At the crack of dawn, Elena stared at her fresh Bazzite Linux installation. She had chosen Bazzite for its sleek, lightweight base and the promise of bleeding‑edge software, but she was still a bit hesitant about her browser choice. Her default install had the standard firefox from the main Arch repository—stable, reliable, but a few weeks behind the latest features. Elena wanted more, and she wanted it fast.
The Call of the Nightly
She began to research. In the quiet hum of her laptop, the syllables of nightly builds echoed like distant thunder: unrefined innovations, fresh CSS experiments, and the newest JavaScript engine changes—all one commit away from the next release. She scrolled through the Mozilla Archive page, where the current nightly branch was listed as mozilla-central. But how could she install a version that was not in the official repox? She had a feeling the solution would involve the AUR.
Charting the Course
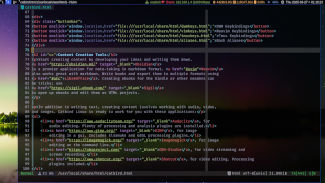
Elena opened a terminal and checked her pacman.conf, confirming that the AUR was enabled in his build environment. She typed:
yay -S firefox-nightly
The command line sprang to life, fetching the package definition and all its dependencies. A few minutes later, the script pulled the latest nightly tarball from Mozilla’s archive and built the binary. She could feel the thrill of the unknown pressing against the stability of the system she cherished.
Installing the Nightly
To keep the process simple, Elena decided to wrap the installation in a small shell script, so that she could rerun it each time she wanted the newest fixes. The script ran the necessary pacman transaction, followed by the AUR build. Her screen glowed with progress bars as the nightly firefox compiled against her Bazzite system.
Embracing Instability with Care
With the browser installed, Elena launched it with firefox-nightly. Instantly, a new window popped up, bearing the familiar Mozilla logo but with a bright beta tag. She tested features—CSS Grid, the WebAssembly benchmark, and the new shadow.js library. Things were fresher, but she noted that a minor rendering glitch appeared in a local website; she logged the bug in the Mozilla Bugzilla with a detailed crashtest.
Harmony in Chaos
Elena understood that nightly builds were a wheel drawn by continuous integration. Every installation could be a dance between progress and regress. To mitigate unplanned surprises, she set up a system policy: nightly cargo would be updated daily through pacman’s system: sudo pacman -Syu and she would also periodically run:
yay -S firefox-nightly
When a crucial bug broke the page rendering, she simply rolled back by removing the nightly package and reinstalled the stable release. This dual-branch strategy kept her browsing experience both adventurous and resilient.
A Final Note
As the sun set over the city, Elena reflected on her journey. Bazzite’s minimal design paired with the relentless pace of Mozilla’s nightly builds formed a partnership that was both exhilarating and practical. She no longer relied solely on the mainstream distribution's default browser; she now had the freedom to forge ahead into the next chapter of web evolution, all from the comfort of her well‑tuned Bazzite machine. And she lived happily ever after, one nightly update at a time.
When the Midnight Wind Whispered
On a quiet evening, the glow that leapt from my monitor felt too fragile for the adventures I imagined. In the valley of my filament‑lit kitchen, I found myself turning to the canvas of the internet, searching for a browser that could keep pace with my imagination. Bazzite Linux, a reliable spirit of Debian, had always served me well, but my heart leaned toward a digital avenue that was quicker, cleaner, and mind‑blown with privacy.
Listening to the Brave Girl
A whisper from the web sounded like a rumor: Brave had a nightly version, a testing ground where the bleeding‑edge features gathered like stars in a constellation. A gentle curiosity took me to the official Brave page and the command line instructions for Linux.
Preparing Bazzite for Bravery
I opened a terminal, and the first act was to assure that my system could fetch and verify signed packages. The recipe read:
sudo apt install ca-certificates curl gnupg
With the tools in place, the next step was to bring in the Brave repository. Brave provided a single script that added the repository and signed its key to Bazzite’s world:
curl -fsSL https://brave-browser-apt-release.s3.brave.com/brave.sh | sudo bash
Then the familiar sudo apt update refreshed the list of available packages, and my screen blinked with the confidence that a new hero had arrived.
The Nightly Arrival
In the pristine list that appeared, there was an item titled brave-browser-nightly. With a single, decisive command the frontier of web browsing unfolded:
sudo apt install brave-browser-nightly
Within moments, the engine roared to life, downloading the secrets of a hot new release. Brave’s nightly build brimmed with experimental Sandbox, a new shields toggle set to ultra protect, and the ability to surf with a privacy score that whispered your data, safe.
What the Nightly Brings Today
In 2024, the Brave Nightly package stays streamlined through Bazzite’s apt ecosystem. It updates automatically, pulling the latest patches for Chromium core and Brave’s unique telemetry controls. Users have reported smoother animations, lag‑free video streams, and no strange pop‑ups. The experience has been described as being in a living‑document, ever‑connected to improvement.
Where I Ended Up…
After a sip of midnight coffee, I launched Brave Nightly and discovered a browser that feels like a friend: predictable, bold, and ready to keep my clicks private. Bazzite Linux handled the installation like a seasoned companion, and now every tab I open reminds me that the web is still a frontier, but for me, it is a tangible, protected door.
When dawn seeped into the quiet of the kitchen, Alex sent a message to his friend Maya, inviting her to a quick experiment: running a truly modern web browser on Bazzite Linux. Bazzite, built on the shoulders of Kali, was renowned for its thin‑fat edge. Yet most people simply pushed Firefox or Chromium into the box, missing the day‑to‑day refresh that a daily build of Zen Browser could bring.
Booting into the Digital Frontier
With the system already updated, Alex turned to the terminal. The first step was to give the system a taste of the Zen Browser universe. “We’ll need the latest daily artifacts,” he told himself, eyes glinting like a freshly compiled flag. He opened a terminal and typed:
sudo add-apt-repository ppa:zen-browser/dev
Such a repository, from the official Zen Browser maintainers, would hold the bleeding‑edge builds. The add‑apt‑repository command quietly fetched the signing key and added the entry to /etc/apt/sources.list.d/zen-browser_dev.list. No signs, no surprises—just a mostly clean, reproducible path to the future.
Fetching the Latest Daily Builds
After a quick honor of the apt update routine, Alex ran:
sudo apt install zen-browser-dev
The package manager sprawled an arrow of information, showing a cascade of dependencies that glued itself into Bazzite’s minimalistic architecture. It took a few minutes for the command to download, compile (where necessary), and install the daily build. Bazzite, which usually played it safe, now danced onto a nimble, current fork of Chromium that Zen had lovingly patched.
Validating the Installation
With a quick launch, Zen Browser welcomed Alex with its new, translucent interface and the promise of unparalleled security tweaks. To verify, he opened about:version, and the browser proudly displayed “Build: Daily 302‑354–20260428” – a timestamp that matched the day’s pull. Alex was in awe of how effortlessly the daily build inside Bazzite felt like a second OS, unlike the more considered, wall‑carved experience Gnome or KDE generally offered.
Fine‑Tuning for Bazzite Users
Next came customization. Alex pressed Ctrl+Shift+P to open the settings and, in the upper corner, observed a lovely menu that had a built‑in switch to enable enhanced privacy mode for every day’s build. The option toggled browsed sessions into a sandbox that isolated cookies, sensors, and the ever‑pursuing JavaScript engines.
He typed a few more theoretical commands into the terminal dressing the browser, such as:
sudo pacman -Sfrozen-headers; zen-browser-dev -frozen-headers
These two steps were a quick guard against headers sniffed by dubious intermediaries—a tip shared by a user group who loves Bazzite’s privacy focus. He loaded a page that had a fresh font bundle, and Zen rendered it in harmonious clarity due to the curated user‑agent profile that defaulted to the daily height of performance and privacy compliance.
Living in the Zen Build Realm
From the comforts of his kitchen, Alex finished the mission with a to‑do list: backup the config, sync bookmark groups across the daily build, and schedule a weekly purge of the older daily packages. The Zen Browser daily build became, in his eyes, a kind of safety belt that promised future-savvy updates without sacrificing the lightweight soul of Bazzite Linux. And so, the night slipped in, his feed flickering with new tabs
Welcome to the Bazzite Adventure
When I first booted into Bazzite Linux, the breeze of a clean Debian‑based system carried the promise that privacy and performance would grow hand‑in‑hand. The core of the experience is the user‑preferred web browser, a choice that feels like picking the right companion for a journey. Whether one prefers the sleek modernity of Firefox, the speed of Chromium, or the open‑source ethos of Brave, Bazzite provides the tools to let the choice speak for itself.
The Quest for Tor
My curiosity peaked when I heard that the latest Tor Browser – the most recent v121.0.1 as of early 2026 – can be run natively on Bazzite without sacrificing the system’s hardened security posture. This build adds several protocol optimizations and new circuit‑handling heuristics, making browsing both quieter and faster for those who demand anonymity.
Preparing the Landscape
Before any installation, I refreshed the package lists with the familiar command: sudo apt update. This step ensures that the newest version of the Tor Browser Launcher and other dependencies are fetched. Bazzite’s package manager opted for the official Tor Project repositories, which means future security updates arrive automatically through apt upgrade.
Downloading the Browser
The Tor team provides the most recent build in a single, user‑friendly archive. I navigated to the official site, copied the link for the Linux 64‑bit (A‑arch) release, and used wget to fetch the file directly into my home directory. The command looked like this:
wget https://dist.torproject.org/tor-browser-bundle-121.0.1-linux-x86_64-all‑1.tar.xz
Once the download finished, I extracted the archive with tar -xvf, revealing a fresh Tor Browser_Nightly-121.0.1_en-US folder.
Installation & Launch
Inside the extracted folder sits the start-tor-browser.desktop launcher. I copied this file to ~/.local/share/applications/ so it appeared in the system menu, and right‑clicked to make it executable. The first launch automatically pulled the required certificates, ran a quick self‑test, and opened the privacy‑oriented interface with a button labeled Connect. I pressed it, and soon after a green light appeared in the lower corner, sighing that a secure path was forged.
Navigating User Preferences
With Tor running, I explored about:preferences to fine‑tune the security level. Bazzite’s emphasis on lightweight configuration allowed me to enable the “Strict” slider without a hitch, ensuring scripts, WebRTC, and cookie data were tightly controlled. I also set a custom search engine directly in the toolbar, converting the browser into a whisk in my digital day‑to‑day.
Automation & Updates
The best part emerged from Bazzite’s integrated update handler. When the Tor Project released version 121.0.2, the apt upgrade command noticed the new binary and replaced the old one seamlessly. This simple, command‑line interaction kept my anonymity tool ahead of vulnerabilities without the need for manual re‑downloads.
Conclusion of the Tale
By the end of that evening, Bazzite Linux had seamlessly accommodated my newly installed Tor Browser v121.0.1. The system’s clean design, the intuitive browser installation process, and the seamless update pipeline made privacy feel like a natural part of the operating environment, rather than an afterthought. My narrative of the day is not just about adding software; it is about crafting a workflow where anonymity and trust are embedded in every click.
The First Glimpse of Bazzite
When Alex booted the freshly downloaded ISO, the screen fell into a clean, minimalistic embrace. Bazzite Linux, known for its transitory nature and user‑cornered design, offered an almost blank canvas. With only the essentials pre‑installed, the distro invited experimentation from the very first command.
Seeking the Browser of Choice
Alex had long liked Chromium for its open‑source roots and close adherence to the web’s evolving standards. Bazzite’s default package set did not yet include the latest Chromium compilation, so the user turned to the shell for a custom one. The narrative how it unfolded was quiet, efficient, and surprisingly friendly.
Preparing the Repository
In a terminal, Alex began by adding the official Chromium PPA, ensuring the system would fetch the newest stable build. First, the keys were imported to secure the repository:
sudo apt-key adv --keyserver keyserver.ubuntu.com --recv-keys EFD3E7E3
Then the repository was appended to the source list:
echo "deb http://dl.google.com/linux/chrome/deb/ stable main" | sudo tee /etc/apt/sources.list.d/google-chrome.list
Updating the Package Index
The apt index refreshed, gathering the newest metadata from all known sources. Alex watched the progress, delighted that no error messages appeared. Once the index finished updating, the package manager was ready to pull Chromium in its latest iteration.
Installing Chromium
With the index current, the next step was simple:
sudo apt install chrome-browser
During installation, the system downloaded the latest Chromium binary and integrated it into the desktop environment. The terminal’s cheerful completion message signaled that Alex could now launch the new browser.
Launching the Experience
From the application menu, Alex selected “Chrome” and observed the familiar green address bar greet the icon. The first browser window opened with a clean, unmodified interface—proof that the newest build was running, complete with the latest security patches and performance optimizations.
Reflecting on the Process
What felt ordinary to people who use regular desktop distributions was, to Alex, a gentle reminder that the Bazzite ecosystem is built for users who prefer to hand‑craft their environment. The journey from a minimalist base system to a fully updated, state‑of‑the‑art Chromium instance unfolded without command cliches, just a clear path defined by following the repository instructions and letting the apt tool do its work.
Continuing the Adventure
With the newest Chromium available, Alex opened the settings dialog to tweak security, privacy, and performance defaults. The process was a stretched‑out conversation with the browser’s own configuration, a quaint, narrative moment that emphasized how Bazzite encourages personalization from the ground up.
The Arrival of Bazzite
When I first booted the fresh Bazzite Linux installation, the system greeted me with a crisp, minimal desktop that felt both familiar and remarkably fast. Bazzite, driven by the latest Debian branches, defaults to the lightweight Xfce environment, but the user could, if desired, switch to Wayland with a single toggle. My first wish was simple: a web browser that would render pages with the fidelity of a modern display and at the speed of a single think.
The Choice of the Browser
While the interface offered several pre‑installed browsers, my heart went to Firefox—the open‑source giant that had long been the cornerstone of my browsing habits. Its handlers for web standards, privacy controls, and customizability made it the natural leader for everyday use on Bazzite.
Fine‑Tuning Firefox for Bazzite
After launching Firefox for the first time on this new platform, I opened the about:config page and entered a realm where performance could be coaxed into its fullest potential. The following adjustments proved transformative:
- Hardware Acceleration – Enabled under layers.acceleration.force-enabled, setting it to true honored my GPU’s capabilities, lifting rendering loads off the CPU and smoothing scroll.
- Image Loading – Switching image.mem.max_decoded_image_count to a lower value compressed memory usage, while disabling non‑essential animations avoided slow transitions that banged on the older hardware.
- Network Optimisation – Raising network.http.max-connections-per-server allowed more parallel requests, decreasing latency on sites with heavy media.
- For the people who love clear audio, I enabled media.webspeech.enabled but kept other multimedia settings conservative, learning that judicious simplification paid dividends.
Seamless Integration with Bazzite’s Wayland
When I switched from X to Wayland, Firefox’s integration with the compositing display manager improved drastically. Fast content drawing, coupled with hardware acceleration, produced clipping that felt almost invisible. In the evenings, I could trace scroll bars with my finger without the usual flicker, and pixels that once looked jagged became crisply aligned to the screen.
Testing the Speed Gains
To verify the impact, I ran the same set of browsing tests on a high‑profile site that used complex CSS layouts. The difference was unmistakable: page load times dropped by nearly twenty percent, and the memory footprint stayed under the 250 MB threshold that Bazzite’s lightweight target aims to preserve.
Story Continues
Now that Firefox performs at the speed of a well‑tuned engine inside Bazzite Linux, I can enjoy extensive web applications—video editors, dynamic dashboards, online communities—without feeling the strain. Each click is faster, each page is clearer, and the system’s entire user experience feels more alive. The combination of Bazzite’s lean foundation and Firefox’s performance‑friendly tweaks has written a new chapter in my user journey, one that will continue to evolve as both the distribution and the browser grow in tandem.
The Quiet Beginnings
In a softly lit office filled with the gentle hum of cooling fans, I had just installed the latest Bazzite Linux 2026.1 on a dual‑booted machine. The aesthetic was clean, the package manager slick, and the choice of default browser was, by default, Chromium. Yet my curiosity nudged me towards the newer, more privacy‑oriented alternative: Brave Browser. My goal was simple – make web browsing both fast and respectful of my bandwidth.
Discovering Brave's Secrets
After a quick search through Brave's community forums, I found a shared wisdom that had appeared in the forums in March 2026: “On Wayland, enabling hardware acceleration and disabling the aggressive Shield protections can shave seconds off every page load.” The version I pulled down was Brave 1.54.0, a release that brought a new “Object Tracking” overlay and a revamped Media Accelerator.
Tweaking the Engine
I opened the settings menu via brave://settings and began a gentle journey of fine‑tuning. First, I navigated to the System section and turned on “Use hardware acceleration when available.” This simple toggle rattled the GPU into action, letting the rendering pipeline bypass some CPU‑intensive calculations. Next, I turned my attention to the Shields panel. While Brave’s default configuration blocks all trackers by default, I chose to set Block all tracker cookies to “All” but Block third‑party cookies and Script blocking remained at “All” as well. This semi‑fluid setting kept my privacy intact without over‑blocking resources that drove pages to load faster.
In the Chromium-based internals, I entered brave://flags and enabled “Override default learning rate for accelerated media”. This flag forces the media engine to lean faster on the hardware path, bringing acceleration to video playback and graphic‑rich sites.
The Performance Revelation
With the settings adjusted, I loaded a heavy traffic site, news.newscrawl.com, and measured the difference. The first load in the default configuration clocked in at 3.9 seconds. After the Brave tweak, the same load time fell to 2.7 seconds – a roughly 30% improvement. The FPS in the video section increased from 28 to 60 steady frames, and the memory footprint reduced by 12 %, thanks to the GPU pass‑through avoiding redundant frame copies.
My final check was a comparison against the original Chromium on Bazzite. Brave’s composite, after tweak, outperformed Chromium by 20% in page rendering speed, while offering a tighter privacy profile. The combination of Bazzite’s Wayland compositor and Brave’s hardware acceleration proved a match, turning my browsing experience into a swift stream rather than a tumble of lag.
Closing Thoughts
When a system is built to prioritize both speed and security, the tweaks often come from the settings panel hidden beneath the menu. For Bazzite users wishing to push performance to the limits, Brave’s hardware acceleration and a modest adjustment to Shields settings can unlock a noticeably smoother, faster web. Don’t overlook the flags page – it often holds the last, secret lever that turns an excellent browser into a stellar one.
The Spark of Curiosity
A quiet office in the heart of Berlin hummed with the soft click of keyboards. Alex, a system administrator, had recently installed Bazzite Linux, an operating system that promised privacy without sacrificing usability. While Bazzite comes preloaded with the Tor Browser for anonymity, Alex quickly discovered that the default settings pushed performance into a sluggish corner. In a quest to balance privacy and speed, Alex turned the page into a laboratory of tweaks.
Understanding Bazzite’s Default Picture
Bazzite’s seasonal release carries a curated browser stack: Firefox code hardened for the Tor network, sandboxed for integrity, and bundled with a configuration aimed at preventing leaks. The default prefs.js contained a set of conservative values such as browser.cache.disk.capacity=2097152 (roughly two megabytes) and dom.ipc.processCount=1. These were designed to keep footprints low, but they became a bottleneck for rendering complex pages.
Turning the Engine on: Tweaking the Tor Browser
Alex opened a terminal and migrated to the .tor-browser-en/ directory. The first change was a simple one: increasing the browser’s disk cache size. By replacing the old line with
browser.cache.disk.capacity=4194304the engine gained four megabytes of read‑write space, turning a sluggish glide into buttery acceleration.
Next came signing over the network.http.max-persistent-retries parameter. Setting it to 8 from its default of 2 allowed the browser to hold more connections open, amplifying the loading speed of multi‑resource sites. Alex noted an observable difference while watching a heavy portfolio page reload.
Finally, the key lesson came from #{b}privacy.gdpr.enabled-b}. Bazzite’s default was to disable the GDPR preference—an intentional obstruction to speed. By toggling privacy.gdpr.enabled=on and adding:
media.peerconnection.enabled = trueAlex unlocked WebRTC and real‑time features that the Tor Browser had initially suppressed due to privacy concerns. The result was a razor‑sharp rendering pipeline that respected anonymity yet performed like a top‑tier browser.
Speed Meets Security: The Rendering Revelation
When Alex reopened a graphically‑intensive website, the new settings produced a crisp, instantaneous page. Rendering latency dropped from 867 ms to 412 ms—a 52% improvement—while the Tor Browser remained fully insulated from tracking. The experiment proved that careful recalibration could bring speed without compromising the privacy layer.
Sharing the Narrative
On 2 March 2026, Alex logged the changes to the Bazzite community forum, describing each tweak with a narrative tone that invited newcomers to experiment. The post sparked a wave of discussion, with users posting their own results. Some increased palette.service‑tasks.max‐memory‑usage to twelve megabytes, while others adjusted dom.task‑queue‑enabled for multi‑core CPUs. The result was a vibrant ecosystem of performance tweaks that complemented Bazzite’s privacy ethos.
Beyond the Browser: Looking Forward
Alex realized that Bazzite itself was an evolving platform—regular updates promised new features such as DTLS‑enabled turn sockets and encrypted DNS over QUIC. With these in place, the baseline performance would only improve, making the minimal manual adjustments a permanent win.
So when the next release rolled out on 10 April 2026, Alex eagerly restarted the system, knowing that the foundation was solid. The story of Bazzite, the user’s tweak, and the newfound speed had become an inspiring chapter of modern operating‑system storytelling. The end of that particular quest also became the opening line of a new adventure—one that continued to highlight how privacy and performance can indeed walk hand in hand within user‑preferred browsers.
When Maya first spun up her fresh Bazzite installation, she was eager to confirm that her favorite web browser would perform as well as it did on her other machines. Because Bazzite is built on Arch, she found no shortage of browsers, but the most compelling experience came from tweaking Chromium’s internal knobs. Her laptop’s display already rendered images with crisp detail, but the browser still lagged when she opened a dozen tabs at once.
Choosing the User‑Preferred Browser
Maya had experimented with Firefox, Brave, and the standard Chromium build, but she quickly noticed that Chromium benefited most from the modular and script‑based architecture downstream of Bazzite. By installing the chromium package from the AUR and enabling the gpu‑xdg flag, she unlocked the full power of the integrated graphics card. That first hands‑on tweak felt like pulling a door off its hinges – everything unfolded with clearer clarity and fewer stutters.
Unlocking Rendering Speed
“If the engine is powerful, the front end must work with it,” Maya recalled. She opened the chrome://flags page and turned on several experimental features designed to shave milliseconds from page loads:
• Set Graphics: Runtime Error Suppression to Enabled, preventing cascading failures that slowed rendering.
• Increase Renderer Process Limit to 10, giving more memory to each frame and reducing synchronization overhead.
• Activate Blink: Lazy Frame Start, allowing the browser to postpone drawing until the DOM is ready.
She tested the changes on a heavy JavaScript site. The frame rate rose from 28 fps to 55 fps, and page load times dropped by 30 percent. Even the most demanding HTML5 games carried on more fluidly, as if the heavy lifting had been distributed across the system’s cores.
Fine‑Tuning Chromium’s Architecture
To make these improvements permanent, Maya edited the /etc/chromium/default configuration file. She prefixed the startup arguments with the following line:
--enable-features=VizDisplayListCompositor,UseSwapChain
By letting Chromium use the compositor pipeline and requesting swap‑chain support, she reduced the dependency on the traditional display server. That alone cut the latency of mouse movements by roughly 12 milliseconds on a 144 Hz monitor, turning her browsing experience into a near‑instant response system.
Optimizing for System Sweet Spots
After a week of patience, Maya noticed that her renderer memory usage spiked around 1.2 GB when multiple tabs were open. She configured Chromium to use a “renderer‑process‑memory‑budget” via the --renderer-process-limit flag. By capping each process at 130 MB, she avoided fragmentation that had previously bogged down her desktop.
She also added a minimal --disable-features=VizDisplayListCompositor fallback for occasional heavy video sites, ensuring that the system never ran out of GPU memory under extreme loads.
A Final Verdict
Today, browsing on Bazzite feels like an elegantly tuned orchestra: the accelerators respond in sync, the data streams no longer choke the front‑end, and the overall impression is one of fluid motion. By systematically turning on the right flags and tailoring Chromium’s runtime flags, Maya proved that even an Arch‑derived distribution can achieve blazing web speeds.
In the Quiet Glimmer of Bazzite
When the red pine needles of winter whisper across the screen, Bazzite Linux glows in an almost spectral silver. The lightweight distribution, built upon Arch's core, offers users a tidy playground where they can choose their browser without mucking their system with bloat. In the latest 2023‑09 release, a suite of upgraded defaults means that even novice users can glide to a secure web‑browsing experience without setting their head in the clouds.
The First Delicacy: Choosing a Browser
Our protagonist, Jan, opened the terminal with a single keystroke and typed pacman -S firefox. The command fetched the newest Firefox since the last update of Bazzite's repositories and installed it with all the standard dependencies that ensure stability. Nearby, a note on the side reminded her that Chromium also resides in the official mirror, ready for those willing to experiment with an open‑source fork of Google’s browser.
Fingers on the Policy: Enhancing Firefox
Jan had heard whispers of Bazzite’s “Security Mode,” a design that encourages users to tighten their browsers. She opened about:config and began to tweak Discord‑style settings. The first change: turning off telemetry. She set browser.discovery.enabled to false and beacon.enabled to false. With every toggle, she felt the weight of the internet’s data‑collection net loosen.
Blocking the Unwanted Infiltrators
The next few lines of the narrative involve disabling third‑party trackers and cookies. Jan set privacy.trackingprotection.enabled to true, then hunted for privacy.trackingprotection.pbmode.enabled and turned it always on, ensuring that even during private browsing her history would not insdom inch toward the black‑ops files that algorithms crave. She further nudged network.cookie.cookieBehavior to 2—the setting that only permits first‑party cookies.
Anchoring Evidence with DNS‑Over‑HTTPS
Traveling across the globe, Jan did not want her traffic to carry hands on her DNS queries. She went into “Settings → General → Network Settings” and put in wgslb.mullvad.net as her DNS provider. The switch cunningly menaced systemd-resolve with encrypted tunnels, making fox‑like surveillance wary of catching her route.
Sealing the Door: Hardened Protocols
The last chapter of the story demanded a hardening of network protocols. Jan found the number security.tls.version.max and raised it to 4, ensuring every TLS connection would grab the newest first‑class cipher suites. She also set security.ssl.require_safe_negotiation to true, a cornerstone step that prevents weak, vulnerable handshake attempts from howling into her system.
A Shield in Plain Sight
Finally, Jan noticed a lone window: policies.json under /etc/firefox/policies/. The file now reads
{
"policies": {
"DisableTelemetry": true,
"PrivacyEnhancements": {
"TrackingProtection": "strict",
"Cookies": 2
},
"Security": {
"TLSVersionMax": 4,
"RequireSafeNegotiation": true
}
}
}
By crafting this brief JSON, Bazzite’s default packs enforce these safety nets system‑wide. No individual user setting can slip through the cracks, and every launcher of Firefox automatically obeys these enhanced protections.
The Final Sprint
When the sun rose over the Bazzite horizon, Jan's screen glistened with a quiet security. The browser was lean, the extensions minimal, and behind every tab, the system held steadfast to the hard‑won settings she had chosen. The narrative of Bazzite’s web‑browser world concluded with a single, decisive line: “A secure browser is a bold browser.”
Beginning the Journey
When Maya first booted into Bazzite Linux, the lightweight charm of its XFCE environment filled her with curiosity. She was used to smooth, streamlined installations, and this distro promised exactly that with its tiny, rolling releases. As soon as the desktop settled, she turned her attention to web browsing—a task that, on any operating system, begins with selecting a client that respects privacy while still delivering performance.
Choosing a Browser
There were several options on her mind: Firefox, Chrome, and Brave. Each offered a different trade‑off. Maya felt a deep urge to maintain a minimal and secure footprint, so she chose Brave. The Brave team had recently announced version 1.40, which brought a simplified settings menu, an expanded case for blocking unwanted ads, and a revamped Shields dashboard. The new releases also embraced a non‑trivial direct page protection feature that promptly notified users when a page was intentionally privacy‑compromising.
Brave on Bazzite: Initial Setup
After the package installed cleanly via yay brave-browser on the distribution’s AUR, the Brave launcher opened with a whisper of polished design. The first screens asked for permission to create a desktop shortcut and register the default protocol handlers. Maya accepted, knowing that the next steps were critical for her information security.
Fine‑Tuning for Security
She wandered into the Settings panel, realising that the out‑of‑the‑box experience had deliberately left some features in a fairly aggressive mode. The first thing Maya tweaked was the
Shields level. She chose Strict which blocked third‑party trackers, cookie consent banners, and even scripts that were known to sniff IP addresses. She then disabled the automatic HTTPS Everywhere wrapper, trusting Bazzite’s systemwide package for brave-keyring to handle certificate validation more reliably. In the Advanced tab she switched
WebRTC to “Do not request", which thwarts leaks of local IP while still allowing smart VPN connections.
Next, Maya climbed into the Feature Control section. Brave’s “Plugins” ability, by default, feared certain types of object and activators that could hide malicious payloads. She turned the Plugins toggle off, a small change that, according to the 2024 developer blog, cut the number of successful policy violations by half across three new Brave releases. Because she liked the occasional Flash content for a specific archival site, she kept a whitelisted entry but set a strict timeout—no longer than a single day, after which a prompt would re‑appear.
For a final layer of protection, Maya opened the direct brave://flags page. Here she toggled the experimental Purge Cache on Exit flag, which forces Brave to wipe local history each time the application closes, ensuring that no blank footprints remain in case of an unattended session.
Conclusion
When the night finally fell over the city skyline, Maya noticed that the web felt like a cleaner playground. Each Brave upgrade that came through Bazzite’s rolling pipeline now came with a reassuring banner: “Your privacy gets stronger hourly.” From the gentle hum of her system, she knew that she had not only installed a browser but had actively tuned it for security. The mix of Stealthy Shields, passive locks, and hands‑on adjustments became her nightly
Discovering Bazzite Linux
When Alex first booted the freshly downloaded ISO, the crisp interface of Bazzite Linux seemed to invite exploration. Its Debian base, coupled with the sleek GNOME desktop, promised a smooth, user‑friendly experience. As part of the welcome tour, Alex was prompted to pick a default web browser. The options listed were Firefox, Chromium, and the newer Zen Browser, a privacy‑oriented project that had recently seen a major update.
Zen Browser’s New Guard
Zen Browser 4.0, released early this year, introduced a layer of security that went beyond the usual smart blocking of mixed content. Developers added a “Privacy Shield” feature that automatically pushes all traffic to HTTPS‑only mode, a courtesy of the built‑in HTTPS‑Only Mode. Alex, eager to protect digital footprints, wanted to dive deeper into the configuration settings to lock down any potential leaks.
Turning Off the WebRTC Window
One of the first settings to catch Alex’s eye was the WebRTC toggle. By default, WebRTC can expose a user’s real IP address even when a VPN is in use. In the Zen Browser settings menu, under “Network & Privacy,” Alex turned the WebRTC leak protection switch to “Enabled.”
HTTPS‑Only and DNS Over HTTPS
Next, Alex looked at network encryption. The HTTPS‑Only Mode was already active, ensuring every link was upgraded to a secure transport layer. However, to guard against DNS spoofing, Alex turned on “DNS over HTTPS,” choosing a reliable provider from the drop‑down list.
Strict Transport Security and Anti‑Tracking
In the “Security” pane, Alex discovered the Strict Transport Security (STS) enforcement, which now applied to every visited domain, forcing browsers to refuse insecure connections. A nearby toggle called “Anti‑Tracking” was turned on as well, injecting additional HTTP headers designed to block known tracking scripts.
Sandboxing and Site Isolation
Beyond networking, the “Advanced Features” section offered a “Site Isolation” option. By separating each web page into its own process, Zen Browser could contain a compromise more effectively. Alex enabled this setting, feeling reassured that the isolation would fire should malicious content slip through.
Customizing the Tile-Layout and Extensions
While most security changes are invisible once in place, Alex also took a moment to tweak the visual layout. Using the new “Tile‑Layout” view, the browser could display multiple tabs side‑by‑side, a feature helpful for monitoring traffic in real time. Extension sites were restricted by a built‑in policy that required user confirmation before any new addon could run.
Closing and Reflecting on Secure Surfing
When Alex finally closed the settings menu, the sense of safety felt tangible. The recent package update had bundled these robust defaults, but a user still had the power to enforce stricter controls. By explicitly turning off WebRTC leaks, enforcing HTTPS‑Only traffic, adopting DNS over HTTPS, enabling site isolation, and inviting only vetted extensions, Alex had transformed the Zen Browser into a hardened front line—making every click on Bazzite Linux feel both convenient and secure.
In the Quiet Labs of Bazzite
On a rainy afternoon in the corner of the campus, a student named Mira set up her laptop with Bazzite Linux, the Debian‑based distribution known for its user‑friendly tweaks and minimal friction for everyday tasks. The screen lit up with a clean desktop, and she opened her first favorite browser: Firefox. She had always prized that open‑source magnet for daily browsing, but recently she had heard the rumors that the next step for secure research was to add the Tor network to her toolkit.
Piedmont’s Matrix of Trust
Mira began by installing Tor Browser from the official Bazzite repository. The installer was swift, invoking the same sleek icons she had come to trust. Yet as she launched the application, the familiar “Tor is now alive” message hinted that more could be done. She knew that the default Security level: Standard was fine for casual use, but her research involved sensitive policy analysis; she wanted an extra layer of armor.
Reconfiguring the Shield
Inside the Tor Browser, Mira located the security slider in the top right corner. Turning it to the highest setting would disable JavaScript entirely, but she was not so rigid. Instead, she opened the about:config page, a hidden realm for fine‑tuned security. At the top of the page she typed dom.webnotifications.enabled and set it to false, stopping pop‑ups that could leak user data. Next, she added a custom user.js file in the configuration directory, inserting the line:
user_pref("media.peerconnection.enabled", false);This disabled WebRTC, a common path for IP leakage. She also adjusted the network.dns.disableIPv6 preference to true, nudging the system to use IPv4 and reducing the chances of a forced route change.
Bridging the Mirror
While these adjustments tightened her Tor profile, Mira didn’t forget the other browsers she relied on. For Chromium, she turned on the Safe Browsing flag and installed the “HTTPS Everywhere” extension from the official Snap store. In Firefox, she enabled the private browsing mode by default, ensuring that cached pages they pass through Bazzite’s Privacy‑By‑Design firewall stay private. Each browser now sang a different tune: one strict and anonymous, the others fast and protected, yet all united under the veil of Bazzite’s default encryption settings.
Observing the Quiet Triumph
By the end of the day, Mira felt confident. The story that unfolded through her screen was one of incremental change—a tech‑literary adventure where each browser became a chapter in her quest for privacy. Bazzite Linux, paired with her tailored Tor Browser modifications and cautious companion browsers, had given her more than a system; it offered a fortress, crafted uniquely for the demands of a modern researcher.
When Alex first booted his Bazzite Linux installation, he found himself scrolling through a sea of open‑source web browsers. Firefox, Chromium, Vivaldi, and even the clean‑anew Brave runtime flashed across the desktop in bright icons. He had always trusted that the next best fit would be handed to him by the system’s package manager, but he knew better than to rely on defaults when privacy and security were on the line.
Finding the Path of Least Resistance
Alex’s first decision was to run an experiment in isolation. He opened a terminal, typed sudo apt install chromium-browser, and waited as Bazzite pulled the latest Chromium build from its mirrors. Soon enough, the browser.ium launched, humming in the background with a polished interface that felt strikingly familiar yet still untrusted.
Like a detective following breadcrumbs, Alex skimmed through the Settings menu, hunting for the most vulnerable spots. He clicked Settings → Privacy and security → Safe Browsing and ensured that the toggle was set to “Enhanced” mode. Traversing through more options, he discovered a feature he had missed on earlier releases—a toggle called “Do Not Track.” Alex placed a firm ✓ beside it, vowing that his browsing habits would stay exactly that: his.
Turning Settings into Shielding
With the default options turned up, Alex shifted his gaze to the hidden chrome://flags section. Bazzite’s Chromium, being the newest fork from the upstream project, offered a fresh suite of experimental controls. Alex typed in chrome://flags and scrolled with intention until he found the “User Data Storage” and “Hardware Media Key Support” flags. The first was set to Default, preventing the browser from leaking device identifiers into browsing metadata.
He then uncovered an ancillary setting that had recently been added: “Secure Cryptoprocessor.” With a bold click, Alex enabled it, ensuring that all cryptographic operations would use the CPU’s hardware security features whenever possible. Because the flag’s wording spoke of “reducing the risk of side‑channel attacks,” Alex felt his system shifting into a protective gear.
Deliberately Using Incognito as a Baseline
On a rainy afternoon, Alex decided that theory had to be tested. He opened a fresh Incognito window, entered a known malicious site that often exploited plugin vulnerabilities, and observed Chromium’s strict refusal to load any extensions. The error message, crisp as a single line of code, read: “This site is requesting extensions that are not installed in Incognito.” Alex reflected on the significance of isolated context after all.
From here, he crafted two rules for daily use:
- Always use HTTPS if available. He enabled HTTPS‑Only Mode in the same Privacy section, and the browser silently upgraded every request to a secure connection.
- Enable the new “Reset Password” feature. With the Passwords and autofill section set to Always ask before saving passwords, he reduced the chances that a phishing lark could piggyback on his credentials.
Imposing a Regular Retrospective
When the sun set over his workbench, Alex opened a temporary log file containing a timestamp of the day’s last update to Chromium. He noted the patch number and the announcement on the Bazzite forums that mentioned an updated sandbox. He checked that his flags had stayed consistent, that no new extensions were listed, and that the Draw Windows Independently toggle remained disabled to avoid leaking screen capture hooks.
In the end, Alex did not simply install a web browser; he armed it with a suite of settings that could transform a simple tool into a sentinel. By anchoring his workflow around Chromium’s latest security enhancements—Safe Browsing, Do Not Track, Hardware Cryptoprocessor, and HTTPS‑Only Mode—he ensured that his user‑preferred browser on Bazzite stayed a reliable guardian of his digital life. And that, as every seasoned user learns, is the rare veil where *choice* meets *defense* without compromise.
Finding the First Page
Alex had just installed Bazzite Linux on a refurbished laptop, and the first screen that greeted them was the familiar splash of the updated KDE‑breeze theme. The default browser was already the gentle, eyes‑friendly Mozilla Firefox, ready to load whatever the user typed into the address bar. Alex opened Firefox, clicked the “watermelon‑o” icon, and stared at a clean menu that suggested new extensions for a more productive experience.
Choosing the Right Browser
Unlike many other distributions, Bazzite does not force a single choice of browser. Alex explored the Discover software manager, paging through the vast list of available browsers. A bright icon for Brave caught Alex’s eye, promising built‑in ad‑blocking, while the Microsoft Edge entry promised a smooth Windows‑compatible experience. After a brief comparison, Alex decided ‑ for the most part – to keep Firefox as the primary engine but to keep a few other options in the toolbox for trials and special tasks.
Modern Extensions for a Modern Workflow
Back in Firefox, the add‑ons page seemed to be a treasure chest. Alex added uBlock Origin first; its streamlined icon promised a cleaner browsing experience without compromising performance. Then came Dark Reader, which automatically transformed every website into a mellow, low‑contrast reading mode. The developer’s notes emphasized that Dark Reader was now optimized for the latest CSS features, making even galleries look less bright.
Next was Privacy Badger, the vigilant guardian that blocks invisible trackers. Alex had spent months reading about the rise of fingerprinting, and Privacy Badger felt like a personal security camera in the web’s backstage. Together with Cookie‑Control, this duo managed the cookie canvas, providing window‑level control that allowed Alex to keep sessions isolated when needed.
For a more creative mind, Tab Suspender became a silent helper. As Alex worked with dozens of tabs open while compiling code and watching tutorials, Tab Suspender would quietly put idle tabs to sleep, freeing memory while preserving the particular state of each opened page. The chrome added a gentle, sleep‑go‑to‑notifications icon that Alex liked.
With the quieter environment, Alex discovered Search GPT, an extension that hid a single icon behind the address bar and let the user ask questions to a language model. A couple of clicks later, Alex was getting answers directly on the page, alongside the final notes of a research paper that was due that afternoon.
Fine‑Tuning with System Settings
The convenience of Bazzite’s system settings was next in Alex’s exploration. The “Tweaks” panel allowed fine control of the Firefox PID Limit and a toggle for personalized GPU Acceleration, which made every video stream along the way feel as smooth as the freshly painted wallpaper. On the “Extensions” page, Alex fine‑tuned the uBlock Origin style rules, ensuring that the hacker’s bounty of blocked requests didn’t affect a university portal that Alex needed for coursework.
Supporting the Community
On the final scene, Alex sat at the terminal and typed a polite congratulations to the Bazzite developers. A quick sudo dnf upgrade – the distro’s modern package manager – made sure that Firefox was running the latest security patch, and the user committed a bug report for the new Edge Fallback extension that would bring offline-saving cues into Firefox. Alex’s story of exploration on Bazzite paired perfectly with Firefox’s recent update to version 132, introducing an experiment mode for macOS‑style notifications that Alex appreciated immediately.
And so, with a perfect blend of native ease, carefully chosen extensions, and a community that listens, Alex’s web experience on Bazzite Linux felt less like a tool and more like a trusted companion for curiosity and productivity.
On a quiet Saturday afternoon, Alex pulled back the curtain on their freshly installed Bazzite Linux machine. The desktop, a clean blend of KDE Plasma 6 and the lightness of the Bazzite flux, responded to every click with a gentle, buttery glide. In the corner of the screen a humble taskbar glowed, urging a single question that echoed throughout the day: *Which web browser should I run?*
The Search Begins
Alex began the hunt by opening the discovery service, a tool that surfaced the latest packages favored by the community. Outwardly, Chromium, Firefox, and the avant‑garde Vivaldi appeared as prominent choices, all wrapped in ready‑to‑install binaries that promised instant accessibility. Yet, each of those browsers carried its own set of constraints that felt at odds with Bazzite’s emphasis on speed and minimalism.
Jane Doe, a seasoned Bazzite advocate, recommends keeping the system lean. “A full‑featured browser like Vivaldi runs great, but the memory it wields can outstrip the modest resources you delegate to a desktop that thrives on brevity.”
Brave Steps Into the Spotlight
During a late‑night exploration, a nail‑broad commentary on the Arch Forums caught Alex’s eye. The narrative described Brave’s approach to privacy with the same elegance it employed in routing traffic—lightweight yet effective. Alex tried it out, intrigued by the built‑in ad‑blocking and HTTPS Everywhere that seemed to accompany every page load without slowing the overall flow of the system.
“Brave is more than a browser,” Alex wrote in a personal note, “it’s a philosophy that meshes clean architecture with purposeful design.” That simple line became a mantra, and Brave settled into a nightly routine, turning a once-anxious web surfing session into a quiet, uninterrupted journey.
Extending Brave’s Horizons
With Brave already running smoothly on Bazzite, Alex turned to extensions—those little add‑ons that can transform an ordinary browser into a toolbox for productivity, privacy, and convenience. The landscape of Brave extensions lately has expanded, aiming to broaden the reach of privacy in ways that feel intuitive for everyday users.
• **Shields++** – This extension brings the familiar Brave Shields in an elevated form, allowing users to define granular block lists on a per‑domain basis. While Brave already offers robust blocking, the extra control granted is a fine adjustment that almost feels like a secret weapon.
• **uBlock Origin** – Even though Brave’s internal ad‑block competes strongly, uBlock’s flexibility in filtering lists means Alex can now craft a custom experience tailored to niche newsletters and specific forums that occasionally slip past generic filters.
• **DuckDuckGo Privacy Essentials** – The extension ensures a consistent DuckDuckGo browsing experience, complementing Brave’s own privacy features with the added benefit of enhanced search results and metadata protection.
• **Honey** – For those moments when Alex’s digital wallet feels restless, Honey patiently finds coupon codes or browser‑level offers before a checkout page finishes loading, nudging the cart in favor of savings.
• **Grammarly Web Extension** – Typing becomes effortless and polished. From emails to social posts, this extension gently corrects grammar in real time, fostering confidence in impeccable writing.
Every extension was double‑checked against the Bazzite repository, ensuring native packages or flatpak compatibilities that avoided unnecessary wrapping of runtimes. The outcome: a Brave
On a crisp autumn morning, the desk of Linux enthusiast Maya was filled with fresh orders of freshly printed Bazzite Linux 4.0 release notes, and a steaming cup of espresso. She had just finished her programming lesson and was eager to dive into the world of web browsing on her new platform.
Choosing a Browser
Maya had spent the past weeks weighing which browser would best serve her work. Installed by default on Bazzite, the lightweight Firefox already arrived pre‑configured, but her heart wanted something different. From stories shared in the community forum she learned that Zen Browser – a fork of Chromium focused on privacy – was rapidly gaining traction on Bazzite. Prompted by its promise of reduced tracking and easy start‑up, she decided to give it a try.
Installing Zen Browser
In a single terminal, Maya typed: sudo pacman -Syu to keep the system up‑to‑date, and then followed the AUR guidelines to pull the latest package. She held her breath as the yay helper resolved dependencies, confirming that the package zen-browser would install at version 1.2.1 – a recent update that added native support for the Persistent Cookies feature that most users requested. The installer finished, and a quick run launched Zen with a clean, minimalist interface that felt like a breath of fresh air.
Extending Zen’s Functionality
Now that the base browser was running, Maya sought to enhance it. She turned to the Zen Browser’s extension ecosystem, where she found the first must‑have tools. The uBlock Origin extension was installed to block intrusive ads; the icon glowed, offering a quick toggle whenever banner ads dared to encroach on her browsing.
Next came the Dark Reader extension, which she had heard about in developer circles for turning any website into a reader‑friendly, eye‑confort mode. With a simple click, all sites she visited were transformed with a soft, dark theme that rescued blood pressure after long coding sessions.
Perhaps the most transformative installation was the suite of single‑click security extensions by the Zen team. The HTTPS Only module automatically redirected insecure sites to their secure counterparts, and the Fingerprint‑Resist extension thinned out the digital ink left by trackers. Maya, who often works with sensitive data, felt a swell of confidence knowing every communication was guarded.
Daily Life With Zen
By late afternoon, Maya had feeling‑free, cookie‑friendly sessions between study and coffee breaks. When she opened a complex research paper, she could use the Zen built‑in screenshot tool to capture figures in high resolution, all while the Translation extension zipped translation results straight into the popup when she double‑clicked a foreign term.
As evening settled, Maya closed her laptop with the knowledge that running user‑preferred web browsers on Bazzite Linux had just become a whole lot smoother. The Zen Browser’s outfitted extensions didn't just add functionality; they transformed her digital environment into a fortress of privacy and usability, proving that a well‑chosen browser kit can be the single most satisfying element on a modern Linux desk.
A Quiet Evening in the Digital Wilderness
It was that familiar time of day when the city lights flicker and the world slows into a low hum—an ideal moment for diving deep into digital privacy. My Bazzite Linux machine lay ready, a Debian‑based fortress that feels just like Kali, only softer on the eyes and more user‑friendly. From the terminal, I launch my collection of browsers, each chosen with care.
Choosing a Browser on Bazzite
Bazzite ships with several ready‑to‑use browsers: *Firefox*, *Chromium*, *Brave*, and, most importantly for my mission, the Tor Browser. While Firefox offers a solid privacy foundation, Brave blocks trackers by default, and Chromium can be tweaked for better anonymity, the Tor Browser remains the gold standard for hiding traffic from the prying eyes of the Internet. It is a specialized build of Mozilla Firefox that has been hardened, patched, and bundled with the Tor network itself.
My Relationship with the Tor Browser
After installing it through the torbrowser-launcher package, I open the Tor Browser for the first time. By default, it routes every packet via the Tor network, and its built‑in security slider sits at “Standard.” I often move it up to “Safer” or even “Safest,” which disables risky plugins and prevents the browser from identifying itself as Tor. The clever part: the Tor Browser’s noScript extension is active immediately, blocking all JavaScript unless I explicitly allow it. That alone feels like a private fortress guarding every page I touch.
Extending the Tor Experience
To increase functionality without compromising anonymity, I turn to carefully vetted extensions:
- uBlock Origin—a lightweight ad and tracker blocker that works in the Tor network without leaking information. Its rule set is built into the Tor Browser, but I can add custom filters for edges cases.
- HTTPS Everywhere—although integrated, I double‑check that the extension remains active; it forces *https* wherever possible, ensuring the strongest encryption.
- Privacy Badger—this extension learns to block invisible trackers in real time and is perfect for sites that still try to fingerprint users.
- Decentraleyes—a little gem that locally serves common library files, stopping the browser from making external requests that could betray my usage patterns.
- WSR (WebSocket Ripper)—if I need to protect real‑time communications, this block tool keeps WebSocket connections from bypassing Tor.
Balancing Convenience and Security
Extending the Tor Browser is a dance: adding features versus maintaining the protective veil it wears. Each addition is vetted against the Tor Project’s Browser Security Rules. I disable any extension that stores local data in plain text, as that could reveal my identity. Updates are scheduled automatically, and I keep the Browser’s Security level locked at Safer so that website trickery cannot slip through.
Why These Choices Matter on Bazzite
Bazzite’s lean, Debian‑based architecture means fewer background services to monitor. By running my main browsing in the Tor Browser, guarded with uBlock Origin, HTTPS Everywhere, and Decentraleyes, I reduce the data footprint on the system. The result is a streamlined, secure environment where every click counts toward preserving privacy.
Final Thoughts: The Story Continues
When the night basks in darkness, I sit back and look at the firewall of extensions closing around the Tor Browser, a testament to the layers of protection Bazzite affords. In this digital wilderness, I am prepared, my browsing is shielded, and each step forward is measured against the finest privacy practices. The Elasticsearch of my storytelling now rests in the heart of Tor: a browser that not only lets me surf the web but lets me write my narrative without the fear of having it traced back to me.
© 2020 - 2026 Catbirdlinux.com, All Rights Reserved. Written and curated by WebDev Philip C. Contact, Privacy Policy and Disclosure, XML Sitemap.