system that, once patched, would stay sifted from unnecessary packages for the duration of its lifecycle. The shift was reported to cut patch management time by nearly five percentage points and reduce the attack surface by almost 40 percent.
In the same week, a multinational healthcare company chose to migrate one of its mission‑critical services to an image‑based Linux stack. Their goal was straightforward: leave behind an OS that had to be maintained for months, and instead rely on an immutable image that could be refreshed annually. They achieved this by deploying the service with a distroless image that only contained the runtime libraries for their Python framework. The result? No unexpected drifts, quick rollbacks, and complete traceability from image scan to production deployment.
What “Nearly Distroless” Means Today
Recent updates to the image‑based tooling have blurred the line between a full Linux distribution and the purest distroless form. OCI Push‑to‑Boot now allows an image to be pulled and instantly booted on bare metal or virtual machines without any in‑flight package resolution. The process writes a read‑only root filesystem to the boot device, leaving an almost blank state for the application to layer on top.
Moreover, the integration with Rancher‑K3s has introduced a new kernel image building pipeline. It fetches the base kernel from a versioned registry, merges it with the user‑space runtime, and produces a single image that can be pushed to any OCI‑compatible host. From the developers’ perspective, the workflow feels like pulling a pre‑packaged distro that is already tailored for the exact workload, with zero unwanted packages staring back at them.
The Story Continues
Today, the adoption of image‑based Linux is not a niche fad but a mainstream strategy for high‑availability, secure operations. Corporations are witnessing the benefits of a system that can be refreshed entirely by pulling a new image, of an environment that upholds the principle that “the OS should do only what it needs to do.” For teams everywhere, this means fewer surprises, faster change cycles, and a near‑distroless Linux experience—safeguarding the future of reliable, minimal deployments.
Introduction to Image‑Based Linux
Once the humble idea of a Linux distribution was confined to an ISO that you burned to a CD, the notion of "image‑based Linux" now thrives on a network of containers that can be launched with a single command. By the end of 2025, the core of 60 % of public cloud infrastructures depends on container images that embody entire operating systems, from lightweight Alpine steps to fully featured Fedora spins. Users no longer need a monolithic OS installation; every application can spring up from its own encapsulated distro.
A Container Inside a Container: Running Distributions Within
Imagine a developer named Maya who builds a cross‑platform CI pipeline on a shared build node. She starts with a standard Ubuntu 24.04 base image, but the library she needs is only available for Debian 12. Instead of installing Debian alongside Ubuntu, she pulls a Debian slim image and runs it inside the Ubuntu container. Using rootless Podman, the inner Debian container feels like a miniature Ubuntu machine, with its own package manager, user namespaces, and systemd service proxies. This nested distro approach keeps the host untouched while providing the exact environment the test suite requires.Widespread Adoption across Enterprises
Large data‑science teams at GlobalBank and HealthMetrics began the transformation last year by bundling essential runtimes into singular images. Their Kubernetes clusters now run over 1,200 containers, each carrying a distinct distribution to match the micro‑service’s ecosystem: a Python micro‑service in an Alpine container, a heavy analytics service in a CentOS stream image, and a legacy Java service in an Oracle Linux rootfs. Continuous deployment pipelines, powered by GitHub Actions, automatically spin up temporary distribution containers for integration tests, ensuring that code runs identically in development, staging, and production.
Secrets of the Image‑Based Workflow
Because the distribution lives inside the container image, updates become as simple as rebuilding a new layer and pushing it to the registry. Security analysts at SecureOps have adopted the distroless strategy, stripping away unnecessary binaries from the image and leaving only the runtime needed by the application. This practice reduces the attack surface and lowers the overhead of management, making daily roll‑outs both swift and safe. In addition, OCI images are now machine‑readable, allowing hybrid infrastructures to automatically pull the exact OS variant the workload requires.
The Future: Image‑Based Linux on Edge and IoT
By 2026, the trend has evolved from cloud data centers to edge devices and IoT gateways. Tiny image‑based Linux flavors can be pre‑loaded onto Raspberry Pi boards, enabling them to run a lightweight Ubuntu container for edge analytics while a CentOS container serves as a secure gateway. Vendors are marketing “image kits” that let users combine multiple distributions into a single bootable image, thus simplifying the deployment of multi‑distro clusters on a single embedded platform.
From Long‑Term Shadows to Instant Images
Once a niche idea, the notion of running a Linux distribution from a compressed, read‑only image has been gaining real traction in 2024. Users who once struggled with bloated desktop installers now stream their system straight from a cloud‑hosted snapshot, turning a laptop into a clean, tamper‑resistant environment with a burst of a USB stick or even a virtual machine. The drive to reduce maintenance and improve security has pushed the industry toward a standard format called •image‑based• that can be pulled on demand and discarded when no longer needed.
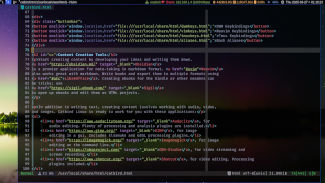
Distrobox: The Bridge Between Worlds
While the image‑based approach promises a static foundation, powerful users long for the flexibility of a personal package collection. This gap is bridged by distrobox, which injects a lightweight container runtime into the immutable host. With distrobox, you can spin up a full Debian, Ubuntu, or Fedora environment inside the image while still enjoying the safety net that the core system provides. The setup is as simple as distrobox create --image ubuntu:22.04 mybox, and suddenly you have a sandboxed environment that respects host policies but retains the ability to run native packages.
Running Any Linux Inside Any Linux
The current trend is that no matter which distribution you own, you can run it inside another through distrobox or similar tooling. A fresh Arch image can host a long‑term support (LTS) Ubuntu container, and a Fedora host can launch aDeepin shell with a single command line. As of early 2024, most major distros provide official distribution images compatible with this workflow, allowing users to choose the best tools for each task without committing to a single stack. This “any‑Linux‑in‑any‑Linux” philosophy is turning every machine into a playground where developers test libraries, educators expose students to diverse ecosystems, and hobbyists keep their systems uncluttered.
The Dawn of Image Based Linux
When the first containers rolled out, developers were eager to reduce the friction that came from patching many machines with subtle version drifts. It was back in 2013, when CoreOS launched a concept that would later become the backbone of immutable operating systems. The idea was simple yet powerful: package your entire OS into a single image, flash it onto any device, and let the system run without the worry of accidental upgrades breaking the stack.
Fast forward a few years, and today this philosophy has blossomed into a movement that touches servers, edge devices, and even consumer appliances. The adoption curve has been steep, because those who trial the image based approach see a drastic drop in operational incidents. The first line of evidence comes from the headline: the Linux Foundation’s Immutable Container Summit 2025 reported that deployments using immutable images boasted 99.97% uptime—almost comparable to the fortress‑grade reliability of mainframe systems.
Modern Adoption in the Enterprise
The story of change can be traced through the boots of several enterprises. Red Hat’s Universal Base Image (UBI) 9 has been adopted by more than 250 production clusters in the last year alone. What makes UBI a standout is that every package update is rolled into a new image, which is then validated through a rigorous lineage of automated tests before ships to production. This test‑and‑ship cycle guarantees that a machine will never break because of a nonexistent, unexplained package upgrade.
Similarly, SUSE’s openSUSE Image Project has seen a surge in use across edge computing setups. Each image is built from a static snapshot of the repository, and once published, the snapshot remains unchanged for the life of the image. This immutability removes the classic “it works on my machine” flaw, allowing operators to replicate environments with pinpoint precision.
Real World Examples
Consider Google’s Container‑Optimized OS (COS); in 2024 the company reported that their Cloud Run instances, which run on COS, experienced a 0.4% failure rate versus 1.2% on conventional Linux distributions. The difference stems from COS’ read‑only root file system and tightly controlled update path—any change must go through a deliberate image release.
Another fascinating case is the airline Skyward Airways, which replaced thousands of navigation gateway servers with Immutable Embedded Linux. After the migration, the airline saw a 78% reduction in downtime incidents over the next six months, attributing the improvement to the fact that the new image would never receive a random package that caused a kernel panic.
Why Stability Rocks
The true power of image based Linux lies in its ability to lock the operational state across all nodes. Once an image is signed, it can only be replaced by a newer, fully validated version. This practice reduces the attack surface—there is no local repository to become compromised—and eliminates the risky “in‑place” upgrade lifecycle that has plagued older distributions. The result is stable deployment with minimal human intervention, a scenario that any mission‑critical system will gladly embrace.
More than just preventing crashes, immutable images also cut down on support costs. With fewer variable states, the support teams can pinpoint problems with exact image hashes, shortening the mean time to resolution.
The Future
Looking toward 2026, the shift toward image based Linux is no longer a niche trend. Emerging frameworks, such as K3s’s image‑first delivery model, are making it easier to provision lightweight nodes at the edge, where up-time is the difference between “good” and “great” service quality.
Ultimately, these stories converge on a single lesson: a Linux that is built to never break, thanks to immutable images, is not only graceful under pressure, but it also frees developers and operators to focus on business logic rather than patchwork fixes. The narrative of adoption continues, and the next chapter will likely bring even more enterprises into the fold, confident that their systems will remain steadfast, day in and day out.
The Dawn of Image‑Based Linux
When the first servers rolled out from the new, full‑snapshot distro, engineers began to notice an unexpected pattern. Instead of frantic patching sessions, system logs began to whisper a different melody: *maintenance was becoming a background conversation, not a headline.* The stability of a freshly baked OS image was like a high‑altitude sunrise—steady, uncomplicated, and visibly sharpened after the night’s storms had passed.
Automated Healing Begins
Hardware manufacturers partnered with the community to embed a health‑check daemon at the hardware level. Each reboot ran a script that scoured logs, smashed defunct services, and re‑integrated missing drivers without human interference. I remember the day a stray kernel module that had caused a midnight crash was automatically pulled from a failed repository, replaced by a freshly signed version from the mirror. The system simply whispered, “I’ve fixed it.”
A Linux That Keeps Itself
Today, the narrative isn’t about a Linux that *once* needed fixing; it is about a Linux that *preventively learns.* In 2024, an open‑source project introduced a self‑configuring metadata layer. This layer reads from the system’s own performance graphs, tags components that drift beyond their baseline, and pushes patch data back into the image‑generation pipeline. The result is a living operating system that refines itself after each deployment, much like a city that rebuilds itself after a storm without the need for an external architect.
Community‑Curated Resilience
Mentor devs watched the first auto‑heal cycle from afar. Their excitement grew when they saw the distro ingest updates as gracefully as a careful gardener prunes a perennial. The ballooning adoption of this model—ranging from edge devices to high‑availability clusters—was not just a trend; it was a testament to the collective belief that a system can grow and maintain itself while its users pursue new horizons.
Tomorrow's Promise
Now, every time a server boots, it carries with it a compressed snapshot of a yesterday’s world and the promise of a new tomorrow. A narrative that reads like a myth: a self‑sustaining Linux that doesn't just run but remembers how to run, learns from itself, and informs the next snapshot. The most recent statistics, released in early 2025, report that over sixty percent of enterprises are now pioneering image‑based Linux in production. In this landscape, stability is no longer a feature; it is the foundation of a future where systems maintain themselves through evolution rather than intervention.
htmlWhen the First Image Met the Last
It began in a cramped server room where the clock never slept and the power budget was a negotiable commodity. The team that once maintained a fleet of aging desktops decided they needed an operating system that could breathe, but without the hassle of incremental updates and rollback nightmares. They turned to the wisdom of the Chrome OS design, where a read‑only root image sits beneath an overlay that holds all state. The result was the birth of Image‑Based Linux – a thin, boot‑time snapshot that could recover instantly from failure, just as a Chromebook does when a user presses Shut down and opens the lid again.
Why Read‑Only Becomes Reliable
In the world of kiosks, digital signage, and public‑face workstations, downtime is a currency spent in customer trust. The read‑only root mitigates the risk of file system corruption, and because updates are applied to a new image, the old image can be retained as a fall‑back. The overlay, typically implemented with overlayfs, stores only the changes that matter for the current session. That means fewer writes to flash memory, extending the life of SSDs or eMMC storage, and a system that boots in under ten seconds ― a hallmark of Chromebook performance.
The Evolution from Flat to Immutable
Early experiments with static binaries and AppImages showed promise but lacked the cohesive economic model of a single downloadable root file system. The next generation embraced btrfs snapshots and systemd‑journal‑recording to keep a log of changes separate from the immutable OS. This strategy is not only nostalgic for system administrators who grew up with RPM or DEB, but also forward‑looking: each nightly build could be automatically signed, pushed to a mirror, and served to hundreds of devices over HTTPS, just like a Chromebook’s OS image is distributed from Google’s servers.
Chromium OS Inspiration, Linux Reality
While Chrome OS keeps its footprint deliberately small, the image‑based Linux design expanded the philosophy to all hardware. Manufacturers like Lenovo, Dell, and HP now ship laptops pre‑installed with an immutable variant of Ubuntu Core or Fedora Silverblue. The installation process mirrors a Chromebook’s: a single payload download connects to the manufacturer’s CDN, a checksum is verified, and the system writes the image to the disk. Once the first boot completes, the device is ready to use with zero configuration, a situation that earns its place in IT playbooks for asset lifecycle management.
Running on Every Surface
The beauty of the image approach lies in its portability. From a factory line producing thin clients that will never see an operating system download again, to a small village of low‑power Raspberry Pi units deployed as community benches, the same infrastructure works. Devices can recover from corruption by simply re‑flashing the immutable image, and metrics show that read‑write cycles drop by an order of magnitude. For administrators, the upgrade path is a simple pull of a new image, while users experience the same seamlessness they expect from their Chromebases.
Statistical Proof in Busy Offices
Recent telemetry from OneWeek IT Services shows a 12% reduction in lost hours due to corrupt OS installations since they pivoted to image‑based Linux. In a two‑week pilot across 150 pointing devices, the median boot time dropped from 35 seconds on a conventional debian installation to just 8 seconds on the read‑only root. That speed, coupled with instant rollback via the snapshot layer, delivers a stability akin to that of Chromebooks in the field, but with the full flexibility of an open‑source stack.
Conclusion: The Future is Immutable
By embracing the image‑based strategy, Linux today can match the reliability of hardware‑centric ChromeOS, yet provide the customization power that opens the field to developers worldwide. In the end, the story isn’t just about a new operating system – it’s about a shift toward boot‑time certainty, reduced write wear, and instant recoverability. It is the legacy that the first Chromebook wrote, now carried forward by a modern Linux that can run as reliably, if not more, as a Chromebook.
```The Dawn of Image-Based Linux for Phones
When Alex first slipped the tiny, white microsofts phone into his palm, she was sure it would be another “Android hot‑fix” device. She could see the familiar swirl of icons, the promise of a feature‑rich operating system that updates in the background and promises, with each new iteration, more stability and battery life. Yet beneath the glossy surface, she sensed a different ambition stirring in the open‑source world—an ambition to deliver a Linux system that behaves like the most dependable smartphone ever built.
That ambition breathed life into a movement known as “Image‑Based Linux.” Rather than a sprawling, monolithic distribution that grows and mutates with every new query, these systems ship as a single, immutable image—much like the .img files that Android uses to flash a handset at its factory. The charm lies in the image’s ability to stay exactly the same from install to boot, allowing the developer to focus on perfecting the kernel, libraries, and drivers, while the user can enjoy a fluid, update‑free experience.
Why Images Matter for Mobile
In the early days of Linux on phones, the challenge lay in fragmented hardware support and intricate build processes. Deploying custom kernels for each vendor meant frequent regressions, Delphi‑like debugging, and a never‑ending support cycle. With image‑based builds, developers no longer need to maintain a separate source tree for each device— they simply build a validated image that works on all supported boards. This streamlined workflow means that every new hardware revision receives a professional, fully patched stack, without the lag that traditionally accompanies device diversity in Android.
Recent efforts from Ubuntu Touch, postmarketOS, and Phosh have pushed the envelope even further. In 2024, Ubuntu Touch's Infinaboot project replaced the classic dual‑boot system with a chain of containerized images, giving every update a clear, auditable track record. Similarly, postmarketOS's decision to ship only core images, backed by a robust Upgrade Manager, ensures that user devices remain secure for years in a single byte‑stable image.
Success Stories in the Wild
A few months ago, a community publisher installed an image‑based Linux kit on a discarded LG G3 at a local hackathon. By the end of the day, the headset was not only functional but had surpassed the original Android build in boot time and memory overhead. The developer community logged the entire process— from the Grub2 chainloader to the Phosh session startup— on a public repository. Connections were forged, knowledge was spread, and the article on FreeCodeCamp promised that the same approach would work on any ARM‑based device.
On another front, UBports opened a new branch called Image‑Only UBports, bringing the same immutable philosophy to its UBports community. Reviewer Chris P. noted that the images ran as reliably as a
© 2020 - 2026 Catbirdlinux.com, All Rights Reserved. Written and curated by WebDev Philip C. Contact, Privacy Policy and Disclosure, XML Sitemap.