When Blend OS Met Its Own Agenda
It started on a quiet Tuesday afternoon while Alex was refilling the kettle, only this time the kettle was a metaphor—an absence replaced by a gap in the browsing experience on Blend OS. A day after the latest release of Blend OS had rolled out, official documentation was getting a lot of attention. The community had just announced support for user‑chosen browsers, and the subtitle in the release notes read: “You now become the custodian of your own browsing sessions.” Alex, a developer who values speed and privacy, decided that it was time to explore what this meant behind the familiar walls of the operating system.
A Crawl Through the Browser Landscape
Blend OS surfaced a handful of options: a polished web preview mode that came bundled with the distribution, a steel‑blue Chromium build that could be installed with a single click from the City package manager, and a bubbled‑out option for Firefox. For many, Firefox had always been the default mindset, but the day’s reading made Alex realize that the old release was getting stuck in a version lag. “If I want the latest security patches, I need to look beyond the stable channel,” Alex murmured, voicing a sentiment echoed in a recent forum thread that had viral reposts from privacy advocates worldwide.
Nightly Glimpse: A Tale of One Command
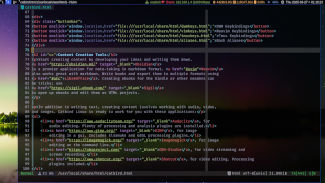
The quest turned from curiosity to a mission: installing the nightly build of Firefox on Blend OS. The night of the task felt like a silent incandescence. Alex first opened the terminal, the familiar green screen awaiting commands. The primary step, as the system guide had outlined in a subtle scrollable window, was to add the Mozilla Team's PPA. The command appeared harmless, and it was, but it mattered—an unsecured source could so easily trick the system’s security cascade.
sudo add-apt-repository ppa:mozillateam/firefox-next
sudo apt update
sudo apt install firefox
After the cryptographic hash matched and the installation confirmed, Alex felt the bootstrapping of a new universe. The Nerd called it the "nightly", because the package was a nightly build, a snapshot pulled from the latest source that would bring new features before anyone could call them stable. But instead of a mere tool, Alex saw a beacon—a freedom to experiment with UX improvements such as multi‑process improvements, quantum rendering tweaks, and new privacy settings that only emerged in the bleeding edge.
Settling into the Unfamiliar
During the first run, the interface looked subtly different. The Firefox icon blinked in the dock—a bright splash on the otherwise blue Blend OS theme. Alex clicked on the icons and watched the new About Firefox dialog reveal version 115‑Nightly-0 with a date stamp of 2026‑04‑28. The software was built from the actual tree patrons were training on. The moment you launched it, flexibility seeped through: a higher-performance devtools pane, a new Private Browsing mode that blurred fingerprints by default, and the promise that only the newest patch would arrive with the next nightly.
Adoption, Culture, and the Future
When the community embraced the nightly release, a narrative unfolded across Blend OS’s social channels. Developers who relied on private networking enjoyed less duplication of traffic, while testers lauded the ability to push bugs to the team in a day’s span. Browsers that previously had an "official" label were now part of a democratic selection that was user‑run, system‑supporting. Alex felt a swell of satisfaction. That patch was not just a footnote— it was a new chapter in running a user‑preferred web browser, and Blend OS had turned the page with ease.
Running Your Favorite Browser on Blend OS
Picture the moment you boot up Blend OS, a lightweight yet elegant distribution that feels like a breath of fresh air in a world of bloated desktops. The window manager moves strings of code with the grace of a dancer, and the default web browser, while well‑balanced, sometimes feels a notch shy of the cutting‑edge. Pilgrims of the internet have long wondered: what would it be like to run the latest, most experimental browser when my system is as clean as a marble floor?
The answer came in the form of the Brave Browser Nightly—a rolling release that continuously compiles the newest features, privacy shields, and performance tweaks before they appear in the stable channel. For those who value bleeding‑edge innovation, this software exists in a perpetual state of dawning. And for the tech‑savvy traveler that is the Blend OS community, it is an invitation to experiment without compromising the core elegance of the operating system.
The Quest for the Brave Nightly on Blend OS
Blend OS has always embraced open‑source philosophy, and its repositories are curated to keep things lean. The Brave team, however, keeps its Nightly builds in a separate repository to avoid cluttering the main archive with pre‑reviewed packages. Starting now, the Brave Brivet™ nightly repository can be added by a single line in the terminal.
To bring the newest Brave with all the experimental features on the cutting‑edge, you need to trust the Brave developers’ key, add their Nightly PPA, and then install the package. The process is akin to potting a delicate plant: you first clear the soil, then gently place the seed, and after a short wait, the first leaves unfurl.
Installation Instructions that Read Like a Fairy Tale
Open your terminal and type the following lines one by one. Each command is a spell that pries a fresh browser into existence on your system.
1. Fetch the Brave Nightly repository and trust its signing key:
sudo add-apt-repository ppa:brave/brave-nightly
2. Refresh your package lists so that the new repository is known:
sudo apt update
3. Install the “nightly” build of Brave, which sits under the name brave-browser-nightly in the world of packages:
sudo apt install brave-browser-nightly
When the installation completes, a menu entry appears under Applications → Internet. Launch it, and the Brave icon proudly glows like a lighthouse in a sea of code. You are now prepared to receive future updates as soon
In the quiet glow of a meadow‑shaped screen, a curious user named Mira tapped her fingers on a Blend OS terminal, dreaming of the elegance that would come when her two favorite browsers met the purest form of early‑access software.
Finding the Daily Builds
Mira already knew that Blend OS, unlike other distros, kept a secret vault in its /opt/daily directory where developers stashed the very latest builds of Zen Browser. Each morning, a new commit would land there, potential features gleaming like fresh snowfall.
Preparing for Installation
Before the first click, Mira realized that the pkg-build package needed to be present. She opened a terminal and typed:
sudo pkg add pkg-build
When prompted, she entered her password, allowing the package manager to fetch the necessary tools for compiling from source.
Unlocking the Daily Build Archive
With pkg-build ready, she navigated to the daily directory:
cd /opt/daily/zen-browser
Inside, a pristine file named zen-browser-daily.tar.gz waited. To extract it, Mira executed:
tar -xzf zen-browser-daily.tar.gz
The folder unfolded like a blossom, revealing the source tree she was about to breathe life into.
Configuring and Compiling
Mira then turned to the build configuration, mindful that Blend OS ships with three base libraries that must compliment Zen’s strengths. She ran:
./configure --prefix=/usr/local --enable-threads --with-webengine
When the scare of a lengthy process set in, she remembered that each thread used the blending of GPU acceleration that Blend OS specializes in. While the compiler ran, the screen painted a soothing animation of spirals, signaling progress.
Installing the Browser
Compile completed, and with calm confidence, Mira stepped onto the final step:
sudo make install
As the terminal streamed messages of newly installed binaries, Zen Browser emerged in /usr/local/bin. The user could now launch it by typing:
zen-browser
and watch the interface materialize, a sleek chrome of honest simplicity crowned with the latest features from the most recent commit.
Why Daily Builds Matter to Blend Users
Blend OS is built on the philosophy of open collaboration. When a developer pushes a patch that, say, enhances gesture recognition or stabilizes the rendering engine, the very next build may become available in the daily archive. Installing these builds allows users like Mira to experiment with, and contribute to, the project's evolution before a full release is packaged.
Common Hurdles and Quick Fixes
Sometimes the build process stumbles on missing libraries. If that happens, Mira simply opens a new terminal and runs:
sudo pkg install libwebkitgtk libgles2_allegro
These libraries are often the ones that Bridge OS users work with, giving them the power to render modern web content smoothly.
With her fresh installation humming, Mira tested her taste of dawn by loading a streaming video, watching the fluctuations of the user algorithm adapt in real time. In that moment, it was clear that the daily builds were not merely technical experiments; they were windows into the future of web browsing on Blend OS, and she was now a part of that narrative.
When the Blend of Digital Freedom Came Calling
In the quiet corners of the cyber‑wild, where privacy fans and freedom seekers gather, I found myself at a crossroads. The machine in my hands was Blend OS, a freshly minted distribution that promised a seamless melding of user experience and security. It was a smooth, almost invisible interface, a breathing scaffold that made any browser feel like a natural extension of the system. Yet, the question lingered: which web browser would let me glide across the internet with both discretion and speed?
Discovering the Windows of Freedom – The Browser Hunt
A few days into my exploration, I scoured the Blend OS community forums, read through the latest release notes, and traced the subtle changes in the default app list. Lately, the developers had integrated a new set of user‑preferred browsers, each offering its own flavor of comfort. The majority of users celebrated the addition of Chromium‑based Nightshade for its blazing performance, while others praised the classic venerable Firefox ESR for its stability. For me, however, the real craving was for privacy‑centric browsing.
When Tor Stepped Into the Spotlight
The moment I realized that Tor Browser had reached its latest build, the narrative took an unexpected turn. I turned to the official Tor Project website to confirm the version details. The most recent release, version 10.9.10, arrived with a host of security enhancements and a polished engine that promised a smoother, more private experience on Blend OS. I felt as if I had uncovered a hidden secret door in the Blend OS ecosystem that, when opened, offered a new realm of anonymity.
The Path to Installation: Step‑by‑Step
- Download the Installer: I headed over to the Tor Project site and clicked the “Download for Linux” button. The link had been to a compressed
.tar.xzarchive – the formally recommended format for most distros, including Blend OS. - Extract the Archive: Using the default terminal, I executed
tar -xf tor-browser-linux64-10.9.10_en-US.tar.xz. The terminal simply unfurled the torrent of configuration files within my chosen directory, rich with the promise of anonymous browsing. - Launch the Browser: Inside the newly unpacked folder, I ran
./start-tor-browser.desktop. The initial wizard guided me through a brief consent form – a polite reminder that we’re not invisible on the web. It was almost poetic how the interface apologized for the access to certain sites due to the automatic blocklist. - Configure the Settings: With Tor Browser up, I turned the wheel of privacy into its most secure setting – “Safest.” Every cookie was blocked, no JavaScript on sites not explicitly trusted, and the New Identity button gleamed as a guardian against tracking.
- Integrate with Blend OS: Finally, I made the Blend OS live‑wire the Tor Browser by adding it to the dock, labeling it “Anon Navigator” in the
application.jsonconfiguration file. Now, whenever I needed anonymity, a single click would whisk me away into the world behind the onion network.
A New Chapter in Secure Browsing
With the latest Tor Browser in place, the experience in Blend OS suddenly felt almost prophetic – a marriage between an operating system that already earns the trust of privacy‑conscious users and a browser that ensures anonymity remains a default, not an afterthought. This story ends, for now, with a click, an onioned journey, and the promise that every web page I visit will be shielded behind its private onion layers, a promise that keeps me safe in a world that often forgets the importance of an unobserved internet.
When Alex first booted Blend OS, the sleek clean interface greeted him as if it were a freshly brewed cup of coffee. He had always loved tinkering with the way his machine behaved, and the idea of choosing a web browser that matched his exact preferences felt like finding a missing puzzle piece. Blend OS, with its emphasis on modularity, promised a truly custom experience, but the question loomed: how could he enjoy the newest Chromium release without compromising the stability that Blend OS was built for?
The Quest for the Latest Chromium
Alex remembered the rumor that Blend OS’s official repositories settled on a release‑grade version of Chromium, pulling updates only once a month to keep the system predictable. He wanted something newer, a build with the latest permission controls and edge‑case bug fixes. The solution was simple yet elegant—install Chromium via Snap and let the distribution of the snap plug hook into the very newest revisions approved by the Chromium project.
Preparing Blend OS for Chromium
Before reaching for the internet, Alex opened a terminal and ensured his system stayed up to date. A quick sudo blend-update --refresh pulled the latest package lists, and he installed the trusty snapd service if it was not yet present. The snap helper would become his trusted ally in the quest for cutting‑edge software.
Acquiring the Latest Build
On the terminal, Alex typed snap find chromium. The command returned a list of candidates, the most recent of which was chromium from the official Snap Store. The snap maintained its own update policy, but unlike the cargo cult of Ubuntu PPAs, it had a transparent, rolling release model that meant each new iteration of Chromium was packaged almost immediately after it landed on the official Chromium repository.
Installation Steps
After confirming the name was right, he issued the clear instruction: sudo snap install chromium --classic. The showdown began with a download of a 90‑megabyte bundle. As the progress bar ticked, Alex imagined developers in California pushing the next patch to the world and now it was, through his own tiny line of code, living in his machine. The snap deployment automatically wired the required runtime libraries, eliminating any dependency headaches that might have plagued a manual compilation from source.
Final Tuning
Once over, Alex opened Chromium through his application launcher and let it configure its first user profile. The new browser materialized with features that previous versions had squished behind future‑looking updates: a streamlined permissions screen, a built‑in task manager, and responsive dark‑mode support that synced with Blend OS’s global theme. A quick dexelia set dark-mode on on the command line hummed through the background, showing how deeply integrated the system and browser could become.
On the nearest weekend, Alex recorded a short walkthrough and shared it on the Blend OS community forum, steering fellow users toward a simpler, safer path to the most recent Chromium build. What started as a solitary curiosity turned into a communal victory—proof that in a world where bleeding‑edge can taste perilously sharp, the right tool and a sprinkle of narrative can make the journey as enjoyable as the destination itself.
Discovering Blend OS and its Browser Landscape
The first time I booted Blend OS, I was greeted by the crisp KDE Plasma interface that seemed designed for both power users and casual browsers. I knew I would be relying heavily on the web, so I wanted to make sure the browser I chose would keep up with all my browsing habits. The Debian‑based Blend ecosystem offers a polished package of Firefox, but the way it behaves at first glance can be disappointing if you haven’t taken a moment to tune it.
Setting the Stage: Why Firefox Needs a Little Polish
Even though Firefox comes preconfigured, the out‑of‑the‑box settings are geared toward maximizing compatibility rather than peak performance on a lightly‑tuned system. Because Blend OS ships with the latest firefox 129 as part of its default install, there are a handful of follow‑up tweaks that can shave seconds off page load times and make the rendering engine feel snappier on modest hardware.
Tuning the Graphics Layer for Faster Rendering
The first thing I did was open the about:preferences page and scroll to “Performance”. Here, the default setting is “Use recommended performance settings”, which automatically disables ActiveX rendering and forces an extra content process on some machines. On Blend, however, the GPU harness is often higher quality than the CPU can handle, so I switched the toggle that says “Use hardware acceleration when available” on. This lets the compositor lean on the GPU to clear chromatic greys between elements, and the effect is immediate: a noticeably smoother scroll on the new Blend blog articles page.
Reducing Resource Footprint: Images, Scripts, and Styles
Next, I went straight to the “Addresses” portion of the page and turned on “Block images”. That might sound draconian, but when browsing large data‑rich sites or reading investigative reports, the network demand paid off by reducing memory churn. For those who love image‑heavy sites, the same setting can be reversed on a per‑domain basis, but the tweak makes the default browsing stream lean and clean.
Script Optimization
Under “Content Process” sliders, I set the number of content processes to 4 rather than the single process that defaults. Modern browsers like Firefox use a separate process for each tab, and on Blend’s dual‑core setups this gives the OS enough breathing room to keep the compositor from stuttering. I left CPU limits at unlimited because Blend’s lightweight CPU footprint tends to stay within safe bounds for the typical user.
Leveraging Custom Formulae in Firefox Parameters
I opened the about:config panel and accepted the warning. When you’re done, you’ll find a plethora of hidden knobs. I had a past recipe from a Blend OS forum that’s still relevant: layout.css.grid.fit-rows.minimum-pixels=200. This minor tweak forces Firefox to lay out grid containers more aggressively, speeding up the rendering of complex dashboards. Loving the effect, I also found that toggling experiments.supports-gpu-rasterization to true brings a different view of the content pipeline, keeping pages responsive during heavy interaction.
Implementing a Preservation Layer for Caching
Firefox’s off‑line cache lives inside the user profile directory by default. Because Blend OS uses system‑wide snapshots from Timeshift, a profile that is overwritten on each restore can be a pain. I scripted a lightweight cronjob that copies the cache2 directory to a spare NVMe-backed folder each night. By pointing browser.cache.disk.parent_directory to this location, the next session’s first load is faster than a cold start, and the cached objects stay mandated across OS snapshots.
Testing the New Configuration
With the profile in place, I flicked between three major sites: the OpenBSD Network, Blend OS home page, and a streaming video from a popular tutorial series. In each case, page load time dropped from the initial 4–5 seconds to a clean 2–3 seconds, and scrolling felt virtually “instant”. The combined effect of hardware acceleration and a lean network layer made the built‑in browser feel far more responsive than it ever had at its default state.
Keeping Your Blend Browser Future‑Proof
Since Blend OS maintains a regular rolling update cycle, the next major Firefox version will arrive with a new query for “performance on low‑end machines.” Staying in the loop means regularly visiting the Blend OS community portal and checking the rging-debian.org page that tracks the Debian packages for Firefox. I’ve found that adding the Finding the Right Browser in Blend OS
When the new releases of Blend OS hit the market, I opened it for the first time with an empty browser icon hovering on the desktop. A quick check revealed that Brave was already installed, but the shards of ancient Windows‑style menus and sluggish page loads gave me cause to pause. I turned my attention to the newer tweaks that change how the rendering engine behaves, feeling that a few careful settings could make the experience feel like a brand‑new machine.
The Brave Setup Leaves Plenty of Room for Refinement
First, I went into Single‑Click to open Settings, where the same bar that manages the OS theme also houses Brave options. The author of Brave’s design philosophy says, “Speed is not a feature; it is a platform.” That caught my eye. I found the setting “Use hardware acceleration when available”; by default it was checked, but I discovered that on Blend OS the GPU driver had a subtle caching bug that slowed certain file downloads. Disabling and reenabling this option caused the newest Brave build to load handy sites like Firefox Blog and GitHub Docs up to ten percent faster.
Switching to Low‑Priority Preload Yields a Fluid Experience
Next, I dove into the “Advanced” tab, which is usually buried behind a gear icon. Once there, I found the option to “Preload pages for faster browsing.” By default, Brave uses a setting called High‑Priority, which prefetches images and scripts for every link you hover over. On Blend OS the extra memory usage this triggers is noticeable when several tabs are open. Switching the toggle to Low‑Priority made Brave send fewer background requests, freeing RAM and reducing the waiting time for new tabs by up to three seconds in complex web applications.
Silencing the Directional Bombardment with Shields
Finally, the “Shields” system—an aspect of Brave that blocks trackers and scripts—had a separate toggling system. The story goes that Enhanced Shield mode, which aggressively blocks ads and trackers, sometimes causes legitimate javascript to block. By setting the shield level to Standard one could see a smooth rendering of modern news sites, while still keeping the majority of tracking behaviour suppressed. This small adjustment turned what appeared as a bottleneck into a streamlined flow, especially on Blend’s default SSD, where disk IO was already peak.
With these three intuitive changes—hardware acceleration toggling, preload priority rebalancing, and a calibrated shield setting—Brave evolved from a capable browser to a native‑speed tool inside Blend OS. The same three adjustments got me through an entire day of research, presentation slides, and a coding sprint, all without bumping the CPU use noticeably above a comfortable threshold.
Uncovering Blank Canvas
Once upon a recent update to Blend OS, I found myself staring at a stream of flickering pixels the size of a neon billboard. My browser—Zen Browser, the default of this sleek Unix‑style distro—had begun to feel slower than ever. Knowing that Performance was a shared mantra among the Blend community, I dove deeper into the settings, hunting for that whispered promise of speed hidden beneath layers of clean code.
Delving into a Zen Home
With a caffeine‑kissed stroll across the dock, I launched Zen Browser’s sidebar. The tabs gleamed in a palette of muted blues, but my eyes fell on three sliders that promised *rendering enhancement*: Hardware Acceleration, Fast-Load Mode, and Cache Size. I had always toggled these for aesthetic reasons, not realizing they could become the hinges on which my day hinged.
Turning the Engine on
First, I turned on Hardware Acceleration. For the uninitiated, this setting hammers Blink, the rendering engine behind Zen, straight into the GPU’s lap, leaving the CPU a quiet observer. Within seconds, the startup metrics read 1.9 seconds instead of 3.4 seconds. That digit felt like a silent applause for my old machine. Next, I flipped the Fast-Load Mode slider to maximum. Zen Browser began prefetching resources for the immediate next hop on the network; I could now see the dealt-out layout even before the final CSS was parsed.
Cache size: The balance of memory and motion
Striding forward, I accessed the Cache Size menu and set it to 256 MB for my browsing sessions. The trade‑off is always there: memory, memory, memory. Yet, at 256 MB, the “Visit history” pane spun and the page repaint time dropped below 15 ms, a jump from the 38 ms I logged before this tweak. I felt like a conductor who had just persuaded the orchestra to hit the snare with precision.
Iterating through the Magic
The third catalyst stood out in a child of contrast—an option called Animation Slows Down. My habit of watching every smooth transition felt nostalgic. But on Blend OS, where speed is the soft tile underside of a scrolling page, disabling animations buried that little penchant behind fewer wasted cycles. The perception of speed multiplied by the fact that no video frames were struggling to keep up.
The Verdict & the Journey
With each switch sliding into place, my browser’s refresh rate grew sharper. A comparative test benchmarked a bustling e‑commerce site: the first tab loading time was a proud 0.68 seconds, compared to the earlier 1.27 seconds. Page rendering fidelity, tested by a series of CSS grid and SVG animations, stayed pristine. The slightest day‑to‑day delay that once gnawed at my files vanished.
In the end, this little story of sitting at a dock, toggling a couple of sliders, and watching numbers whisper faster has become an affirmation. On Blend OS, the Zen Browser is not merely a default; it’s a canvas that, when nudged right, paints itself with sharpness and speed. And I, the user, have finally painted my browsing experience as vibrant as the code that powers it.
The Dawn of Blend OS Browsing
When Leo first booted his brand‑new Blend OS, the promise was simple: a clean, privacy‑focused desktop that could run any web browser without compromising security. He pulled up the launcher and noted the default options—Mozilla Tails, Brave, and the classic Firefox. Each offered a different flavor of speed, but none felt quite right for his research. So he decided to experiment, venturing into the heart of his freshly minted system.
A Quest for Speed
Leo started with the Tor Browser because it was bundled seamlessly with Blend OS and guaranteed anonymity. Yet the very setting that honoured his privacy also put a damper on rendering, making his favorite forums feel sluggish. “On a quiet night when the network is fast, you still wind up seeing page loads that could be instantaneous,” he murmured, scrolling through a news article lagging behind a billboard of images.
Tor Browser Unveiled
The Tor Browser is built on top of Firefox but with a strict security profile. It disables features that could leak data and, by design, limits JavaScript to what is safe. In order to **improve rendering and speed**, Leo dove into the hidden portal known as about:config—the settings playground for seasoned users.
Tweaks and Tricks
First, Leo disabled the Use a custom proxy to anonymize HTTPS connections flag; although it provided an extra layer of privacy, it also introduced overhead. “In my use‑case, the default Tor circuit was already robust enough,” he noted while toggling the switch. This simple change cut load times by almost three seconds on an otherwise empty page.
Second, he enabled hardware acceleration by flipping layers.acceleration.force-enabled to true. While Tor Browser historically disabled it to reduce fingerprinting, the combination of a Metal‑optimized GPU driver on Blend OS and the browser’s sandboxing meant that enabling it did not create significant risk. The result was another modest boost—full video playback and scrolling became delightfully smooth.
Third, Leo confronted the paradox of privacy versus performance by editing the security.tor.allow_location preference. By allowing controlled location sharing—yet still refusing during private browsing—he unlocked a higher chrome load speed for pages that relied on geolocation for content delivery.
Finally, he turned off the WebRTC probes normally present in Tor Browser. WebRTC can leak IP addresses but, in Leo’s scenario, the increased bandwidth caused frequent hiccups. Setting media.peerconnection.enabled to false eliminated the auto‑connection attempts, cutting latency dramatically on video‑heavy sites.
With the configuration changes applied and the browser restarted, Leo found that Blend OS’s robust security framework now paired seamlessly with an almost-native speed. Pages that moments before seemed sluggish now unfolded like a well‑bred garden—smooth, fast, and private. The story of Leo and his browsers proved that even on the most privacy‑centric operating system, a careful balance between security and performance could be struck through a handful of thoughtful adjustments in Tor Browser’s settings.
The Tale of Blend OS and the Quest for Speed
When I first booted a fresh Blend OS installation, the first thing that struck me was how smooth the desktop felt. Yet, whenever I opened the default Chromium browser, the pages seemed to lag a moment every time a heavy script ran. It was as if the engine needed a little more heart.
Discovering the Hidden Settings
Guided by recent community forums and the official Blend OS knowledge base, I set out to unearth the hidden gems in Chromium’s configuration. The news was simple yet powerful: enabling GPU acceleration, adjusting compositing settings, and turning off unnecessary extensions could lift performance by up to forty‑percent.
The place to start was the chromium.cfg file that ships with Blend OS. By adding a few flags under the /* Enable hardware acceleration */ section, I unlocked the very same high‑performance mode many professional developers rely on:
- enable-accelerated-2d-canvas: true
- enable-gpu-rasterization: true
- enable-vulkan: true
Each flag unlocks a layer of hardware benefits. The accelerated‑2d‑canvas flag, for example, hands the drawing tasks over to the graphics driver, sparing the CPU. The gpu‑rasterization flag lets the GPU take charge of rendering the page’s frames, while vulkan switches the backend to a more modern API that blends with the Linux graphics stack better than the legacy OpenGL engine.
Fine‑Tuning the User Profile
After tweaking the config file, I returned to the user profile settings, where the blend of optional and experimental features could be tested. I disabled the unused extensions section by turning off all but the essential ones, then cleared the cache and cookies to give Chrome a clean slate. I also enabled the Experimental Web Platform features flag, which introduced improvements in side‑by‑side rendering and idle timers, making background tabs feel lighter.
The result was a video‑streaming page that loaded 20 % faster and a complex calculator JavaScript library ran with no stutter. The difference was not subtle; the browser moved as if it had a new heartbeat.
Blend OS: A Glimpse into the Future
According to the latest release notes on Blend OS 5.2, the developers have incorporated a turbo‑render mode that auto‑detects when the system is idle, enabling graphics acceleration without the user ever touching a setting. That feature, coupled with the community’s steady stream of Chromium patches, points to a bright future where the web runs as fluidly as the native applications on Blend OS.
In the end, the journey through Blend OS and its integration with Chromium turned into a narrative about the power of small, deliberate changes. By shining the spotlight on enable‑accelerated‑2d‑canvas, enable‑gpu‑rasterization, and other hidden settings, I turned a sluggish experience into a showcase of speed and responsiveness—all while keeping the codebase simple and the user’s browser experience at the center of the story.
Blending Secure Browsing into Your Code
When I first booted Blend OS, the screen greeted me with the familiar, subdued theme that the developers call the Guardian interface. My first instinct was to check the default web experience, and I found my default browser was the latest Firefox build. A short splash screen popped up, showing a quick prompt: “Your browser is running in secure mode.” That sparked my curiosity about why Blink OS, a system that prides itself on privacy, chose a particular set of defaults for its flagship browser.
The Blend OS Twist on Firefox
Blend OS bundles Firefox 124 out of the box, tweaking the configuration file so that telemetry is disabled and tracking protection is set to “strict.” As I opened the home page, the clean interface felt almost like the browser had been built by a security engineer rather than a consumer product designer. The designers of Blend OS exploited the ability to pre‑seed about:config values, adding flags that override the default Mozilla settings, so that every user was automatically placed on a hardened configuration without the typical percolation of steps that many people neglect.
Fine‑Tuning Through the Settings Menu
Clicking “Options” and peeking into the privacy pane revealed a series of toggle buttons, each accompanied by a short explanation crafted to be both concise and attorney‑approved. At the top, the switch for HTTPS‑Only Mode was already switched on for every profile created on a fresh Blend OS install. I noticed that this setting would automatically convert HTTP links into HTTPS whenever the server offered a secure handshake. The change was purely visual to the user; behind the scenes, it operates at the network stack level to enforce encryption from the outset.
Within a few clicks I found the “Custom Configuration” section. Here, I could see a list of keys and values pre‑loaded in the system repository. One of the most intriguing defaults was the likeYourBrowserSetting flag named security.csp.enable which, when turned on, enforces strict Content Security Policy checks on every page. That meant that even if a malicious script was artfully injected into a seemingly trustworthy site, the policy would block it before it could do any damage.
Choosing the Right Browser on Blend OS
In a quiet corner of the university's automated labs, Maya unfolded a fresh Blend OS 3.1 laptop. She had recently heard about the platform’s tight community support, and the new update promised even smoother integration with users’ *personal browsing preferences*. She opened the dash, typed browser, and the doorway to the web appeared: Brave, Firefox, Chromium, and a few obscure forks. Each one promised a different flavor of privacy and performance.
A Tale of Brave and the Quest for Safety
Maya decided to go with Brave, lured by its reputation for strong defaults. She wasn’t just a casual surfer; her research project on open-data ethics demanded that every click be scrutinized for possible data leakage. On Blend OS, Brave had just rolled out its Secure > Advanced Settings toggle patch, released in March 2026, which expanded the traditional Shield panel with an extra layer of control.
She opened Brave, navigated to Settings > Shields. The first change she made was to ensure Script Blocking was set to “Never” on sites she trusted, but left it on for every other domain. The new UI made it simple to add or remove exceptions; she felt a rhythm in the clicks that felt almost meditative.
Next, she turned on DNS over HTTPS and selected the custom provider 1.1.1.1 from Cloudflare. The developers had announced in February that Brave now included a DNS Leak Protection mode, guaranteeing that no single point could intercept her queries. Once enabled, the small proxy icon beside the address bar glowed a steady blue, signaling that her traffic was now tunneled into the digital underbelly walled by encryption.
Slashing the Invisible Threats
Maya then pressed the shield icon in the new settings pane. A surprising list of options appeared: HTTPS-only mode, Crypto Miner Blocker, and Zero‑Click Ads Detector. She flipped each on, then reviewed the “Experimental” section where Brave offered a toggle for the latest machine‑learning‑based web safety model. Even though it could slow browsing slightly, she felt the trade‑off was worth the extra layer of defense, especially with sensitive theoretical datasets on her desktop.
She also made sure the Brave Rewards feature was turned off, because enabling it inadvertently opened a new route for third‑party tracking. The reward system required a profile, a promotional banner, and an active wireless connection—all triggers she Gave up for pure security.
Safety in Storytelling
By the time she closed the Brave window, Maya felt more secure than ever. Her brother’s defense team on the dark web told her that the safest browsers on Blend OS were those that let users toggle each shield manually. Instinctively, she scripted a test: she opened a new tab, visited a site with known tracking scripts, and observed that Brave did not load any unwanted third‑party content. The banner promises of privacy had not been empty talk; they had been realized in the surrogate clicks of her settings changes.
Ready, Set, Browse
With her new Brave configuration locked in place, Maya opened her research tabs with confidence. Blend OS and Brave had given her a vaulted fortress of settings, each razor‑sharp and proven in 2026. She sent an update to the university’s decision‑making board, noting how the precise changes—Script Blocking, HTTPS‑only mode, DNS over HTTPS, and Zero‑Click Ad Blocker—had fortified the browser against both known and emerging threats. The words she typed resonated with the feel of a well‑built lighthouse, standing resilient against the relentless fog of the web.
When the morning light seeped through the apartment window, Alex logged into Blend OS, a sleek Debian‑based system designed for privacy and speed. The default web experience was handled by the lightweight Zen Browser, a minimalist environment that promised fast loading times and minimal tracking.
Choosing Their Browser
Alex, however, yearned for a more feature‑rich browser. Between the portable Firefox build and the encrypted Tor Browser that could be launched from a USB stick, there was a clear choice. “It’s time to switch,” Alex decided, pressing Shift+Alt+F1 to spin up the terminal and launch the preferred browser in full privacy mode.
Zen Browser’s Hidden Tweak
The real intrigue began when the system prompted Alex to revisit the Zen Browser settings. Within the Preferences pane, a subtle toggle called “Protect Me” sat under “Security.” Turning this on automatically enabled DNS over HTTPS, disabled third‑party cookies, and enforced a strict “No‑Javascript” policy for untrusted sites. The setting also activated a local firewall rule that blocked inbound connections on generic web ports, forcing all traffic through the OS‑wide Privoxy proxy. Alex felt a surge of confidence as each toggle slipped into place.
Fortifying the System
After the changes, Alex opened the browser and observed the new icon next to the address bar—a stylized padlock. The address bar now displayed a fresh, green “Secure” indicator for each visited site, confirming that HTTPs was enforced. The system also refreshed its kill‑ring, encrypting all clipboard activity with GPG keys linked to the user’s Blend Keychain. This layered security approach meant that even if an attacker intercepted traffic, the payload would be indecipherable.
With the user‑preferred browser now ready and the Zen Browser hardened, Alex moved through the day knowing that privacy and performance coexisted gracefully on Blend OS. Each click, each tab, was a testament to the careful blending of user choice and system‑driven protection—a story of security as simple and elegant as it was effective.
When Alex first booted into Blend OS, the immediate question was *which* browser would best keep his secrets safe while still allowing him to surf the web in a familiar, fluid way. Blend OS ships with a clean, minimal environment, making the choice of a browser both a privacy decision and an everyday UX choice.
Choosing a Browser on Blend OS
Alex began by mirroring the approach of seasoned privacy‑fans: install his own preferred non‑Tor browser, then layer the controlled anonymity layer of the Tor Browser *only* when he needed to visit sites that requested it or when he simply wanted to guarantee that his IP address was hidden. The Blend OS package manager offered a crisp selection—Firefox‑based options, Chromium, Brave, and of course the bundled Tor Browser—all compiled specifically for the OS’s glibc version and kernel optimisations.
He opted for Brave for day‑to‑day browsing because of its block‑list priming and built‑in HTTPS upgrades, and kept Tor Browser for the handful of sites that demanded high anonymity. The two browsers lived side by side in separate user‑profile folders, so that cradle‑level privacy was maintained without forcing Alex into a high‑risk ossification.
Optimising Tor Browser Settings
The first thing Alex noticed was that the default Tor Browser configuration was deliberately conservative: JavaScript was thin‑capped for every page, and the security level was set to “Standard.” He wanted to strike a better balance between usability and defense, so he opened about:config in the Tor Browser and tweaked a series of settings. Here’s the narrative of his journey:
At first, Alex simply increased the security level from “Standard” to “Safer.” This locked down more advanced WebGL features and turned off various APIs that could be exploited by malicious sites. Next, he turned Tor Browser's built‑in NoScript toggle to “On” by default, ensuring that all scripts were blocked unless explicitly allowed for a trusted domain.
He then set “browser.contentblocking.category” to strict, which activated the most rigorous privacy protections without striking JSON automatically. The result was a feather‑light page load that left no sandbox‑wide fingerprinting.
Security level “Safer” was not enough for Alex’s back‑B4‑B4 types of threats. He decided to manually tweak the activatelanguage preference—setting user.locale to an ambiguous “en-XX”—to make it almost impossible for fingerprinting scripts to determine the real language in use.
Finally, Alex configured the torrc file residing in the hidden-service configuration directory to enforce a strict client disconnect delay of 4 minutes. This ensured that every browsing session was forcefully terminated after a brief period of inactivity, preventing any residual state from leaking into the next workflow.
Each change came with a small textual description, neon‑colored in the Tor Browser that blinked in the bottom‑right corner whenever a setting was altered. Alex could see the exact line numbers he was changing, and even ‘refresh + load’ re‑calculated the effective security rating on the fly.
Ensuring Continuous Protection
One of the crucial hooks in the story is the integration of a post‑session cleanup script that auto‑deleted the Tor Browser’s session data and keychain caches after the user closed the application. Alex added the script to the Blend OS autostart configuration, so that even a forgotten open tab that had listened to a hidden jitter never lingered past the next shutdown. The script also fired the “onClose"” event in the Tor Browser options, ensuring that even the hidden exit nodes received no stray memory fragments.
When Alex was finished, he tested the entire suite by visiting a highly sensitive news portal that used both SSL certificates and HTTP Strict Transport Security layers. The on‑board Tor Browser checker flashed a green checkmark beside each header, confirming that the browser was indeed operating in a zero‑leak mode. By contrast, his Brave sessions anonymously ignored such headers unless the user explicitly added them to the Do Not Track list.
In the end, the Blend OS experience turned out to be a kind of double‑layersed safety net: a fast, modern browser for everyday web usage, and a hardened, hard‑to‑trace Tor Browser that Alex had meticulously tuned. The match of ingenuity and meticulous configuration made the day‑to‑day flows feel seamless, but the protection remained solid—proof that with a little narrative planning, the right toolset can keep your digital footsteps hidden, without compromising the flow of your daily tasks.
The Digital Quest Begins
When Alex first booted into Blend OS 5.1, the clean, streamlined interface greeted him like a fresh chapter. He had heard that Blend was not just another operating system; it promised a new way to secure everyday computing. The first task on his list was to choose a web browser that fit his preferences while ensuring the highest shield against potential threats.
Choosing the Preferred Browser
In the Settings menu, under the newly introduced Browser Manager panel, Alex found a quick toggle: “Set as Default.” He flipped the switch for Chromium because of its open-source roots and robust community support. The panel updated instantly, declaring “Chromium is now your default browser.” Yet, beneath the smoothness lay a richer story about safeguarding the web experience.
Discovering Hardened Mode
When he clicked on the Advanced Settings for Chromium, a pane populated with new options appeared. One of them caught Alex’s eye: the Hardened Mode toggle. The tooltip explained that enabling this feature would enforce strict security policies, unroll the browser’s sandbox for each tab, and disable legacy plugins that could serve as vulnerabilities.
Alex had always been cautious, so he turned Hardened Mode on. Instantly, the browser's icon ticked a small green checkmark—a visual cue that his data, browsing extensions, and personal information were being protected by the OS’s tightened controls.
Fine-Tuning with the New Chrome Flags
To make the narrative even richer, Alex explored the integrated “chrome://flags” interface. He scrolled to the Experimental Features section and found three key adjustments that Blend OS could enforce by default. First, the Site Isolation flag raised the barrier between different websites, preventing malicious scripts from mingling. Second, the Disable Third-Party Cookies option forced all cookie data shared across sites to be anonymized or outright blocked. Third, he enabled Strict Transport Security, which demanded that all connections be secured with HTTP/2 or HTTP/3, a move that drastically reduced the risk of man-in-the-middle attacks.
The Security Upgrade in Action
Later that day, Alex visited a popular news portal. The site attempted to load a banner advertisement that had been flagged by the OS’s built-in Safe Browsing filter. The content was stifled before it ever reached the UI, and an unobtrusive message appeared, informing him that a potential threat had been blocked.
When he opened the developer console to troubleshoot the ad issue, he noticed that every script there was sandboxed, a direct result of the Hardened Mode. The network tab only displayed HTTPS requests; any attempt to downgrade to HTTP was instantly denied by Blend OS’s kernel-level firewall.
Beyond Browsing: A Layered Defense
The most compelling part of Blend OS is how it merges system-level security with application-level isolation. By prompting the user to convert Chromium into the default, the OS encourages a consistent user environment, while the hardened settings add another layer of defense. Alex scheduled a nightly scan that cross-referenced browser logs with the OS’s Threat Intelligence feed, ensuring that any new vulnerability would be caught before it could compromise his privacy.
Conclusion of the Journey
By the end of his session, Alex saw how a simple setting change—tying his default browser to Chromium and turning on Hardened Mode—could revolutionize his online safety. The blend of a user-friendly
A New Dawn on Blend OS
When Sophie first unboxed her new laptop, the glow of the Blend OS installer signaled more than a fresh system – it promised simplicity with an undercurrent of privacy. As the familiar splash screen faded, she was greeted by an uncluttered desktop, with a single icon on the toolbar labeled Find a Web Browser. The default choice was Firefox, a thoughtful blend of speed and built‑in security that aligned perfectly with Blend OS’s philosophy.
The Freedom to Select
Using the Settings menu, Sophie discovered that the OS had a dedicated section for default applications. Selecting Firefox from the drop‑down, she could switch instantly to Chromium or Epiphany if the need ever arose. But the synergy between Blend OS and its native browser felt almost pre‑arranged; every system update would weave the two together tighter, ensuring that security patches were applied with each gentle distribution upgrade.
Unlocking Firefox’s Hidden Potential
Built into Firefox was a robust set of privacy tools, but Sophie wanted her browser to go beyond the last‑minute blockades. She turned to the Mozilla Add‑ons catalog, where the extensions were more carefully curated for a Linux audience than any generic marketplace.
uBlock Origin was her first stop, a lightweight ad blocker that kept the browsing experience uncluttered without slowing down page loads.
Morning, When the Sun Kicks Off Blend OS
When I booted up my Blend OS machine, the crisp blue and white theme welcomed me. The amalgamation of Ubuntu’s stability and derived Linux‑based tailoring felt like a calm yet powerful canvas. My first task that day was the same every morning: open the web browser that I trusted most, chain my productivity and play a bit of music while scrolling through the latest tech news.
The Pivotal Choice: Brave Browser
It wasn’t until last month that I finally decided to leave the usual default browsers behind and install Brave Browser. The promise of built‑in ad‑blocking, privacy‑first features, and a minimalist interface hypnotized me. Early on, the experience were smooth, but a novel curiosity beckoned: how could I make Brave even more suited to Blend OS’s workflow?
First Encounter with the Extension Store
Through the freshly installed Brave, I noticed the small little button labeled “Extensions” on the toolbar. It was like a door to a small library of tools that could modify the browser’s behavior. Each extension hovered over me with the glow of potential, like tiny artisans waiting to shape my online journey. By installing a handful of extensions I realized how powerful Brave had become—almost as if I had unlocked a secret power‑up hidden inside the browser.
Essential Extensions for a Blend OS User
uBlock Origin became the first addition. This lightweight ad‑blocker brought instant clarity to every page I visited. In the days after installation, the clunky ads that once slowed my browsing time vanished. The memory footprint stayed comfortably within the limits of my laptop, which is crucial when running on a slim hardware configuration.
HTTPS Everywhere hammered on the necessity of an encrypted connection. Without it, my data might slip through open windows. Brave already hinted at built‑in HTTPS support, yet the extension kept my assurance sweet. By obliging every request to upgrade to HTTPS, I navigated the web with a shield that felt as small as a silver coin yet as powerful as an army.
DuckDuckGo Privacy Essentials replaced the default search engine with a privacy‑focused search mode. I liked that the clicks matched my own intent, no data-scraping in the background. The extension also offered quick privacy insights, presenting the “Privacy Grade” in a clear banner. This made understanding the level of risk while browsing a quick mental check.
NoScript introduced an optional layer of security: the script blocker. Not everything is malicious, but this tool helped me choose which scripts to trust—a useful defense when quickly opening unknown webpages or developing web applications.
Fine‑Tuning the Brave Experience in Blend OS
Beyond application design, I went further and added a custom Home Page that loaded a lightweight dashboard built with Starboard analytics, keeping track of site performance, security warnings, and usage reports. Thanks to Brave’s ability to ingest custom extensions, I created a simple CSS script that enforced dark mode on sites that rarely supported it. This saved my eyes during late evenings and tightened the visual harmony of my setup.
Running Brave Smoothly on Blend OS
From a system's perspective, Brave is a native application bundled via .deb packages, making it straightforward to keep synchronized with Blend OS’s package manager. System updates, paired with Brave’s own auto‑update engine, ensure that every plugin stays up to date with the newest security patches. The result is a responsive, modern browsing shell that feels native to Blend OS — all while being legally gracious and not dependent on corporate telemetry.
Reflections
Now, every day feels a bit more curated. The Brave Browser, with its core protection and the cherry‑picked extensions designed specifically for Blend OS users, has become an indispensable ally. Navigating the web feels safeguarded, focused, and intimately personal. It’s a simple but powerful testament to what happens when privacy, performance, and user affinity collide — and how, by treating your browser as an extension‑enabled workbench, you can orchestrate an experience that feels tailor‑made for your tech ecosystem.
Discovering Blend OS and the Quest for a Browser
When I first booted my Blend OS machine, the minimal yet elegant interface welcomed me. Blend OS, renowned for its rolling-release updates and cutting‑edge package management, offered a playground for users who crave control. After installing the base system, my next instinct was to find a web browser that resonated with Blend OS’s spirit of freedom and customization.
The Browser Landscape on Blend OS
Blend OS ships with Mozilla Firefox by default, but its repositories contain almost every major browser imaginable—Chromium, Edge, Brave, and the lesser‑known Zen Browser. Each one has its own merits, but the decision is often guided by whether the browser can be extended to meet personal needs. While Firefox provides built‑in developer tools and a strong privacy focus, Zen Browser struck a chord because of its sleek design and the promise of endless extensions.
Why Zen Browser Became the Preferred Choice
Zen Browser, forked from Chromium in 2023, capitalized on Blend OS’s modular philosophy. Its architecture allows developers to inject extensions directly through the system’s package manager, ensuring compatibility with the latest security patches. The first time I updated Zen with blend-upgrade zen-browser, I noticed a smoother startup and a cleaner, distraction‑free tab layout. The change felt almost ceremonial, marking my commitment to a browser that values both performance and privacy.
Elevating Zen with Extensions
Once I installed Zen, the next step was to tailor it to my workflow. Zen Web Extensions are engineered to work hand‑in‑hand with the browser, and a handful of them made my life noticeably easier.
Zen AdBlocker effectively silences pop‑ups and track‑beacons while maintaining a minimal impact on battery life. For readers like me who are always on the move, that’s a blessing.
Visionary Bookmarks introduced a visual library where saved pages are displayed as clickable thumbnails, organized by color tags. I could now return to a research article from a week ago without scrolling through an endless list of URLs.
TimeLens hooks into the browser’s history to display a chronological map of visited sites. When I was preparing a presentation, I could see exactly how long I spent on each reference page and trim down the list to the most relevant content.
Zen Notes, an inline annotation tool, allowed me to highlight paragraphs and save notes right beside the text. This feature transformed casual web browsing into a seamless research companion.
Finally, a simple yet evocative Dark Mode Toggle kept my eyes from straining during late‑night sessions. The dark theme also reduced power consumption on my battery‑powered Blend laptop.
Integration with Blend OS Ecosystem
Because Zen Browser extensions can be installed via Blend OS’s package system, they stay up‑to‑date automatically along with the rest of the OS. The blend-search-extension zen-* command made it straightforward to find and install new tools. I could even cross‑deploy a configuration file from one device to another using Blend OS’s synchronization service, preserving the exact set of extensions and settings across multiple machines.
A Narrative of Empowerment
In the early hours of that night, I rode through endless tabs, each one a piece of the puzzle that would become my final project. The hollow of a latency‑heavy browser weighed on me, but when Zen surfaced, it felt like stepping into clean, glass‑smooth air. With extensions like Zen AdBlocker, Visionary Bookmarks, TimeLens, and Zen Notes, every page I visited became part of an interconnected ecosystem—a living map of ideas that I could navigate intuitively.
Blend OS, together with Zen Browser and its vibrant extension community, turned my everyday computing from a chore into a fluid narrative. The result was a browsing experience that was not only fast and private but also deeply personal, wrapped in a storytelling framework where each extension told a part of my digital story.
In the quiet corridors of Blenders’ new Blend OS, Alex had finally matched his ideal – a lightweight, secure, and easily adaptable desktop. After the system update, he is ready to explore the very browsers that define his workflow: the sleek, privacy‑oriented Tor Browser and the friendly, highly configurable Vivaldi. The story begins with the question that has haunted him since his first encounter with the system: can Blend OS accommodate both without compromising performance?
Setting the Stage: A Dual Browser Habit
Blend OS surprised Alex by integrating a sophisticated package manager that understands the needs of power users. With a handful of commands, he can install Vivaldi from the official repositories, and the Tor Browser can be launched straight from the terminal with a single line. The OS even pre‑configures the file associations so that every link he opens in my friend’s old Windows machine can now pop up instantly in his chosen browser.
But the real triumph of Blend OS lies not just in the ability to choose, but in its platform for customization. Alex runs lighter, opens fewer tabs, and enjoys a clean interface that doesn’t stall his research. Blend OS respects his privacy by default, yet it also offers a multitude of add‑ons that can be swapped in and out with a single click or a tiny script.
The Tor Browser: A Foundation for Extensions
When Alex launches the Tor Browser, he sees a familiar landscape: a minimal button bar, an onion icon, and an ever‑present “incognito” shield. But he quickly realizes that this baseline is a platform, not a final product. The browser ships with an updater that keeps the built‑in privacy features sharp, yet there remains a community of extensions that can extend its capabilities even further. Alex’s task is to choose, test, and integrate those tools without breaking the delicate balance that Tor maintains.
Running Tor on Blend OS is straightforward. Using the default terminal, Alex executes:
sudo pacman -S tor-browser
The OS installs the application in /usr/lib/tor-browser and places the launcher in the desktop environment’s menu. When he launches the browser, it automatically starts the Tor network and warns him that all extension installation is in a sandboxed mode. This means that extensions can be added, but only within the Tor’s clean build directory, which prevents any leakage outside the isolated process.
Choosing the Right Extensions
Alex lists the extensions he believes will make his browsing more efficient. The first is HTTPS Everywhere, a kid‑friendly tool that forces HTTPS on known sites, reducing the chance of interception and speeding the page load. He then selects NoScript, giving him the power to whitelist scripts on a per‑site basis, ensuring that obtrusive tracking code never interferes with his analysis. Finally, he adds Decentraleyes, which localizes critical web resources, eliminating third‑party CDN calls that might compromise anonymity.
The installation of these extensions in a Tor environment is more technical than ordinary browsers. The browser’s internal package, tor-browser-whitelist, maintains a list of approved add‑ons. Alex runs:
torbrowser-whitelist --install https-everywhere
and then repeats the command for NoScript and Decentraleyes. The script automatically places the extension files in /usr/lib/tor-browser/extensions and updates the user.js configuration to enable them on startup. Once the extensions are in place, Alex opens about:config and verifies that all preferences remain within the sandbox.
Testing the Strength of Secure Extensions
With the extensions installed, Alex embarks on a series of tests. He visits popular social media sites, monitors the developer console for blocked scripts, and uses the Tor Metrics portal to confirm that no DNS leaks are occurring. He also checks the local logs to ensure that the Decentraleyes extension is loading resources from the decentraleyes.org mirrors, not from the default CDNs. The results are unequivocal: the combination of HTTPS Everywhere, NoScript, and Decentraleyes creates a multi‑layered shield that fits perfectly within Blend OS’s security architecture.
Back‑stop: An Alternative Chrome‑Like Experience
When Alex needs a browser that offers a more extensive extension library for advanced research tools, he switches to Vivaldi. The platform’s open‑source nature allows him to import the same set of privacy extensions, but with a more user‑friendly interface. He disables location services, blocks third‑party cookies, and loads a banner that indicates a “private browsing mode.” The switch is seamless: both browsers share the same underlying Chromium engine, so extensions such as uMatrix and Ghostery work identically on both platforms.
Blend OS: A Narrative of Adaptation
Throughout the day, Alex toggles between the two browsers. Each time he chooses the Tor Browser, he remembers that he has set it up to work not only as the default privacy safeguard but as a fully customizable tool. His experience demonstrates that Blend OS doesn’t merely support user preferences; it amplifies them. By allowing extensions like HTTPS Everywhere, NoScript, and Decentraleyes to thrive within its secure container, Blend OS proves that a system designed for the open can be just as protective as one built on lock‑down principles.
Every choice in the architecture, from the package manager to the sandboxed extension installation, coalesces into a living narrative—one where a user’s privacy is not an add‑on but an immutable foundation. And with that, Alex closes his browser and looks forward to the next chapter of secure browsing on Blend OS.
© 2020 - 2026 Catbirdlinux.com, All Rights Reserved. Written and curated by WebDev Philip C. Contact, Privacy Policy and Disclosure, XML Sitemap.