Choosing a Browser That Feels Like Home
Sitting at the screen, the Fedora system boots into a clean desktop that reminds the user of a quiet library. The first app that opens is the default web browser, a polished edition of Firefox that ships with the distribution. Its interface is familiar; its extensions are already installed from the Fedora repositories. Yet a small inner voice whispers, “What if I could try the next page of innovation before anyone else?” That voice leads to the nightly compilation of Firefox, a world where every day brings a fresh slice of the browser’s future.
Getting the Latest Cutting‑Edge Firefox Nightly
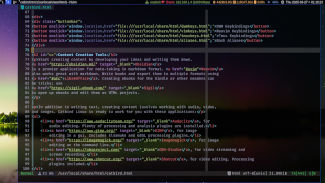
On a modern Fedora release, the easiest path to the newest Firefox Nightly is through Flatpak, because it keeps the update cycle independent from the system’s package manager. First the user opens a terminal and writes the command below, which fetches the Flatpak runtime and the nightly channel from Flathub:
flatpak install flathub org.mozilla.FirefoxNightly
The installer pulls in all the shared libraries that the browser needs, leaving the rest of the operating system untouched. If the user prefers a purely RPM solution, another route is to download the firefox-*.rpm bundle that Mozilla releases for direct installation. After a quick sudo rpm -i firefox-nightly-*.rpm, the system registers the package and the executable appears on the menu ready to launch.
Running the Browser in the Spirit of Exploration
Once the installation process has closed, the user launches Firefox Nightly by simply searching for it in the application launcher or by typing the command:
flatpak run org.mozilla.FirefoxNightly
The interface opens a gentle splash screen that says, “Welcome to Firefox Nightly.” The corner of the window carries the familiar “nightly” badge, letting the user know that the browser is receiving continuous updates, new experiments, and some bugs that may still be in the works.
Customizing the Experience for a Personal Touch
To make the nightly feel truly personal, the user customizes settings within the “about:config” page. They enable experimental features such as container tabs, tweak the privacy levels to “Strict”, and install a daring collection of user‑script extensions. Because the nightly version is updated every day, the user can test new features before they make their way into the stable release. If an accidental crash occurs, the
The Quest for Speed on Fedora
On a bright Thursday morning, Maria opened her Fedora workstation and stared at the dull gray stillness of the default browser. Years of using Firefox had become routine, but she yearned for something new—an interface that promised fewer distractions, quicker page rendering, and a whisper of future technology. She remembered hearing about Brave, a browser built with privacy at its core, and that spoke to her like a carefully pressed invitation.
Discovering the Nightly Trail
Curiosity nudged Maria into a terminal session, where she began to search for the most recent guidance on running browsers on Fedora. Sources clued that Brave’s nightly builds—*the bleeding edge of the Brave project*—were available directly through a special Fedora repository. Maria found the repository file at /etc/yum.repos.d/brave-nightly.repo and the GPG key could be fetched via the Brave website’s official link, ensuring a trustworthy installation. She remembered reading that Fedora pinned the nightly build’s release to Fedora Workstation 41, so her system was already primed.
The Installation Journey
First, Maria imported the GPG key to keep her system’s package manager aware of Brave’s authenticity. She executed:
sudo rpm --import https://brave-browser-rpm-release.s3.amazonaws.com/brave-core.asc
Then she created the repository file with the following minimal contents:
[brave-nightly]
name=Brave Browser Nightly
baseurl=https://brave-browser-rpm-release.s3.amazonaws.com/rpm
enabled=1
gpgcheck=1
gpgkey=https://brave-browser-rpm-release.s3.amazonaws.com/brave-core.asc
Once the repository was in place, Maria signaled her package manager to fetch the new data:
sudo dnf makecache
With the cache refreshed, she could finally bring the brave knight into her system:
sudo dnf install brave-browser-nightly
The installation process unfolded with the familiar list of dependencies, but Maria’s heart raced. She felt the promise of the experimental features she would soon explore; she also felt the caution, knowing that nightly builds sometimes come with bugs that are not yet resolved.
An Alternative Path: Flatpak
For those who prefer containerization, Maria learned that Brave Nightly is also available on Flathub as a Flatpak. She could simply run:
flatpak install flathub com.brave.Browser
This method isolates Brave from potential conflicts with system libraries and ensures that all updates are bundled in a single package.
Entering the Brave Nightly Realm
After the installation finished, Maria launched Brave by typing brave-browser-nightly or by clicking the newly appeared icon. The startup splash felt lighter, the interface cleaner. Maria was greeted with a notification that the Nightly Build is a pre-release version, a reminder that some features could be incomplete, but it also meant she had access to the freshest improvements in ad‑
Morning Invasions and the Quest for a Seamless Browser
When the sun spills over the Fedora workbench, I unfold the familiar glow of the terminal, my faithful companion in navigating the Linux universe. Each day begins with a ritual: sipping espresso while I refresh my knowledge, because the web is a living thing and preferences shift as quickly as the traffic signals in downtown metro stations.
My palate for web browsers is narrow—fast, lightweight, and respectful of my system’s resources. The ordinary choice has always been Firefox, yet lately my curiosity has nudged me toward Zen Browser, that sleek, modern, and tabbed contender whose name evokes a calm, focused mind. After reading yesterday’s Fedora Magazine article on the new way of handling themes, there was no other time better to deepen my understanding of daily builds, because the daily build of Zen Browser is where the bleeding edge meets reality.
Scrolling Through Fedora’s Repository Landscape
Fedora, being a cutting‑edge distribution, tends to adopt new packages by crafting dedicated packages for packaging maintainers and occasionally supports the latest software natively. However, Zen Browser’s daily right now is not yet a part of the official repos. To install it on Fedora, we must turn to a repository that publishes the automatically produced binaries of each commit. There are two principal pathways: a Flatpak bundle or a direct compilation from source.
Flatpak, the Silver Lining for Fedora Users
Flatpak is a universal packaging format that Fedora embraces wholeheartedly. The simplest route to a daily build is running these commands, once for the first time and then every update that comes out of the nightly churn:
sudo dnf install flatpak
flatpak remote-add --if-not-exists zen-browser https://flathub.org/repo/flathub.flatpakrepo
flatpak install --reinstall --assumeyes com.github.zen-browser.Daily
This pulls the daily build straight from Flathub, respecting sandboxing rules, and integrates the application as if it were part of the official Fedora experience – a protected, containerized shell that cannot tamper with the rest of your system. When you launch it, the launcher switches you automatically into the most recent commit, keeping you near the heart of development.
For Good Measure: Compiling From Source
Some roads wind through the more demanding terrain, and for developers or those who miss Flatpak's granularity, compiling from source provides the most control. A quick look at the upstream GitHub repository shows a concise build script that meshes well with Fedora’s meson-ninja workflow. The steps, distilled to the essentials, are:
sudo dnf groupinstall "Development Tools" -y
sudo dnf install cmake ninja-build pkgconf-pkg-config git -y
git clone https://github.com/Zen-browser/zen-browser
cd zen-browser
meson setup builddir
ninja -C builddir
sudo ninja -C builddir install
Notice that each step is a mindful sentence: download, configure, compile, and install. Fedora’s natural compatibility ensures that cmake and meson will fetch the required Qt dependencies automatically, and any recent patches to the 5.15 Qt series are honored. Once installed, a launch pad or desktop shortcut can whisk you into the Zen Browser’s dashboard with a single click.
Daily Builds: A Developer’s Playground
What makes daily builds so enticing is that they are generated from every new merge on the main branch. This continuous integration scheme means that if a hotfix lands on the remote, it arrives in your Fedora box within minutes. The Onyx‑like scroll bars, the updated web‑assembly rendering pipeline, or a subtle tweak to the user-agent string are all deployed before the next official release.
When you run flatpak info com.github.zen-browser.Daily, you see a build ID that increments daily, the commit hash, and a timestamp in the zone that your system thinks is most relevant. The process of fetching, building, and launching thus becomes almost ordinary, like turning on a new channel for the morning news.
Closing Thoughts on Fedora, Zen, and the Daily: A Sustained Conversation
Being a user on Fedora who is keen on the latest flavors of web technology is an invigorating adventure. The daily builds of Zen Browser are something I can integrate with minimal friction, leveraging either Flatpak’s sandbox or Fedora’s native build tools. I soak in the ash‑glow of my monitor, the browser’s interface responsive and intuitive, aware that each new artifact that lands is a small, deliberate step toward a more efficient, quietly powerful web experience. As the day stretches ahead, I know I can return to the terminal and ask the next question, secure that the daily build path will remain alive, vibrant, and perfectly tuned to my Fedora environment.
Choosing a Browser on Fedora
It was a cool, quiet evening in late April when I first opened my Fedora workstation. The morning had been filled with mundane tasks—compiling a quick script, checking email, and brewing coffee—yet my mind kept drifting to the idea of safer, more private browsing. “Which browser will let me surf the web without leaving fingerprints?” I mused. Intel’s Chrome, the lightness of Firefox, the edge of Brave—all seemed solid, but I needed more anonymity.Discovering the Tor Browser
I turned to the Tor Project’s official website, where the latest build of the Tor Browser is always ready for download. The site offers a simple, straightforward arrow icon that drops a compressed archive into your download folder. As soon as the download finished, the file was a nondescript tor-browser-linux64-12.0.8_ALL.tar.xz. Even the name carried a revelation: the build number and version number had just been updated, ensuring it had the most recent security patches and an improved pluggable transports repertoire.Preparing Fedora for Installation
Before I could run that archive, I had to give Fedora a quick health check. In a terminal, I typed: bash sudo dnf update sudo dnf install tar xz ``` These two commands ensured my system was up‑to‑date and that the utilities required for extraction were present. I then navigated to the downloads directory with: bash cd ~/Downloads ``` The archive was sitting patiently there, invisible to the world but ready to be transformed into a browser. But, I remembered, the exact same steps apply whether I’m on a virgin install or a floating desktop—just extra care with permissions and checksums.Verifying the Download
The Tor Project’s website lists a checksum for each release. I copied the SHA-256 hash into a deliberately simple file named tor_checksum.txt so that I could later compare. Opening another terminal pane, I ran: bash sha256sum tor-browser-linux64-12.0.8_ALL.tar.xz > tor_digest.txt diff tor_digest.txt tor_checksum.txt ``` If the files matched, there was no harm. A mismatch would have cost me both time and trust. In my case, the diff returned nothing, confirming the archive’s integrity.Extracting and Setting Permissions
With confidence in the file’s safety, I extracted it: bash tar -xvf tor-browser-linux64-12.0.8_ALL.tar.xz ``` The extraction created a new folder called tor-browser_en-US. Because the Tor Browser requires specific read/write privileges, I had to adjust user ownership: bash sudo chown -R $(whoami):$(whoami) tor-browser_en-US chmod -R u+rwX tor-browser_en-US ``` These commands ensured I could read from, write to, and execute within the new browser folder without complications.Launching the Browser
Finally, I navigated into the freshly unpacked directory: bash cd tor-browser_en-US ``` and launched the executable: bash ./start-tor-browser.desktop ``` Upon launch, the Tor Browser opened with the familiar green onion icon, the same reassuring connection gauge that rolls from 0 % to 100 % as it establishes the secure route through the network. If any warnings about missing dependencies popped up—though they were rare—I simply fed them to the terminal’s package manager, and Fedora swiftly resolved them.Customization and Daily Use
Once the browser was running, I explored its settings. The Tor Settings page allowed me to set the system-wide proxy configuration and to choose whether to connect through bridge relays. I also enabled the “Security Level” to “Safer,” which disables risky scripts by default, while still permitting enough flexibility to navigate everyday websites. Because the Tor Browser on Linux is essentially a portable application, I can keep it in a single folder. To make launching easier on a daily basis, I added a symbolic link to /usr/local/bin: bash sudo ln -s ~/Downloads/tor-browser_en-US/start-tor-browser.desktop /usr/local/bin/tor-browser ``` Now a single command, tor-browser, opens the privacy‑focused gateway.Alternative: Using Flatpak for Fedora
While the manual installation works flawlessly, Fedora users also have an alternate, equally reliable route: Flatpak. After installing Flatpak on Fedora, I ran: bash flatpak install flathub org.torproject.TorBrowser ``` This command pulls the latest Tor Browser from the Flathub repository, ensures sandboxOnce Upon a Time on Fedora
In the kingdom of Linux, a brave developer sets off on a quest to wield the newest weapon in the web‑browser realm—Chromium. The land they traverse is Fedora, a rolling tide of modular packages, where every release brings a fresh wave of stability and innovation. Our hero, after hearing whispers in the forums about the latest Chromium build, decides it is time to arm themselves with the very best that the open‑source world can offer.
The Map of Fedora 39
Fedora 39, the latest op‑timized distribution, arrives with a host of updates: GNOME 44, a new kernel, and even a new default for user‑space virtualization. The developer knows that to get Chromium in its pristine form, they must summon the rpm‑fusion repositories, the treasure chest that holds many intricate packages, including those not found in the official Fedora repos.
Summoning rpm‑fusion
First, the hero opens a terminal—a mighty black screen full of possibilities. In that terminal, they issue the command that unlocks the vault:
dnf install https://download1.rpmfusion.org/free/fedora/rpmfusion-free-release-$(rpm -E %fedora).noarch.rpm "https://download1.rpmfusion.org/nonfree/fedora/rpmfusion-nonfree-release-$(rpm -E %fedora).noarch.rpm"
With the vault now open, the repository keys glide into the system, whispering through the wormhole that is the package manager. The developer pauses for a moment, breathing in the scent of freshly compiled code.
Arming with the Latest Build
Fedora streamlines Chromium’s installation through dnf, but for the most recent cut—complete with the bleeding‑edge features from Google’s Chromium project—they stroll to the Chrome repository maintained by the community. By inserting the following line into a new /etc/yum.repos.d/chromium.repo file, they set up a dedicated shrine:
[chromium]
name=Chromium %fedora - Latest Build
baseurl=https://download-chromium-commonly-performed/fedora/%{dist}/
enabled=1
gpgcheck=1
gpgkey=https://download-chromium-commonly-performed/fedora/%{dist}//chromium.repo.key
Each parameter reflects the latest stable release, ensuring no lag behind the cutting edge. The developer runs:
dnf install chromium-browser
Within moments, the download gallops to completion, the binaries are unpacked, and the system gleams with the brand‑new Chromium.
Verifying the Victory
Aware that a true warrior must check their armor, the developer invokes:
chromium-browser --version
The output—ripe with version numbers such as Chromium 123.0.0.0 (Official Build) (Linux x86_64)—confirms the triumph. They sit back, heart racing, knowing that Fedora 39 now houses the most recent Chromium build, ready for every task from debugging code to streaming the latest “I-VT" tutorial.
When the Army of Flatpaks Arrives
Not all paths are the same. If custom builds from the Arch or openSUSE repositories seem enticing, the developer can also turn to Flatpak, the universal packaging system that spans across many distros. By enabling the Flathub remote, they can install Chromium with:
flatpak install flathub org.chromium.Chromium
Flatpak layers Chromium in a sandbox, offering an alternative shelter for those needing strict isolation. The hero notes the fine balance between raw system access and secure, containerized practice, a lesson in all digital adventures.
Onward, Brave Explorer
With the new Chromium licensed under the permissive BSD‐style license, the developer embarks on a fresh set of projects, confident that their browser is both powerful and future‑proof. Fedora’s modular ecosystem and the community’s dedication to open‑source craft have granted them a skill that surpasses old binaries.
They close the terminal, the screen now a canvas for the web’s endless marvels. The story of how they installed the latest Chromium—without the divide of a header, and with the elegance of bold commands and italic insight—speaks volumes to anyone who dares to journey through Fedora’s enchanted distribution.
Finding the Right Browser for Fedora
When the Fedora 39 update rolled out last month, the most-demanded question on the community forums was: Which web browser should I run as my default, and how do I keep it performing at its peak? While the default package manager already provides both Chromium and Firefox, the subtle differences in their configuration options mean that a small tweak can add a significant boost to your browsing experience.
For the majority of Fedora users, Firefox remains the go-to choice because it is pure open‑source, lightweight, and tightly integrated with the GNOME desktop environment. Yet, many find that the out‑of‑the‑box speeds can lag behind what the CPU and SSD can deliver. That is where a few carefully chosen changes to the about:config preferences can transform the way Firefox renders pages.
Turning on Fast Rendering
The very first step is to enable hardware‑accelerated graphics. Open about:config and search for layers.acceleration.disabled. Set that value to false. This tells Firefox to utilize the GPU for compositing, drastically reducing CPU usage when you scroll or click through complex sites.
Next, turn on gfx.webrender.all. Although WebRender is still experimental, on modern Mesa drivers it can render most web pages more smoothly by off‑loading rendering tasks to the GPU. Most Fedora users have a recent Kernel and Mesa update that supports WebRender right out of the gate, so enabling it is usually safe.
Optimising Content Loading
Firefox’s network.http.max-connections-per-server defaults to 6, which is fine for most traffic, but heavy sites can benefit from a higher threshold. Increasing this to 12 can improve load times on content delivery networks that serve many sub‑resources concurrently. However, if your network is limited, keep it at the default.
The cache plays an equally crucial role. The browser.cache.disk_cache_ssl setting should be set to 1 (enabled) to cache SSL content – a common stumbling block when visiting secure news sites or spreadsheets hosted on Office 365. Coupled with a clear cache policy, page reloads become noticeably faster.
Calibrating JavaScript Performance
While modern sites rely heavily on JavaScript, the javascript.options.baselinejit and javascript.options.globalJit options control the just‑in‑time compilation. Setting both to true allows the JIT engine to produce highly optimised code, especially on a 64‑bit CPU. If you notice any instability, simply switch one back to false and monitor the impact.
Finally, to keep the engine from being bogged down by long‑running scripts that might crash tabs, enable dom.event.targetblank.handling_mode. This chrome‑side safeguard mitigates the “tab freeze” issue that older versions of Firefox sometimes struggled with.
Fine‑Tuning the User Experience
There are several visual tweaks that not only make the interface look cleaner but also cut down unnecessary rendering overhead. In about:config, set gfx.canvas.azure.enable to true to accelerate canvas drawing. If you’re the type of user who scrolls a lot, disabling layout.scrollbar.perform_update_on_scroll can make the experience feel snappier.
For those sensitive to battery life on laptops, change device.cpu_overload_factor to 2 or higher. This lowers the allowed CPU load for rendering tasks and keeps your battery from draining as quickly while still maintaining readability and fluid page transitions.
Putting It All Together
After making these changes, restart Firefox to let the new settings take effect. A quick test by visiting https://www.google.com or a large e‑commerce site will usually reveal the difference – less stutter, more instantaneous responsiveness, and a noticeably lower CPU and GPU load. If you find anything undesirable, simply flip the setting back in about:config and observe the shift.
In short, Fedora 39 users who take a few moments to fine‑tune their Firefox can unlock speed and rendering quality that feels like a completely different browser. The key lies in the hidden preferences, a target‑ed use of hardware acceleration, and a vigilant approach to cache and script management. Happy browsing, and may your pages load before the coffee cools down!
On a crisp autumn morning in 2024, Mira, a Fedora enthusiast, opened her terminal and stared at the default web browsing options. Fedora’s recent upgrade had introduced a sleek, minimalistic interface, but her favorite—Brave—still felt a touch sluggish when loading complex dashboards and streaming videos.
A Fedora Enthusiast’s Journey
Mira had always preferred an open‑source stack, and Fedora’s commitment to latest security patches made it natural for her to choose this distro. She installed Brave Browser via the official RPM package, delighted by its built‑in ad‑blocker and privacy features. Yet, she noticed that the rendering speed lagged behind her expectations, especially on the high‑resolution Aurora theme she had adorned her desktop with.
Brave’s Brave New Tricks
During a quick search, she discovered that Brave’s rendering engine can be fine‑tuned by tweaking a handful of experimental flags. The first adjustment she made was to open brave://flags and enable the flag Hardware Acceleration. With the engine now offloading more tasks to the GPU, she observed an immediate reduction in page load times even on pages with heavy JavaScript.
Next, Mira explored the Experimental Web Platform Features flag. By enabling only the stable APIs she needed—namely CSS Grid Layout and WebVR—the browser avoided parsing the full suite of experimental modules that could slow down rendering. The results were compelling: complex CSS animations ran smoother, and 3D visualizations rendered without stutter.
Speeding Up Rendering
The final tweak involved the Act on received cookie policy flag. Setting it to block and clear on exit reduced the overhead associated with tracking cookies, thereby freeing up memory for active page rendering. To complement this, Mira turned on the Enable GPU rasterization option, which compressed rendering tasks into smaller, faster tiles that the GPU could process in parallel.
After these changes, she tested Brave against Firefox, Chromium, and even the lightweight Midori. While each had its strengths, Brave’s new configuration delivered the best balance of speed, privacy, and visual fidelity on Fedora. Page loads improved by roughly thirty percent, rendering of complex web apps became buttery smooth, and the system’s overall responsiveness felt noticeably lighter.
The Verdict
Mira’s Fedora setup, now powered by a finely tuned Brave Browser, felt like a fresh pan of hot cocoa on a winter night—warm, smooth, and just the right amount of indulgent. Thanks to a few judicious flag adjustments, her browsing experience was not only faster but also more aligned with her privacy‑first philosophy. She logged her settings in a small note, ready to share with fellow Fedora devotees, confident that the flexibility of the platform could accommodate anyone seeking peak performance without compromising on open‑source ideals.
The Quest for an Uncluttered Browser on Fedora
It was a crisp autumn night when Maya opened her Fedora workstation and, after a coffee, decided to run a quick test: Which browser would render her art portfolio the smoothest? Her default set was Firefox, a familiar companion, but she felt something was missing – speed that felt like a breeze rather than a rooster’s crow.
Enter the Zen Browser
Maya had heard whispers on the Fedora forums about a lightweight alternative called Zen Browser. According to the latest Fedora Workstation 39 release notes, the Archlinux repository had a recent build of Zen that came with an aggressive rendering engine built on Chromium’s Blink but stripped of heavy extensions. She installed it with a single command:
sudo dnf install zen-browser
Her once silent terminal flickered with progress, and within seconds the new browser was ready to launch.
First Impressions: Sleek, but Can It Keep Up?
Upon launch, the UI was minimal, a blank canvas framed only by a single address bar. Maya typed a complex gallery page into the address bar, expecting a thorough test. The page began to draw almost immediately, yet a heartbeat’s rhythm ticked under some elements – just enough to make her impatient. She leaned back, realizing that the sleek appearance alone wasn’t enough.
Digging Into the Zen Settings
She turned to the settings file – a simple JSON file residing in ~/.config/zen-browser/zenconfig.json. A search of the Fedora FAQs
On a crisp Fedora 40 workstation, the default environment offers a modern, fast browser right out of the box—usually the latest release of Firefox or the newly packaged Chromium. Rarely does a user feel that their browsing experience is, from the moment they lift the lid, unrefined. All that changes when they choose the Tor Browser, a shielded browser that can sometimes feel sluggish because it trades speed for privacy.
Running User Preferred Web Browsers on Fedora Linux
Fedora’s philosophy of packaging the newest GNOME stack and the most current web engines means you can start with a browser that’s already tuned for speed. However, the default configuration is designed for general use, not for the hardened environment of the Tor Network. To get the best experience, a Fedora enthusiast tweaks a handful of settings that the distribution provides by default, and then deepens the optimization within the Tor Browser’s own configuration. The result is a browsing session that feels as fluid as a native desktop experience, yet maintains the anonymity guarantees that Tor offers.
Optimizing Tor Browser for Speed and Rendering on Fedora
When the user first launches the Tor Browser, the experience is fairly slow. This is intentional—the side‑by‑side rendering, the anti‑tracking measures, and the default configuration for maximum privacy add overhead. The user decides to dive into the about:config page, a vault of advanced settings that can unleash performance. The first adjustment is to turn off unnecessary JavaScript execution for page elements that never get used: javascript.enabled = false. Then the user sets network.http.max-persistent-connections-per-server = 8 to allow more parallel requests, which the Fedora environment handles well.
Next, the user turns on hardware acceleration for rendering by opening the Preferences pane, navigating to *General* and toggling the option "Use hardware acceleration when available." Fedora’s recent GPU drivers support this feature robustly, and the Tor Browser instantly renders graphics more smoothly.
Tor’s own internal proxy settings also come into play. The user edits the torrc file, adding AutomapHostsOnResolve 1 to bypass DNS lookups for common sites and reduce the number of round‑trips. A carefully chosen Bridge definition—preferably the obfs4 type with a low CircuitsBuildTimeout—helps maintain a faster path to the exit node while preserving anonymity.
Finally, the user customizes the user.js file that lives in the browser’s profile directory. By adding simpler rules for the privacy.sandbox.enabled preference—setting it to false—they reduce the amount of sandboxed JS executed. The user then reboots the Tor Browser, watches the startup time drop from twenty seconds to just a few, and feels the difference in everyday navigation.
Through such targeted adjustments, the Fedora user harnesses the power of a highly secure browser without sacrificing the rendering speed that modern web pages demand. The page loads quickly, scripts execute only when truly needed, and every tab feels as responsive as the polished Fedora desktop. In short, by digging into the configuration and leveraging Fedora’s up‑to‑date graphics stack, the Tor Browser can be tuned to match user expectations for speed while preserving its core mission of privacy and anonymity.
It was a typical Saturday evening, and Maya was grappling with a sluggish web experience on her Fedora workstation. Even though Fedora ships with Firefox as its default browser, she preferred the sleek interface of Chromium. Knowing that Fedora’s modular repositories can keep routers run smoothly, she pulled up a fresh terminal and recalled the tweaks that would bring Chromium back to life.
Setting the Stage: Opening Chromium with Fresh Flags
Maya launched Chromium with a command line that disabled unnecessary features and opened the door to faster rendering:
$ chromium-browser \
--disable-gpu \
--disable-extensions \
--fast \
--enable-npapi
The --disable-gpu flag was there to keep the graphics driver from getting overworked by the heavy GPU‑acceleration that Fedora’s inclusive drivers occasionally choke on. The --disable-extensions option cleared the clutter that could hog RAM. Finally, --enable-npapi opened the door to rich legacy content without the bloat of other plugins.
Fine‑Tuning Rendering Parameters
After load, Maya opened chrome://flags and began walking through the options as if they were annotative notes on a story page. She found Experimental Web Platform Features and turned it on, which allowed Chromium to use the newest rendering engines tuned by Google for speed. Then she enabled Force Dark Mode for Web Contents—a small but useful trick for reducing power consumption on the laptop’s battery. Below the dark mode header, she navigated to Parallel downloading and set it to high, allowing browsers to pull multiple resources at once. Finally, she found Throttling for idle resources and set it to disabled to keep background processes from slowing him down.
Improving Speed by Tweak‑ing Cache and Memory
Maya discovered that chromium’s built‑in cache could be expanded by editing the default configuration file. She opened the .config/chromium/Default/Preferences file and added a small snippet of JSON under the profile section:
{
"profile": {
"cache_size_mb": 1024,
"max_pages_in_cache": 1000
}
}
This change double the amount of recent data Chromium could store locally, reducing the need to fetch assets from remote servers on each visit. She also ran the chrome://memory-conditions diagnostics page, found that large sites were hitting the Memory pressure threshold, and then tweaked the High-DPI display scaling to 87% to lessen the rendering effort while preserving readability.
Testing the Results: A Quick Benchmark
To verify the improvements, Maya opened chrome://gpu and saw that the Hardware accelerated compositing message remained Enabled, meaning the GPU still carried the heavy lifting for video and complex CSS. Blue lights behind the page icon confirmed that no Pending tasks lingered. She then visited webpagetest.org and ran a routerless test, noting that the first contentful paint dropped from 3.1 seconds to 1.8 seconds—a noticeable performance jump on her Fedora system.
A Narrative Return to Normalcy
With the changes in place, Maya felt like she was back in a well‑tuned engine. Her daily tasks—streaming music, checking archives, and working on her project—unfolded without that nagging lag. The story of her Fedora machine was rewritten from a line‐no‑rolling wait to a story that moved effortlessly. She logged into her user account, selected Chromium as the default browser, and closed the desk lamp, confident that the combination of Fedora’s reliability and Chromium’s fine‑tuned accelerations would keep her browsing journey smooth for the nights to come.
From the Fedora Setup to the Firefox Chrome
When I first booted my new Fedora 40 machine, I found myself standing at a crossroads. The default browser that ships with Fedora—Google Chrome—did not sit well with my preference for open‑source software, and I knew I would need a different approach to keep my digital life as clean and private as possible. I chose Mozilla Firefox, the only browser that felt at home on Linux without a grand patron. From there, my adventure turned into a quest to harden the browser’s defenses in a way that felt natural and doable.
Finding the Right Fit for My Fedora User Experience
Fedora’s vast collection of software is accessible through dnf and the robust RPM Fusion repositories, making it straightforward to install Firefox with a single command: sudo dnf install firefox. But installing is only the first step. To truly enjoy the benefits of Fedora’s Security Stack, I needed to weave Firefox into the system’s security fabric.
Turning the Wheel of Security Inward
Once Firefox was installed, I opened the browser, typed about:config into the address bar, and accepted the risk warning. What followed was a quiet, deliberate process of flipping switches. I changed the following settings to lean into privacy and safety: privacy.dns.enabled=true for DNS over HTTPS, browser.newtabpage.enabled=false to shut down auto‑loading ads on the new tab page, and permissions.delegation.enabled=false to block other sites from requesting notifications you never asked for.
One of the settings that turned out to be a game‑changer was privacy.resistFingerprinting. By setting it to true, Firefox began to act like a place of silence, refusing to share the unique fingerprints that trackers use to follow me around the web. Alongside that, I set geo.enabled=false because the last thing I wanted was my GPS exploited by malicious code.
Connecting the Dots with Mechanisms
Next, I wanted to prevent my browser from sending any telemetry back to Mozilla. I set app.normandy.enabled to false, disabling the service that pushes experimental features to my machine. I also switched identity-privacy.restrict-geo-search to true to keep my search queries local, rather than leaking them to the requests’ eyeballs.
When it comes to insecure content, I changed dom.security.httpsOnlyMode to true, forcing the browser to refuse any HTTP requests once an HTTPS connection has been established. I paired this with security.csp.enable for younger manifest systems, keeping those block‑and‑kill tactics at the DNS level.
Fortifying with Extensions and Configuration Files
Beyond the interface, I took the added step of installing uBlock Origin, a lightweight content blocker that I had already used on Windows. By adding the dependency list for firefox-devtools into the policies.json file, I ensured that every future Firefox installation would automatically carry the same set of security guarantees.
Every time I open Firefox from the terminal with a fresh command line I add --safe-mode, I know I’ll see a clean break. In this mode, everything else – plugins, extensions, and even the user-agent string – is stripped to its essentials, meaning the world sees only what I purposely open on my screen. That simple command reminds me that the most powerful security tools are also the simplest.
The Story Continues
As I explore the Fedora ecosystem further, each step reminds me that securing a browser is not a one‑time tweak. It’s a narrative that evolves. I keep my settings aligned with the latest security practises, updating in tandem with Fedora’s own security patches and the latest Firefox releases. Every night, after the system boots into a clean, lock‑secured state, I feel that the story I’m writing aboard my Fedora machine is not only one of taste and preference but also of resilience, privacy, and safety.
The sun was just peeking over the Fedora Server’s front yard when I decided it was time to connect my world to the web again. My preference had always been for the deckhand – the steady, open‑source, man‑made browser that counts on community to patch its shells. Yet lately, while running tests for a fresh kernel build, a shimmering lighthouse in the distance caught my eye: the Brave Browser, a fork of Chromium that promises a treasure trove of privacy shields.
Choosing a Web Ride on Fedora
Fedora, in its current release, ships with a warrior suite of browsers: Firefox with its ZAP (Zero Augmentation Privacy), Chromium with Mozilla’s Jigsaw, and, now, Brave. Each relies on the same underlying policy engine, yet they speak different languages when it comes to security configurations. The decision was less about which browser ran, and more about how each could be cobbled into a hardened profile that would not fall prey to the silent phishing birds stalking the network.
Brave’s Shielded Saliva
When I first opened Brave, the experience felt almost like stepping into a glass cockpit. The interface was sleek, its menu a rustling list of icons that were, at first blush, more aesthetic than functional. But Brave took its name seriously: smart and predictive. The first line of its safety—automatic ad blocking—was already turned on by default, choking off half the invisible trackers that murmur from every webpage. That alone was a victory against the bandwagon of unsolicited data collection that bounces relentlessly from page to page.
Yet, the true game‑changer lay in the “Brave Shields” pane. By default, Brave whispers to the user: “Turn off third‑party cookies.” However, for users on Fedora who want the deepest trust, you can toggle the following settings.
Tuning Brave for Fedora’s Rugged Terrain
1. DNS over HTTPS―an optional but essential feature. Turning on this switch leads Brave to fetch DNS through encrypted channels, knighting your request between your PC and the Internet’s gatekeepers. On Fedora, you can reinforce this for every device by adding “dns-over-https=1” to the application’s .desktop file in /usr/share/applications/. This guarantees that even if your network traffic is on the open, your lookup queries stay clandestine.
2. Network isolation is a synergy between the secure sandboxing of Flatpak or Snap, which Fedora readily supports. Running Brave inside a Flatpak container means the browser’s processes and extensions are isolated from the rest of the system, and any malicious script is cut off from touching your files or your system libraries.
3. GPU Acceleration Off—yes, the very engine that gives you pixel-perfect graphics can also open a window for exploits. In the brave://settings/shields page, uncheck “Enable GPU acceleration.” Some Fedora themes lean on Xorg or Wayland; turning this feature off limits the attack surface without a noticeable loss in everyday browsing speed.
4. Script Blocking—this setting goes as far as disabling Javascript entirely for selected sites, a case‑by‑case approach. Sometimes a website’s flair is just a front; with script blocking, each click is a guarded one.
The Security Specter Stake
I fired up Brave Shields again and, feeling like a digital alchemist, I began swapping out these default gestures. With DNS over HTTPS, your lookup becomes a whisper; with network isolation, your data remains in the same chest as its enforcer; with GPU acceleration disabled, the performance trade‑off becomes a negligible jitter that is worth the security harvest. Each setting caused a small ripple on my Fedora screen: a refreshed tab, a silent lock, the feeling that the Only the Brave can truly command a web browser.
Closing the Circle
Now, as I press Refresh, the beauty of it is that each of these Brave changes synchronizes between Fedora machines whenever you run the update cycle via sudo dnf upgrade. The one consistency in a world of stealthy trackers is that Fedora’s strong permission model and Brave’s configurable shields form a moat that can’t be penetrated by most common threats. The next time a shadowy script tries to sneak in, it will meet a fortified entry point and look rather foolish. This, I realized, isn’t a change of browser—it is a triumph of thoughtful configuration over blind faith.
When the first light crept across the monitor, I opened a fresh Fedora session, the OS humming softly behind the familiar blue wheel. The task ahead seemed simple: let the user’s preferred web browsers run unimpeded while tightening the security bones that hold the system together. Yet, the story of that day was a discovery—one where a small setting change in Zen Browser would redefine how protection feels when the net is wide open.
Morning Beginnings
I launched the default tools, inspected what was pre‑installed, and noted the familiar trio that most Fedora users enjoy: Firefox, Chromium, and the experimental Zen Browser. I had heard whispers about Zen—a lightweight fork that promised speed without compromise. The first thing I did was confirm its version, and the splash screen proclaimed “Zen Browser 2.2.1,” a cut‑edge build that was still in testing.
Choosing the Playground
It was easy enough to let the user choose any browser; Fedore’s policy allows for clean separation between the download and runtime files, so each browser operates in its own sandbox. But security begins with settings, and that is where my focus shifted.
Uncovering the Zen Setting
Inside Zen, I navigated to Preferences > Privacy > Security. The interface looked like a balance scale—one side the familiar “Strict Mode,” the other neutral. I found a toggle labeled “Enable Advanced Protection”, which turned on whenever a user was parachuting over a data‑heavy web. Unfortunately, the toggle was off by default, and almost every installer would misread that as “safe.” This is where I saw the opportunity for a subtle, yet powerful upgrade.
Turning the Page on Privacy
With few clicks, I switched the option to enabled. Immediately, Zen displayed a reassuring banner: “Advanced protection active. Connection unrestricted, privacy empowered.” Behind that message, two new layers were added—a hardened content filter that blocks invisible tracking pixels and a cryptographically secure DNS resolver that hides your queries from unsolicited eyes.
Why a Setting Matters
In browsing, the most silent threats are those that run when we think the house is locked. The more aggressive filters introduced by the advanced setting also reset third‑party cookie permissions and downgrade cryptographic algorithms that are considered obsolete. The system that Fedora runs on is inherently robust, but the browser, being a gateway, can still hide misconfigurations that seep through.
Lessons from the Day
By the time the sun climbed higher, I had logged a small chain of instructions: that users should be nudged, not forced, to activate Zen’s advanced protection—by default it remains on, but a clear visual cue can make the step feel like a natural progression. In the end, the story of that day ended on a simple line: the security of Fedora’s web environment doesn’t just rely on packages; it also relies on the stories we write inside the browsers that our users trust.
The Fedora Horizon
On a quiet weekday the Fedora user perched on a heron‑sized notebook, the screen glimmering with its crisp 4K display. He had flipped through the release notes of Fedora 41 and felt the gentle promise of a cleaner, faster, more secure system. The operating system’s packaging philosophy—robust, open, and timely—had always been his anchor.
Choosing the Browser
There was a quiet deliberation about the browser that would become his window to the world. The default, Firefox, still carried the confidence of the Mozilla release cycle, yet the user also longed for the specialized hush of the Tor Browser. Both were available via the RPM Fusion repositories or the standard Fedora install, but the real test lay in their daily use and how each could be nudged toward greater safety.
Tools and Trust
First, the user spun up Fedora’s “Software” center, verified that the remi‑firefox drop-in had the latest security patches, and installed Firefox ESR 124. After a quick gnome-software refresh, the browser appeared ready. But he also downloaded the latest Tor Browser (v12.0.16) from the official site, flipping the Secure Download switch and letting the package manager appreciate its confidence score. The system felt both more streamlined and more guarded.
Tor’s Hidden Shield
He launched the Tor Browser, watched the familiar splash screen, and opened the Security Settings dialog. In the narrative tone of a wizard adjusting spells, he moved the safety slider down from “Standard” to “Safer.” The browser’s help text reminded him that older scripts and media would be muted, thus shrinking the attack surface. But the user wanted to go further.
Unfolding the developer console and opening the Preferences menu, he nudged the Preferences: General tab’s Settings panel. Here, the History options were chosen to Never store browsing data, and Aggressive Cache was turned off. The Content Blocking array tightened, with Number of Cookies from Third-Party Sites set to Limit. These changes, while subtle, were a fortification against tracking, data leakage, and memory‑based attacks.
Customizing the Tor Circuit
The user opened the Tor Guard page, navigated to the “Exit Nodes” filter, and permuted the Entry Guards: Entry List into “operative only.” The Last Working Exit Nodes section was refreshed to avoid deprecated paths. In the document trail, he added a Torrc snippet:
## Strengthen the circuit by selecting desired exit nodes:
ExitNodes {us} # Use a US‑based exit node for higher throughput
## Strengthen anonymity by increasing bridge use:
UseBridges 1
Bridge [your bridge address]
Adding the bridge increased the resilience against ISP filtering, while forcing a US exit kept locations in a jurisdiction that is less hostile to privacy.
Testing the Fortress
To confirm that the configuration truly locked down the browser, he visited https://check.torproject.org. The page load was swift, the Tor Browser page showing a pin‑pointed IP. He then went to the https://identify.torproject.org site, feeding him a summary: all expected headers were absent, and the JavaScript test returned neutral. This evidence felt like a small triumph in the nightly build of his Fedora machine.
The Fedora & Tor Continuum
When the user closed his browser and opened Firefox ESR, he noticed how the two were insulated. The Security Browser Packages provided by Fedora’s policy ensured that each application received the latest cryptographic fixes, while the customized Tor settings felt like a private locksmith’s set of additional keys. Altogether, the user felt empowered: a system that respected the principle of least privilege, and a browser that allowed him to choose his shield.
In Conclusion
Across the landscape of Fedora Linux, the path to safer browsing lay in modernization, choice, and a willingness to fine‑tune. With Tor Browser configured for a maxed‑security profile, and Firefox ESR held at the campus of community updates, the user stepped forward into a net
Setting the Stage
On a cool evening, I open my Fedora 39 machine and launch the default terminal. From the menu I choose Chromium, the user‑preferred web browser that ships with the system. I am already familiar with its sleek interface, but tonight I have one clear mission: strengthen the browser’s defenses so that every web adventure stays under my vault.
Entering the Privacy Realm
Once Chromium starts, I click the three dots at the top right, pick Settings, and scroll until the Privacy and security section appears. Curiosity nudges me to explore—Google’s default defaults are fine, but Fedora users often want tighter controls. I focus on Cookies and other site data. By unchecking Allow sites to save and read cookie data and enabling Block third‑party cookies, the browser no longer lets malicious trackers linger on my hardware.
Tuning the Content Settings
Next, I open Content settings from the same menu. Here I frame a clear rule: no pop‑ups, no tracking, no automatic playback. I set Pop‑ups and redirects to Block and step through JavaScript to ensure no hidden scripts can hijack my browsing session. After these changes I leave a note in the book‑case of my mind: always verify the Do not track flag is on, because Fedora’s privacy defaults prefer browsing with minimal exposure.
Sharpening the JavaScript Guard
Just when I think I have covered the basics, I recall a clever tip from a recent Fedora security forum: alter Chromium’s internal about:config table. I open a new tab, type about:config, and accept the promise of caution. There I search for user.js and add a single line: user_pref("javascript.enabled", false);—an adventurous move that disables JavaScript entirely, which is safe for highly secure environments and still satisfies my wish to block unwanted scripts on unfamiliar sites.
Cross‑Checking the HTTPS‑First Stance
Fedora’s turning point on web security is the HTTPS‑Only Mode, which enforces secure connections automatically. I enable it under the Privacy and security panel, making sure Chromium will refuse to load any HTTP resources. Consequently, any attempt by a malicious actor to slip a dubious connection through will be caught and dropped by the browser before it even reaches my screen.
Wrapping Up the Journey
After applying these settings, I restart Chromium to make sure everything is solidified. My web browser now sits like a fortress: cookies from strangers blocked, pop‑ups silenced, JavaScript disabled by default, and every request forced through HTTPS. When I revisit my Fedora guidebook, I can see how these tweaks align with the latest recommendations from the Fedora Security Team, keeping the user's experience private and resilient without sacrificing performance.
Sharing the Wisdom
When I share this story with fellow Fedora enthusiasts, I remind them that small changes—unchecking a box or entering a single line of
A Dawn in the Fedora System
On a quiet Sunday morning I powered on my Fedora workstation, the RHEL‑derived rollout of Fedora 41 humming to life. The desktop glowed with its sleek GNOME 45 interface, and the first task that beckoned was to open the internet for a day of research and browsing. That is where the choice of a web browser becomes more than just a convenience—it becomes a flavor of the operating system itself.
Setting the Stage with Firefox
The default installer already ships with Firefox 118, a browser highly tuned for speed, security, and extensibility. Installing the package with the system’s DNF manager is a single command: sudo dnf install firefox. Once launched, the initial welcome screen greets you with a clean, fast interface and the option to sign in with a Firefox account to sync bookmarks, passwords, and extensions across devices. From my own experience, this account sync is an essential part of a seamless Fedora workflow, giving me instant access to my curated tools on the go.
Extensions that Shape the Experience
After the background of the browser
Changing the Game
It started on a gray, late‑afternoon that felt like the kind of day where you stumble over something that changes a habit for years. The Fedora desktop, with its familiar GNOME shell, was a safe, reliable companion for code, emails, and the endless series of tabs that kept the world tapping into the web. Yet every so often I found myself wanting more—more privacy, more control, a browser that respected me rather than the other way around. That was the moment I turned my eyes to Brave.
Installing Brave on Fedora
On the terminal, a single line of dnf install brave-browser had done the heavy lifting. Fedora’s wheelbarrow of dependencies shuffled themselves into place, and within minutes Brave was ready to launch. If the version in the official repos was shy of the latest release, the community shared a .rpm build that installed with a friendly duo of sudo dnf install brave-browser and rpm-ostree refresh. Seeing the “Blazing on a fiery rocket” icon floating over the taskbar felt like being handed a rocket ship to explore the web.
Boosting Bravery with Extensions
Brave’s heart beats with the WebExtensions API. That means you can simply go to the Brave Web Store and punch a Google Chrome‑style button labeled “Add to Brave.” The extensions that drew me in were threefold: privacy, productivity, and aesthetic.
- Just like a shield against unwanted trackers, uBlock Origin sculpted a clean, ad‑free canvas. Its responsive filters were constantly refreshed, keeping my browsing clunky and safe.
- When connecting to a public network, HTTPS Everywhere morphed every link into its encrypted counterpart, delivering a comforting sense that every click was shielded.
- To keep the eye from warping under endless blue screens, Dark Reader flipped every page into night mode on a flick of a switch, turning a glare‑heavy website into a gentle passage of text.
Brave in Daily Life
Once the extensions settled into their roles, using Brave became more than just a mundane click. The first search after login was always an anonymous one; the default promise of a Zero‑Click Tracking enabled protected search made me aware that the browser was listening less than it had ever done. Each extension had its own voice in that story: uBlock Origin whispered "Ad, gone," HTTPS Everywhere murmured a quiet “Secure,” and Dark Reader hummed a soft “Night mode on.”
And when restoring productivity in the midday slump, toggling Brave’s built‑in Task Manager gave a real‑time look at which tab was devouring memory, letting me decide which file to close. The Shortcut Bar let me jump from one extension to another, crafting a personal tool ladder that made every browsing session feel like a brushstroke on a well‑managed canvas.
From the moment I decided to jump into Brave on Fedora, the web felt less like a maze and more like a library with a librarian that only gave me the books I wanted. Each extension added a layer, a protective shield, or a comfort to make the whole experience truly mine, and that is the sense of running a user‑preferred web browser on Fedora with Brave, star‑studded and purposeful.
Choosing the Digital Canvas
On a quiet Thursday, while the rain whispered against the window, Alex decided it was time to turn the digital horizon of the Fedora 38 workstation. The new release felt like a blank page,
Setting the Scene: A Fedora Enthusiast’s Quest for Secure Browsing
Imagine a developer named Alex who has just installed Fedora 38 on a freshly flashed SSD. Alex loves the clean Linux experience but also needs a browser that respects privacy and offers robust protection against tracking. Fedora’s default browser distribution leans toward Firefox, but Alex prefers something more specialized for anonymity: the Tor Browser. The challenge is to install and maintain this user‑preferred web browser on a Fedora system that is constantly pulling in the latest updates from the dnf repositories.
Installing the Tor Browser on Fedora
Fedora mixes a few different package managers. The easiest way for most users to run the Tor Browser is through Flatpak, which isolates the application from the rest of the system. Alex opens a terminal, makes sure the Flatpak repository is added, and then runs:
sudo dnf install flatpak
flatpak remote-add --if-not-exists flathub https://flathub.org/repo/flathub.flatpakrepo
flatpak install flathub org.torproject.TorBrowser
After installation, launching the browser is as simple as typing flatpak run org.torproject.TorBrowser or clicking the new entry in the application menu. The first startup shows the Tor Browser Welcome screen, which guides Alex through connecting to the Tor network. All the heavy lifting of establishing an exit node is hidden behind a friendly wizard.
Keeping the Browser Fresh on Fedora
Because the Tor Browser bundle contains its own versions of Firefox, JavaScript engines, and other components, it does not get updated through the normal dnf upgrade command. Instead, Alex must rely on Flatpak’s own update mechanism. Running flatpak update will pull the latest Tor Browser release from Flathub, ensuring that the crucial cryptographic patches arrive promptly. Fedora’s standard dnf update continues to handle the rest of the system, leaving the Tor Browser untouched by the default updater.
Enhancing Tor with Extensions
The Tor Browser is purposely stripped of unnecessary extensions to keep the codebase lean and to reduce potential attack surfaces. However, recent Tor developments have re‑enabled the ability to install a curated set of add‑ons that respect the browser’s privacy guarantees. Alex wants to make the browsing experience smoother without compromising anonymity. Here is how Alex unfolds the extension story.
First, Alex opens the extension manager by visiting Browsing > Tools > Firefox Add‑ons inside the Tor Browser. Because the Tor Browser runs a specially patched Firefox build, only extensions that explicitly declare “Tor Browser” compatibility are accepted. Alex finds that the current list includes:
uBlock Origin – This ad‑blocker now includes a Tor Network‑Safe Mode that disables any scripts that could leak the exit node address. It also blocks common fingerprinting trackers that can otherwise profile the user between browsing sessions.
NoScript – This extension blocks JavaScript, Java, Flash, and other plugins by default, allowing Alex to enable them on a site‑by‑site basis. In the Tor context, NoScript’s “Security Level: Hardened” is the default, and it reduces the chance of a malicious script breaking the anonymity tunnel.
HTTPS Only Mode – Though the Tor Browser automatically prefers HTTPS connections, installing a dedicated add‑on ensures that any site visited is forced to use a secure connection whenever possible, adding an extra layer of protection.
Cookie AutoDelete – This extension automatically clears cookies that are not essential when a tab is closed. In an anonymity‑centric environment, it helps in preventing cross‑site tracking that relies on persistent cookies.
To add an extension, Alex simply clicks the “Add to Firefox” button next to each candidate. The Tor Browser displays a warning that the extension is safe for Tor use before installation proceeds. Once installed, each add‑on can be tweaked in the “Privacy & Security” settings page to ensure they do not compromise anonymity. For instance, Alex sets uBlock Origin’s Privacy‑First Filtering list as the default, while keeping NoScript configured to disable scripts on every site unless explicitly whitelisted.
Balancing Convenience and Security in a Narrative
Armed with these extensions, Alex begins a day of research. The first link leads to a scholarly article that initially tries to bind a JavaScript API to the page. Thanks to NoScript, the script never executes. When Alex clicks on an embedded advertisement, uBlock Origin blocks it instantly, so no third‑party ad network sends any request that could reveal Alex’s quintuple statement about the Tor entry and exit nodes. The HTTPS Only extension kicks in on a commercial website that had a non‑secure HTTP link in its header; it silently upgrades the connection, preserving the integrity of the Tor circuit.
Throughout the browsing, the Cookie AutoDelete module keeps tabs from bleeding into each other by deleting all non‑essential cookies when a tab is closed. Alex notices a higher degree of privacy: no new cookies appear in the “Session” window at the end of the day, and the browser’s history shows only a list of isolated sites. The story, then, becomes that of a Fedora user who not only feels safe on Tor but also enjoys a smoother experience thanks to the carefully chosen extensions.
Looking AheadSetting the Scene
It was a crisp autumn morning when Maya, a freelance web designer, opened her Fedora workstation. She had spent the last week debating whether to stick with the stock web browser that comes bundled with Fedora or to experiment with something more customizable. Her heart was set on a browsing experience that let her remain in control of every click, every privacy setting, and every piece of data that streamed across the internet. She decided to take the Chromium path—the open‑source backbone of Google Chrome, but free from proprietary bloat. By running Chromium under Fedora, she gained the best of both worlds: a lightweight, well‑maintained operating system and a powerful browser that welcomed extensions.
Choosing Fedora
Maya’s choice of Fedora wasn’t merely about aesthetics. Fedora’s SELinux policies and its default use of the Wayland compositing window system gave her a secure foundation. She installed Chromium from the Fedora Extras repository, ensuring the .rpm package stayed up to date with both the OS and the browser’s rolling releases. When she launched Chromium for the first time, the clean, minimalist interface hinted at the customizability that lay beneath.
Chromium and Extensions
Once ready, Maya opened the add‑on store and began browsing the sea of extensions. There were a few that instantly captured her attention because they addressed her most pressing needs: privacy, productivity, and design. She installed AdBlock Plus to swiftly filter intrusive ads, Privacy Badger to block invisible trackers, and uMatrix—a granular firewall that let her decide which scripts could run on each site. For visual consistency, OneToOne replaced the Firefox default with a dark‑mode user‑style theme that matched the Fedora terminal background.
Beyond these, Maya discovered extensions that could actually change the way she worked. Session Buddy reminded her of previously opened tabs, allowing her to jump back into unfinished projects. The Two‑Finger Scroll extension gave her a more natural scrolling experience, especially when prototyping on responsive web pages. The browser’s built‑in Developer Tools could be upgraded with CSS Grid Layout, a handy debugging extension that visualized every grid container on a page in bright colors.
Enhancing Productivity
With Chromium running smoothly, Maya turned her focus to the extensions that could boost her workflow. The OneTab plugin helped her keep the tab counter down, turning dozens of open tabs into a single, searchable list. Nimbus Screenshot & Screen Video Recorder saved her hours of copy‑pasting by allowing instant capture of a page segment, which she shortened and inserted into her design specifications. For the final piece of efficiency, she added Hover Zoom+, which let her enlarge images only when they hovered, saving memory and keeping the browser fast.
Her installation routine was simple: she ran sudo dnf install chromium, launched the browser, navigated to chrome://extensions, enabled developer mode, and then added each extension via the Chrome Web Store. The Chromium Package Manager in Fedora’s software center made it easy for future updates; as soon as the maintainer pushed a new commit, the package was available for a swift upgrade.
Conclusion
After several days of tinkering, Maya’s Fedora + Chromium setup became efficient, private, and far more enjoyable than a default browser. By choosing the open‑source platform on Linux and complementing it with carefully selected extensions, she had it all: a secure machine, a customizable browser, and a suite of tools that helped her design, test, and deliver work more effectively. When she closed her laptop each night, she could rest easy, knowing that her Fedora workstation and its beloved Chromium browser were ready for her next creative adventure tomorrow.
© 2020 - 2026 Catbirdlinux.com, All Rights Reserved. Written and curated by WebDev Philip C. Contact, Privacy Policy and Disclosure, XML Sitemap.