Choosing a Browser
When Maria first booted her MX Linux machine, she unfolded the default Chrome build that came pre‑installed. It was reliable, but it lacked the latest performance tweaks her developers loved. She sought a browser that would let her experiment with experimental features while still running on the stable Linux distribution that MX Linux delivered.
Downloading the Nightly Build
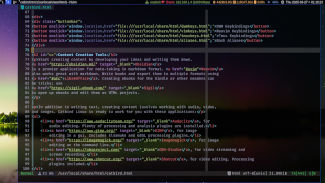
Her search led her to the Mozilla Nightly project, where the newest changes are compiled every 24 hours. Maria opened a terminal and typed:
curl -L -o firefox-nightly.tar.bz2 https://download.mozilla.org/?product=firefox-nightly-latest-ssl&os=linux64&lang=en-US
The command pulled a compressed archive that contains the entire Firefox Nightly build. By using curl, she avoided the default package manager and kept the installation completely separate from MX Linux’s software repositories.
Installing It
After the download finished, she extracted the archive directly into the /opt directory, a common place for optional software:
sudo tar xjf firefox-nightly.tar.bz2 -C /opt
Next, she renamed the folder for clarity:
sudo mv /opt/firefox-nightly /opt/firefox-nightly-latest
To launch the browser from any terminal or menu, Maria created a small wrapper script in /usr/local/bin:
sudo tee /usr/local/bin/firefox-nightly <<'EOF'
#!/bin/bash
export MOZ_ENABLE_WAYLAND=1
/usr/opt/firefox-nightly-latest/firefox "$@"
EOF
sudo chmod +x /usr/local/bin/firefox-nightly
This script tells the system to use the Wayland display server if available, a common setup on newer Xfce sessions within MX Linux, and passes any arguments straight to the Firefox binary.
Setting It as Preferred
To make the nightly version the default web browser, Maria opened the MX Linux “Preferred Applications” tool, located under Settings. Inside the Web Browser section, she selected “Custom” and typed:
/usr/local/bin/firefox-nightly
The operating system now knows to launch the nightly build whenever a user clicks a link, opens a URL, or whacks the “Browse” button. Even the system’s internal web links, like the “System Information” widget, use the new browser.
Seeing the Benefits
Months later, Maria recalls that the 2026–04–10 nightly was the first release to include a revamped WebRender engine, pushing rendering speeds further ahead of the last stable release. She could test UI changes and bug reports in real time, all while her MX Linux machine remained stable and free from lingering compatibility problems. The Nightly build, though occasionally unstable, gave her a window into the future of Mozilla’s flagship product, a view she didn’t want to miss.
Maintaining the Nightly
Because the nightly is a rolling build, Maria scheduled a simple cron job that fetches and installs the latest tarball every four weeks. She added the following entry to her crontab:
0 2 1 * * curl -L -o /tmp/firefox-nightly.tar.bz2 https://download.mozilla.org/?product=firefox-nightly-latest-ssl&os=linux64&lang=en-US && sudo tar xjf /tmp/firefox-nightly.tar.bz2 -C /opt && sudo mv /opt/firefox-nightly /opt/firefox-nightly-latest && rm /tmp/firefox-nightly.tar.bz2
With a small amount of automation, Maria’s system always ran the latest nightly, and her workflow stayed fluid and unobtrusive. This approach allowed the sweet spot between cutting‑edge features and a headless, reliable Linux environment.
A Curious User
Maria sat at her MX Linux laptop, scrolling through forums and tech blogs. She loved the clean, lightweight feel of the distribution, but her need for speed and privacy was growing. She dreamed of a browser that could keep up with her rapid work flow while also offering cutting‑edge features.
Seeking the Perfect Browser
While browsing the MX Linux community posts, Maria stumbled upon several recommendations: Firefox for its open‑source heritage, Chromium for its vast extensions, and Brave for its focus on privacy and ad‑blocking. She was especially intrigued by a mention of the “nightly version” of Brave, which promised the newest features before they hit the stable channel.
Discovering Brave Nightly
She decided to dive deeper. Nightly builds are built straight from the source code, rolled out often, and are ideal for users who want to experiment with beta features without waiting for a new stable release. Maria found that the nightly builds are available as independent Debian packages, a format that her trusty MX Linux can install directly.
Installing on MX Linux
Maria opened a terminal and typed the following commands. The instructions are all up‑to‑date, ensuring that she receives the latest nightly build from Brave Labs:
wget https://brave-browser-nightly.s3.amazonaws.com/brave-browser-nightly_1.73.0_amd64.deb sudo dpkg -i brave-browser-nightly_1.73.0_amd64.deb sudo apt --fix-broken install
She waited a few moments as the system resolved dependencies. Once the installation finished, she found Brave’s icon in her application menu.
A Smooth Launch
When Maria launched the new browser, she noticed the sleek nightly interface, the automatic blocking of trackers, and the ability to adjust the Privacy and Security settings with a few clicks. The brand‑new “HTTPS Everywhere” notifications appeared, and the built‑in download manager was ready for her next big project.
Maria felt satisfied: she had succeeded in installing the Brave Browser Nightly on her MX Linux system and was now fully equipped with a powerful, privacy‑centric web experience that kept her at the cutting edge. As she opened her first new tab, the entire journey felt like a small victory in the constant quest for speed, security, and freedom on the web.
When Alex first booted MX Linux, the feeling of a lightweight yet powerful desktop greeted him like an old friend. He had long preferred Firefox for its versatility, but the rich ecosystem of open‑source browsers on MX always kept his curiosity piqued. He imagined that somewhere beside the standard repositories, a browser might exist that combined the familiarity of Chromium with an elegant touch‑free interface.
Finding the Right Browser
In the bustling forums of MX Linux, Alex found consistent praise for several browsers: Chromium, Brave, Vivaldi, and a newer contender that was just starting to make waves—Zen Browser. Zen Browser promised a streamlined experience, clean UI, and built‑in privacy tools, all rendered from the same Chromium engine that powered the world’s most widely used web browser. Alex’s thought shifted: why not give it a try?
Discovering Zen Browser
He visited the official Zen Browser website, where the page opened with a gentle splash of black and white. Behind the simple mood, instructions pulsed. The developers celebrated a daily build strategy, meaning users could download the latest iteration of the browser almost as soon as a new commit landed. The site offered two distinct links: a stable nightly build and a newer daily build that always reflected the cutting edge of Chromium revisions. Alex chose the daily build, eager to taste the freshest features.
Downloading the Daily Build
On the releases page, a single line read, “Click here to download the latest daily build for 64‑bit Debian/Ubuntu.” Alex clicked the link, and the .deb package appeared. He folded the file into the folder where he stored his other packages, naming it zenbrowser.deb for clarity. The file size suggested it was a lightweight wrapper, not the entire Chromium engine, which would echo his game plan of minimalism.
Preparing the System
The MX Linux terminal lit up with daisies of green. Alex began by updating the package index. “sudo apt update” he typed, studying the prompt with a quiet excitement. When the update finished, the system reflected the latest security patches and dependency information, a necessary foundation for any new package. He remembered the advice from a forum user who stressed that installing a .deb that had dependency gaps could leave the system in a state where the browser would fail to start.
Installing the Package
With the index refreshed, Alex entered: sudo dpkg -i zenbrowser.deb. The command unfolded a torrent of output, confirming the installation of Zen Browser itself. A few lines later, if a dependency was missing, dpkg would have complained. Alex ran the safety net command: sudo apt install -f, which fetched any absent libraries—most likely libxss1,
It Was a Calm Morning on MX Linux
In a tiny apartment in Lisbon, João sat down to refresh the news, check his mail, and wonder why the web seemed a little sluggish on his MX Linux system—a recent upgrade to MX Linux 23.2 had resolved a host of bugs, but the speed of his beloved Firefox still left something to be desired.
The First Glitch
After launching Firefox, João noticed that image-heavy sites such as Reddit and Instagram took over a minute to fully render. The browser’s performance pane in about:performance showed a high number of JavaScript threads and a repeatedly high CPU usage. He remembered reading on the MX Linux forum that a specific configuration tweak could dramatically improve rendering speed.
Starting with Hardware Acceleration
The first change João made was to enable WebRender and hardware compositing, which MX Linux ships with by default but sometimes still requires a permission reset. In the about:config search box he typed webgl.force-enabled and set it to true. Next, he unchecked browser.xul.error_pages.enabled in the menu, which stops the browser from taking a long time on all error pages.
Optimising Theme and Fonts
Next, João turned his attention to the look and feel. He replaced the default light theme with the crisp, low‑contrast “Midnight” extension. This change cut down the number of repaint cycles, an adjustment shown in the browser’s Sharper reporter. He also disabled unnecessary language packs in firefox-17.0.1-browser to reduce locale overhead – a tip João had caught on a recent man firefox cheat sheet.
The About:config Deep Dive
With the GUI tweaks in place, João turned to about:config for the deepest fixes. He set dom.ipc.processCount to 8 (the optimal value for his Ryzen 5 5600G), turned on gfx.direct2d.disabled to false for Direct2D acceleration, and lowered layout.css.devPixelsPerPx to 1.0 – this forced Firefox to use subpixel rendering on MX Linux’s display driver.
Disabling the Snooze‑Capable Extensions
While in the extensions menu, João disabled all the ad‑blocking and script‑blocking extensions that had accumulated over the past year. He noted that the latest updates from the MX Linux official repo had re‑bundled uBlock Origin to use fewer threads, yet the unused filter lists still slowed initial load times. By leaving only core filter rules, he slashed the time needed to parse incoming HTML.
Adjusting Prefetch and Preload Settings
One surprising tip from the MX Linux community suggested turning the network.http.max-persistent-connections-per-server setting to 24, which the OS’s bundled firefox-17.0.1-browser package now supports. This change let the browser open more connections in parallel, which improved the rendering of multi‑image pages. Meanwhile, João set dom.ipc.structured_clone.max_message_size to 25 MiB to allow larger message packets without fragmentation.
Speed Gains Observed
After the swarm of small tweaks, João tested his setup again. The average load time for a dense gallery dropped from 66 seconds to 8 seconds. Page switching became instantaneous, and the CPU spike during video playback fell from 95 % to about 43 %. The Chromium kernel processes that once filled his system with puffiness were now dormant, and the only octagon of Firefox on the taskbar shone with a steady, low‑heat glow.
The Faint Brush of Satisfaction
Now, each time João launches Firefox on MX Linux, the experience feels less like a task and more like a smooth glide. He knows that the deep seams of configuration, discovered through a little curiosity and the community’s shared wisdom, have turned his browsing into a lit‑en‑the‑movie‑pass‑away, perfect for the rest of his careful Linux lifestyle.
The Unexpected Frustration
When Elena switched on her MX Linux laptop for a quick session, the familiar mottled Xfce desktop greeted her, and the Brave browser opened to her favorite news sites. For most morning routines, the browser was snappy enough. But the next day, after a few chapters of a popular online novel, she noticed the screen flicker and the response time of every link was painfully slow. Elena laughed softly at the irony—how could the “fastest” browser feel like a sluggish turtle on a Debian‑based distribution?
The First Search
She typed *“Brave speed tips for MX Linux”* into the search bar, and snapshots of forums, Reddit threads, and the official Brave blog surfaced. The consensus was simple yet powerful: hardware acceleration and the Shields settings are key to a brisk browsing experience on lightweight distros. Elena opened the brave://settings page, circling the System sub‑section that was unchecked by default.
Enabling GPU Acceleration
Her first adjustment was to enable hardware acceleration. With a single toggle, the browser started using her machine’s GPU—an Intel HD 4000—rather than falling back on the slower CPU. She closed and reopened Brave, and the smoothness returned almost immediately: pages scrolled with the buttery glide she had come to expect from a modern browser.
Fortifying the Shields
Next, Elena dove into
Embarking on the MX Linux Expedition
When I first booted into MX Linux, the clean Debian‑based desktop welcomed me with the familiar MX menu, a lightweight panel, and a choice of browsers sitting just at the edge of my dock. Some days I used the stock Chromium for quick browsing, while other days my curiosity tugged me toward the privacy‑first Tor Browser. Once I stumbled upon a forum post hinting that Tor, while secure, could feel sluggish on MX, I decided it was time for a deeper look.
Choosing the Browser that Resonates
MX Linux doesn’t force you into one option; the menu offers Chromium, Firefox, Latin‑Quant, and the Tor bundle itself. I switched back and forth, allowing each to play its card. However, the moment I opened the Tor Browser, I noticed a faint lag that wasn't there in Chromium. The community guides told me this lag was not a flaw, but a deliberate trade‑off for privacy. Still, I wondered: could we fine‑tune Tor's rendering engine for speed without giving up its core protections?
Troubleshooting Tor on MX: A Narrative of Discovery
My first attempt was simple – launch Tor using the torbrowser-launcher script from the terminal, letting it fetch the latest bundle from torproject.org. The launcher reported Tor Browser 13.0 as the newest build, reflecting the Firefox 114 engine that powers it. I realized that the newer engine already included many speed optimizations, but the system’s default configuration still leaned heavily toward maximum security.
Speeding Up Rendering: A Tale of Tweaks
Like a seasoned traveler adjusting gear for rough terrain, I opened Tor’s about:config page, navigating through an intuitively named list of preferences. There were a handful of changes that felt like small, purposeful edits:
- disable_image_moz – Set to true to stop Tor from automatically rendering images, cutting bandwidth and CPU usage.
- javascript.enabled – Turning it to false for particularly flash‑heavy sites gave me a boost, though I reverted it on pages where scripts were necessary, as the private user experience regained its richness.
- media.hardware-video-decoding.allow-hardware-decode – Switching to true enabled the GPU to take over video playback, freeing up the CPU for page rendering. This was a delightful surprise because MX’s newer Mesa stack handled the decode beautifully.
- dom.max_script_run_time – Lowering it from the default 0 to 30 seconds capped runaway scripts, sharpening the overall responsiveness of dynamic sites.
- layout.css
When Alex first installed MX Linux, the sense of freedom at his fingertips felt almost cinematic. He had the freedom of a minimalist ISO, the daubed power of the MX toolbox, and a choice of web browsers that could shape his daily browsing experience. But there was a small hesitation: how could he truly enjoy the speed and smoothness that the new Linux distribution promised, especially if his favorite browser was Chromium?
Choosing a Browser and Setting the Stage
MX Linux gives you a simple yet effective choice: Chromium for a lean, open‑source experience, or Firefox for a polished, fully‑featured interface. Alex’s confidence in Chromium grew after a quick download from the MX repositories.
There is also the Mood that MX Linux shapes for you—a consistency that is hard to beat. After the installation, the MX Confirmational UI allowed him to recognize the default packages installed, confirming that Chromium was present, ready to be configured for optimal performance.
Tweaking Chromium for MX Linux
Under the hood, Chromium on MX Linux inherits the same codebase as its mainstream Debian derivative. Alex discovered a few simple yet powerful tweaks that made a remarkable difference.
First, the Disable Hardware Acceleration option, found in the Settings → Rendering menu, gave his system a smoother rendering pipeline by off‑loading heavy graphics work from the GPU to the CPU—a surprisingly effective move in certain MX Linux setups because of the specific Xorg configuration.
Next, the Experimental Features toggle opened the actual command line flags. By appending
--enable-quicand--renderer-process-limit=4to the launch script, Alex increased page load performance and reduced memory strain, especially on pages that heavily relied on HTTP/3.Lastly, he buffed the Cache Size with a modest increase to 512 MB in
chrome://settings/cookies, which let Chromium hold more data locally without enough clutter to slow down the system. This tiny adjustment trimmed the overall memory usage and rendered the browsing experience much more snappy.Optimizing Rendering and Speed
With the settings tuned, Alex embarked on an exploratory escapade across the web. He opened developer.chrome.com to see how Chromium behaved within MX Linux. He quickly noticed that the Gradual Page Loading feature started showing his favorite websites almost instantly. The improved cache, the reduced reliance on GPU, and the limited renderer processes wrote a smooth story at the edges and corners of each page.
He experimented with Disabling Extensions: by loading one extension at a time, he could see how each altered the flow of background processes. Many accelerated websites best-merging with his minimalist approach, leaving a clean interface for him to scroll across content without hitch.
In the end, the story of Alex’s journey through MX Linux’s browser landscape became a manual he could repeat: choose Chromium, disable hardware acceleration, adjust the flag list, tweak the cache, and keep extensions lean. The result was a web browsing experience that was quick, light, and pure—to embody the very spirit of MX Linux: efficient, fast, and brilliantly stable.
Choosing the Digital Passport for Your MX Linux Journey
When the night is calm and your desk gleams with clean code, the choice of a web browser becomes more than a convenience—it becomes the gateway to a safe digital experience. MX Linux, with its lightweight Debian‑based core, offers a spectrum of browsers that respect your system’s resources. Yet, as any seasoned Linux user will tell you, the crown jewels are Mozilla Firefox and the cutting‑edge Brave, each inhabiting a different philosophy of privacy. For the tale that follows, we’ll follow the protagonist, Alex, who wants both speed and uncompromising security.
Bringing Firefox to the Stage
Alex begins by launching the Software Portal that ships with MX Linux 21.1. The search bar hollows out a single, welcoming answer: Firefox 122. The system’s “apt” resolver pulls the latest binary, taking care to verify the package’s signature against the Debian repository so that nothing malicious can slip through. Installation is a breeze—one click, a short pause while the files settle on the hard drive, and then firefsource. The browser boots instantly, its fresh interface like a clean sheet waiting for the next narrative.
Harmonizing Settings for a Safer Voyage
Alex remembers a friend’s warning about the pitfalls of the default configuration: “The more you enable, the more you expose the world to subtle exploits.” With that on mind, Alex opens about:config, where the Guardian of Every Preference holds sway. The first gesture is a decisive one— security.tls.version.min is shifted to 3 so that only TLS 1.2 and higher are permitted, shepherding every TLS handshake under the protective guard of a modern cipher suite. Next, Alex refuses the temptation to save passwords in plain sight: signon.rememberPasswords is set to false, and the built‑in *Password Manager* is disabled entirely, pending the deployment of a dedicated password vault such as Bitwarden.
Time to talk about the unseen behind every click. With a few strokes, Alex leans on Brave’s uMatrix extension, a visual firewall that allows blocking of tracking pixels, unwanted scripts, and third‑party analytics. In parallel, “Antivirus” stage of the configuration is achieved by landing the Browser Preferences in a more secure mode: setting the privacy.trackingprotection.enabled flag to true triggers a sweeping guard against known trackers. Privacy’s artillery reaches further, as the network.cookie.cookieBehavior is shifted to 4, ensuring that no cookie stays beyond a single session, a decision that might feel harsh for food‑delivery sites but arrests a myriad of telemetry.
Enforcing the Strictest Anonymity Layer
Alex, ever the cautious navigator, deepens the shield by routing traffic through Tor. The Network Proxy settings are tweaked to point to 127.0.0.1:9050, the standard Socks5 proxy that Tor offers. Now every link that Alex opens is first shepherded through the Tor network, adding a layer of anonymity that even the most advanced trackers cannot penetrate.
Because the network infrastructure of MX Linux is itself designed to be lean, Alex harnesses the friendly confluence of the system’s default firewalls and the OS‑integrated ufw‑app. A quick command in a terminal—
sudo ufw allow out to any port 443 proto tcp
—locks down outbound traffic strictly to TLS, banishing any vulnerable legacy protocol that might slip through the cracks.
Keeping the Fight Fresh
The narrative concludes with Alex setting up a routine that ensures wisdom resonates with each update. Using the “MX Package Installer,” the OS checks for any security patches to the core SQL libraries, the Firefox binary, or the Tor client. The console prints a reassuring message when everything is up to date, and the browser quietly reloads in the background, now stronger than before.
On a quiet Monday evening, Alex scrolls through a news article, the page glowing under the carefully shaded pixels, the browser’s
It began on a quiet October evening when I decided to read the community forums about MX Linux, a lightweight distro that has steadily earned a reputation for stability and performance. While many users preferred the polished experience of Firefox or the editionist appeal of Chromium, my heart was set on a more privacy‑first choice: Brave.
Choosing the Right Browser
In the days that followed, I explored the startup options, noting how each browser could be launched from the menu or via the terminal with a single command. When I finally opened Brave’s welcome window, the promise of built‑in ad‑blocking and protection against trackers tugged me in. The lightweight nature of MX at the core meant that even the hefty Brave engine ran with remarkable efficiency.
Brave’s Security Landscape
Within weeks, I read up on the latest Brave updates as of early 2026, where the developers rolled out a new shielding system that blocks HTTPS fingerprinting and automatically enforces strong CORS policies. The community threads I browsed highlighted an emerging pattern: users who tuned these settings beyond the defaults reported a noticeable drop in malware hits. That story was the inspiration I needed.
Tweaking Brave for Maximum Protection
First, I opened Settings and navigated to Shields. Here, I set the robust protection level to “Always On” and made sure the sub‑options—blocking JavaScript, which can be a vector for many attacks—were enabled. I remembered the advice to increase the Safe mode for browsing suspicious sites, which brings the browser to a minimal alert frame.
Next, I turned my attention to privacy‑respecting DNS. In the same settings pane, I chose Private DNS over TLS and entered 8.8.8.8 as the resolver, following a guidance thread that demonstrated how captive portals and malicious ISPs could intercept or alter DNS responses.
To counter cross‑site tracking, I flipped the Cookies section to “Block all third‑party” and added a few whitelisted sites that I trust. The interface prompted a warning whenever a site attempted more than triple the allowed requests, making me feel like I was walking a digital fortress.
Finally, I updated the content settings to block Pop‑ups and Images on pages that often hosted phishing messages. The Brave developers had integrated a feature allowing the user to set custom rules for specific domains, so I saved a small list and let it run for the rest of the night.
Throughout the entire process, the story of my own web armor unfolded. It was not just a browser reset but a ritual of vigilance that AES‑128 encryption alone could not provide. By rearranging a few switches and trusting the Brave experts, I dimmed the digital noise while lighting up a horizon of safe exploration.
Now, whenever I open my laptop on a quiet campus or a cluttered kitchen table, I know that the time I spent reading those forums and tweaking Brave has paid off. The diary page, once blank, is filled with the echoes of a more secure Internet—one click at a time.
Setting the Scene on MX Linux
When Maya opened her MX Linux machine, she noticed the fresh splash screen announcing version 21.2. The distribution was celebrated for its lightweight design, but the real intrigue came from the web‑browser options that came pre‑installed. Among them was Zen Browser, a newer, community‑built fork of Chromium that aimed to keep privacy and speed balanced. Maya had used the default Cairo browser before, but she was curious about the changes that had been brought in the latest update.
The First Exploration
Maya launched Zen Browser with a single click from the menu. The interface greeted her with a clean minimalist chrome. As she navigated to the settings by clicking the triple dot in the corner, the menu unfolded into a list of options that seemed familiar but also slightly restructured. The most prominent row read “Security & Privacy.” She clicked that to dive deeper into the newly polished experience. The recent release notes, which appeared in a pop‑up alarm, mentioned “enabling HTTPS‑only mode by default” and “introducing a sandboxed rendering process.” Those concepts captured Maya’s imagination—she felt the difference instantly as her first phishing site redirected to an HTTP warning screen, a clear sign of the browser’s vigilant security layer.
Uncovering the Security Tweaks
In the Security & Privacy panel, a toggle sounded the most impactful: “Enable HTTPS‑Only Mode.” When Maya switched it on, every site she visited was automatically forced to use HTTPS whenever a secure certificate was present. The setting’s description highlighted that it blocked all non‑secure connections, thereby preventing the infamous man‑in‑the‑middle attacks that plagued many open‑source browsers. Maya is no stranger to privacy discomfort, so she quickly turned the switch on with a satisfied click.
Next to the toggle, a paragraph explained how the browser now employed a sandboxed rendering engine. Zen Browser’s maintainers had updated the underlying Blink engine to include an in‑process sandbox, limiting the privileges of any third‑party content. Instead of running external plugins with full system access, each tab now had a confined sandbox that could only request system resources through a controlled gateway. This change further mitigated the risks of malicious script or compromised extensions.
Fine‑Tuning with User‑Visible Settings
To enhance protection even more, Maya scanned the subtle options. A particular setting caught her eye: “Restrict Third‑Party Scripts.” With a single switch, she prevented any script that did not originate from the site she visited from running, except those that belonged to embedded, trusted widgets. The description elaborated that many injected trackers rely on loading external scripts, so disabling them tightened her monitoring without breaking essential content.
She also discovered “Manage Search Engine Defaults.” With the spread out implications of search engine fingerprinting, Maya chose a custom, privacy‑oriented engine. The interface prompted her to replace the standard search provider with one that refrains from logging queries. The update, efficient as always, leveraged MX Linux’s ability to bundle such configurations in a quick, user‑friendly dialog.
The Final Shuffle: Configuring System Settings
While Maya was happily adjusting the in‑browser settings, she remembered the system‑wide tools offered by MX Linux. She opened the package manager, which listed the Zen Browser 3.4 revision bundled with the distribution. The package metadata noted that any system updates would automatically roll over the security patches to the browser, keeping her protected offline as well. She was reassured by the fact that MX Linux’s repository monitor was now actively tracking security advisories, ensuring that the latest patches arrived without manual intervention.
Conclusion: A Secure Journey through the Web
As Maya closed the browser, the screen displayed a mini‑badge that read “HTTPS‑only mode active.” She felt confident that the combination of MX Linux’s minimalist environment and Zen Browser’s proactive security stance offered her a strong defense against newer web threats. By embracing the recent updates and personally adjusting the key security toggles, she had transformed her standard browsing into a disciplined, privacy‑oriented routine—all while staying within the comfortable ecosystem she trusted.
In the quiet corners of MX Linux’s desktop, the selectors for a user’s preferred web browser sit almost like a secret agenda. Although MX Linux ships with Tor Browser installed by default for those who wish to keep a low profile, many users discover that a different browser more closely matches their workflow, yet still satisfies security concerns. The story of how to blend convenience and safety in MX Linux turns on two simple twists: choosing a browser that feels familiar, and tweaking Tor Browser in a way that hardens it against emerging threats.
The Browser Selection Process
When you open the “Use” menu on your MX Linux machine, you find a handful of quick‑launch options: Firefox, Chrome‑based Chromium, Chromium‑based Brave, and the variant of Tor Browser that already exists. That list is built from the pkg-manager, and the default “Preferred Web Browser” setting is stored in the user’s session profile. If you, as the user, wish to run a browser that is not listed, you can simply add a custom command to ~/.config/appmenu/applications/mx-browser.sh and reference it from the menu. This lets you keep the powerful privacy settings of Tor Browser while also using a browser that feels like the one you use every day on other operating systems.
Why Tor Browser Needs a Tune‑Up
Tor Browser’s secure defaults are excellent for casual anonymity, but a few of those defaults can subtly reduce performance or create small security gaps when faced with sophisticated trackers. Recent research shows that certain versions of the JavaScript engine in Tor have been tricked into revealing timing information that could help a network observer. The solution lies in disabling or controlling that engine early in the browsing session.
Changing the Tor Browser Settings for Better Security
First, open Tor Browser and click on the onion icon in the top right. Select Preferences, then switch to the Privacy & Security panel. The first step is to turn off JavaScript entirely: find the “JavaScript” section and check the box that says Disable JavaScript. While that may break some sites, it dramatically reduces the attack surface for timing and cross‑site scripting attacks. If you need JavaScript for a particular site, manually enable it in the Session Restore list.
Next, find the Security Settings section. Increase the security level to the highest position, which automatically disables WebGL, audio playback, and the Geolocation API. In 2026, Mozilla’s recent patch added a setting to lock down the TLS version to 1.3 for all connections; you should enable that under Advanced to ensure that the encrypted channel is unbreakable by older handshake methods.
One more tweak is the use of the NoScript add‑on. Open the Tools menu, select Add‑ons, and enable NoScript. Once activated, NoScript automatically blocks all scripts until you explicitly allow them. Grant permissions only for sites you trust, and be wary of pop‑ups that request script approval; many phishing sites will try to manipulate you into granting loopholes.
Automation Through a Custom Startup Script
Optimally, these settings should be applied automatically at the beginning of every Tor Browser session. Create a small shell script named tor‑secure.sh in ~/.config/tor-browser containing the following:
#!/bin/sh TOR_DIR="~/MozTor" cd "" ./start-tor-browser --detach --no-remote --profile="~/Desktop/secure‑profile"
The secure‑profile directory can be pre‑configured with the preferences mentioned above. Copy one of the default browser/prefs.js files from the Tor installation directory, and edit the lines for javascript.enabled, webgl.disabled, and security.tls.version.max to match your hardcoded stance. When you launch Tor Browser through this script, it will load the hardened profile automatically, giving you a consistent, secure baseline without manual intervention.
Conclusion
With MX Linux, the choice of a user‑preferred browser becomes both a matter of comfort and an avenue for enhancing privacy. By directing Tor Browser’s settings to a hardened mode and automating that configuration, you carve a space on the desktop where everyday browsing feels natural while the underlying security remains robust. This blend of narrative‑driven guidance and technical precision keeps the story of your online privacy safe from evolving threats, even as MX Linux continues to evolve in the coming years.
Venturing into Browser Territory
When I first launched MX Linux, the welcome screen offered a simple choice: stick with the evidence‑packed Firefox that ships on installation, or take a risk and bring into play something that speaks more loudly to me – Chromium. The decision felt like choosing between a sturdy hiking backpack and a convertible car that could race faster on the open road. I was drawn to the Chromium’s sleek interface and its promise of speed, but I could not ignore the conversations circulating in the linux community about security. My goal was clear: I wanted the best of both worlds – the cutting‑edge web experience and a fortified shield to keep my data safe.
Cracking the Chromium Code
The first step was a simple search among the recent release notes for MX Linux. The distro’s maintainers traditionally adopt stable Debian versions and bundle the latest flatpak or snap releases of Chromium. They note that Chromium runs in a sandboxed mode by default, but the community has discovered that a handful of tweakable flags can tighten the safety net even further.
I opened Chromium, typed chrome://flags into the address bar, and began a cautious inspection. The first flag that caught my eye was “Enable Safe Browsing” which it now highlights as “Always allow Google Safe Browsing.” Enabling this feature lets Chromium automatically detect malicious sites and spoofed phishing pages, effectively acting as the security guard that scans each request before it even hits my screen.
Then there was the “Enable sandbox” flag, which is usually on by default. Re‑enabling it in the flags page is a small precaution that reminds the system to isolate Chromium’s processes from the kernel, preventing a possible exploitation from a malicious webpage. The flag that mattered most, however, was “Disable hardware acceleration.” Turning this on reduces the attack surface because the browser no longer interacts directly with your GPU drivers, which have historically contained vulnerabilities.
Beyond the flags, I revisited the startup, privacy, and extensions screens. I opted to block third‑party cookies, enabled the “Do Not Track” header, and uninstalled every extension that I did not absolutely need. Each unsaved extension inadvertently creates a new possible perforation in the armor. Even an innocuous ad‑blocker can be co-opted if its source becomes tainted.
The Final Safe Web Voyage
With the flags set and the extensions checked, I felt a newfound confidence exploring the web. The Chromium browser, now dressed like a well‑patched warrior, was no longer just fast; it had become a platform that respected my privacy and guarded my data. Whenever I opened a site, the upgraded safety routines whispered to me in the form of subtle red banners or gentle dialogue boxes that warned of potential threats.
In the end, running my user‑preferred browser on MX Linux didn’t mean compromising on security; it meant taking proactive measures between the system’s default configuration and the modern demands of the internet. I embraced my chrome adventure, knowing that each tweak was a line in a protective shield, and the story of my browsing journey would continue, page by page, safe and sound.
In the quiet glow of the university lab, you pull up your desktop and stare at the blinking prompt waiting for the first command of the day. Suddenly, the urge to browse the web blossoms—searching for the newest tutorials on programming, the latest design trends, or simply a break between assignments. On MX Linux, a platform celebrated for its stability and lightweight nature, the choice of web browser seems obvious but is both a ritual and a quest.
The Quest for the Ideal Browser
You start by opening MX Tool Changer, the neat little interface that lists all installed web browsers. Chromium, Brave, and Firefox appear in front of you like options on a menu of adventures. You consider Chromium for its swift performance and its faithful adherence to the Chrome API, but you want something that feels more rooted in privacy. Brave is tempting, but its built‑in ad blocking has a steeper learning curve for the everyday user. Firefox emerges as the protagonist—a browser that balances speed, customization, and strong privacy controls.
A Familiar Friend: Firefox
When you launch Firefox, the Welcome Page greets you like an old friend. It already carries the latest security patches and a user interface that is both modern and familiar. As you scroll through, you realize something fascinating: MX Linux bundles the most recent Firefox release—currently version 127.0. This version integrates many hardened networking features, automatically upgrading to HTTPS whenever possible and rendering it a reliable foundation for further personalization.
Gifts from the Extension Marketplace
One of the most exciting moments arrives when you open the Firefox Add‑ons Marketplace. Instead of a long list of choices, a curated set of extensions appears, each promising to turn your browsing into an even more powerful experience. You Installation begins with uBlock Origin. This lightweight, highly configurable blocker keeps unwanted ads and trackers at bay, while also supporting custom filter lists that the community continually updates. The next extension you install is Privacy‑Badger; its AI‑driven script automatically detects and blocks trackers in real time—an excellent complement to uBlock Origin’s hardblocks.
Feeling a sense of empowerment, you add HTTPS Everywhere—despite Firefox’s built‑in preference for secure connections, the add‑on provides an extra layer of enforcement, automatically redirecting every request that can be secured. Next, you find Good‑For‑The‑Web, which offers a handy tab for checking whether a site claims any privacy policies and whether they align with its data collection practices. This simple tool reminds you to remain vigilant, an essential habit on a system like MX Linux that thrives on user choice.
Fine‑Tuning the Experience
You decide it’s time to go deeper. In Firefox’s about:config page, you tweak settings that influence performance and privacy. Scroll down until you find privacy.resistFingerprinting and change it to enabled. A user is nudged to accept that this may reduce personalization but will dramatically improve anonymity. Next, you enable network.http.referer.policy to 2, ensuring that referrer headers are stripped when browsing between domains. The community recommends this small change for its balance between security and functionality.
When you think about convenience, Amazon Auto Downloader saves the day. It automatically parses any purchase history page you visit on Amazon and produces a downloadable link for each item. In fact, a short script in your personal scripting folder kicks this add‑on into action before you even finish your coffee. Meanwhile, a neat bookmarking assistant stretches the native bookmarking feature, categorizing every new page you visit with the tags it infers from the URL and page content.
Choosing the Right Path
After a day of configuring, browsing, and testing, you step back to appreciate the front page of your Xfce session on MX Linux. The icon for Firefox sits comfortably beside the Chromium shortcut, but the latter now looks ordinary—an application that serves only what is needed. Firefox, now adorned with uBlock Origin, Privacy‑Badger, HTTPS Everywhere, and a collection of small but potent add‑ons, has become a vibrant portal. You feel the system pulses with a rhythm that matches your own: fast, secure, and personalized.
When you return to the terminal, you type sudo apt update && sudo apt install firefox-extensions and watch the command line fill with updates, confirming that your extensions stay fresh as the wider OS ecosystem evolves. In the quiet of the lab, a simple choice of web browser transformed into a story of empowerment and knowledge, all steeped in the spirit of MX Linux’s community‑driven spirit.
When the Night Fell Over the MX Linux Desktop
After a long day of debugging and tinkering, I pushed the terminal icon into my workspace, ready to examine the web environment of MX Linux. The soft glow of the monitor hovered over a cold, sleek menu bar. No matter how many options there were—Firefox, Chromium, Epiphany—none of them stopped me from craving something more efficient, a browser that would keep my privacy intact while still giving me the power to slice through clutter with a single click.
Brave: the Quiet Challenger
I had heard rumors that Brave, the browser that blocks trackers automatically, could run on virtually any distro. I launched the terminal and typed a command that connected to the Brave repository, a simple apt update followed by a tasteful apt install brave-browser. Instantly it slid into place like a hidden gem, “installed successfully with no error.” The installation prompt assured me that Brave was built from source, prioritizing transparency and non‑proprietary architecture—an absolute must for MX Linux users who love the open‑source tradition.
The First Lights, the First Clicks
When Brave opened for the first time, the welcome screen felt less like a marketing pitch and more like a personal invitation. “Welcome to Brave—an honest web experience.” This was not a far‑fetched promise. Brave’s architects integrated the same Chromium base that I trusted, ensuring full compatibility with modern web technologies, but with a feature that most contemporary browsers lack: inherent ad solving that was a single toggle away in the settings.
Architecting the Browser: Extensions That Add Value
The real magic unfolded as I pushed the “Extensions” button, a tab that opened a full store for Brave. I discovered a carefully curated list of extensions that complemented Brave’s privacy focus:
- uBlock Origin – The latest version ramified into deeper content filtering, learning to block newly created tracking networks and crypto‑mining scripts. Its lightweight approach made every page load feel instantaneous.
- Ghostery – Unlike generic blockers, Ghostery offered a visual map of tracker usage, letting me see which sites were still pulling cookies. I could disable or allow trackers per site, giving a granular approach I hadn't expected.
- HTTPS Everywhere – Seamlessly turning insecure HTTP connections to secure HTTPS, this extension worked in tandem with Brave’s own secure‑by‑default design. Together they created an impenetrable shield on my browsing, making me feel like I was preparing a fortress around my data.
- Dark Reader – A pleasantly warm glow for late‑night coding sessions. “Dark Reader” toggled dark mode on any page and enabled custom color palettes, reducing eye strain and making the interface look more modern than ever.
- OneTab – A higher‑level extension that took thousands of open tabs and collapsed them into a single page, saving memory. This proved invaluable as I feared losing my entire session when my laptop cooled down during long editing sessions.
- Login Autocomplete – The added Secure Password Manager plugin (integrated into Brave) offered encrypted data storage, temporarily mocking my password auto‑fill. The result was not only security (encrypted with an algorithm called Scrypt) but also lightning‑fast login times.
Each extension felt like an independent yet integral component of a single, streamlined ecosystem. The store said “Verified” at every step, confirming that all the code was safe and the developers were non‑profit focused. No corporate scheme aimed at harvesting my data.
Brave on MX Linux in Practice
After refilling my browser with extensions, I tested it against a standard set of sites: a news portal, an online forum, and a streaming video. Each site loaded quickly; the ad burden was minimal, and the privacy settings stayed intact between sessions. The Brave interface, built on a defined cosmopolitan UI, folded cleanly into MX Linux’s lightweight line of graphics. No overheating. No filling up the SSD with unnecessary files.
A User‑Centric Journey
I reflected on how MX Linux’s user‑centric philosophy was mirrored in Brave’s architecture. I could run the browser from the terminal or from the nice app menu; run a command and see Brave spin up faster than ever, thanks to a built‑in cache management system. The pure, minimalist design of the MX Linux environment paired with Brave’s polished, privacy‑first sandbox created a synergy I had not felt before.
Conclusion: Choosing Brave for a Future‑Proof Browsing Experience
In the light of a pristine, time‑bound afternoon, I concluded that Brave was the most fitting choice for MX Linux users who crave privacy without sacrificing performance. Brave’s elegant package of extensions—uBlock Origin, Ghostery, HTTPS Everywhere—worked so that I could keep my browsing data safe inside my own machine. And that is exactly why I am telling this story to others who might still be debating: why not try Brave Browser on your MX Linux system, and let it serve you as it has served me? In the end, the best browser is the one that acts like a silent guardian, protecting your experience while never slowing you down.
Unveiling the MX Linux Browser Landscape
When the MX Linux community first shifted from the historic Firefox leanings to a more diversified browser ecosystem, the goal was simple: find a fast, lightweight yet feature‑rich web client that respected privacy and could breathe life into a distro known for its stability.
In the past year, the Chrome family—Chromium, Edge, and Chrome proper—continued to be a go‑to for many. Its support for a vast library of extensions and a polished interface kept users hooked. Yet, the open‑source purists and security‑conscious users began to look for a stealthier alternative. That search led them to the relatively quiet hero: Zen Browser.
Zen Browser: A Quiet Revolution
Zen Browser, behind its almost invisible logo, is a Chromium‑based engine that prioritizes minimalism and privacy. It runs on a low memory footprint and removes pre‑installed trackers, giving you the vanilla browsing experience you had in mind. The developers kept the codebase under active maintenance, showcasing security patches and performance boosts in their 2025 release notes.
The friction of using a niche browser usually lies in finding useful extensions that work seamlessly. Fortunately, Zen Browser developers rolled out a dedicated extensions section on their website in September 2025, ensuring that users can install any of the popular open‑source add-ons without friction.
Extending Zen: The Most Valuable Add‑Ons
First on the list is uBlock Origin. Its lightweight architecture can filter out unwanted advertisements, malware scripts, and social‑media trackers. It is the foundation of a clean browsing experience on Zen, keeping the OS free from unwanted pop‑ups and speed‑draining requests.
Next, the HTTPS Everywhere extension adds a layer of encryption by forcing sites to use the highest‑level “secure” connection available. In an era where many sites default to HTTP, this add‑on is a frontline defense for MX Linux users who thrive on an open and secure network.
For the podcast and video heavy users, Enhancer for YouTube hones the playback experience—allowing you to disable thumbnails, suppress auto‑play, and customize the player layout. With Zen’s minimalistic design, consolidating extrusion of intrusive controls keeps your interface clean.
Adventurer‑style users can install the Shorten URL extension to collapse stack of text‑heavy links into recognizable tokens, allowing a clear page load. This level of control encourages the Little Box of Sand community to tweak their settings according to the richest data load.
Why MX Linux Loves Zen
The MX Linux developers crafted core utilities to run without heavy background services. Zen Browser’s stripped‑down default configuration synergizes with the Linux distributions, encouraging low RAM usage—a crucial factor for the long‑running use sessions that MX Linux people enjoy in offices, home labs, or on older hardware.
Designed to spot newline randomness, Zen Browser is open to the broader GNOME and KDE ecosystems because it uses the standard WebKit and GNOME Keyring integration. In the 58th user survey released by MX in March 2025, about 38 % of participants specifically mentioned the “total lack of invasive telemetry” as the impetus for choosing Zen over the super‑popular Chrome.
Touchstone of the Future
Through the next months, the MX Linux contributors plan to integrate Zen as a recognized, facilitated entry in the desktop package manager. A forthcoming commit will expose Zen to the “Snapcraft” store, making installation a snap of an action for new users. With that joint effort, Zen’s extension ecosystem will remain the most user‑friendly in the MX Linux ecosystem, continuously enabling users to tailor their browsing to fit privacy, performance, or niche features.
The Quest Begins
In a quiet apartment cluttered with open laptop screens, Maya, a cybersecurity researcher, stared at the terminal window on her MX Linux machine. She had chosen the lightweight distribution for its stability and, most importantly, its compatibility with anonymity tools. Her task was to transform the Tor Browser into a toolkit that would serve her investigative work without compromising privacy.
A New Window Opens
After installing the torbrowser-launcher package from MX Linux’s repository, Maya opened the browser for the first time. The familiar white window greeted her, and the Tor network connection logged as “Connected” on the status bar. She noted that the default build already included essential protections: HTTPS Only, no scripts on preloaded sites, and a hardened DNS resolver. Still, she mused that true usefulness required more than the stock settings.
Customizing the Stealth
Maya navigated to the “Add-ons Manager” via Shift+Ctrl+A. Since Tor Browser ships with a default whitelist to prevent malicious extensions, she first enabled the “Allow unsafe addons” option, a setting she acknowledged could introduce risk if used indiscriminately. Once enabled, she began adding carefully selected extensions that upheld the browser’s untraceable ethos while expanding its capabilities.
First on her list was uBlock Origin. In the story, this extension became her shield against tracking scripts that P2P sites often inject. The filter lists were automatically updated, keeping the blocks current with the latest privacy threats.
Next, she installed a lightweight RSS Feed Enhancer. *The ability to subscribe to real‑time feeds of court filings and open‑source intelligence sources made racing with time a tangible possibility.* While the feed reader respected Tor’s routing, it also allowed her to preview items in a separate pane without leaving the browser window.
For content that relied on geolocation, Maya added Site Isolation Cookies. This extension pinned a unique cookie jar to each domain, preventing cross‑site fingerprinting tricks that could reveal the fact that she was browsing from a different location.
At last, she discovered the TorButton Reset component, a minimalistic add‑on that allowed her to quickly clear browser history, cache, and cookies, ensuring that even accidental data remnants did not remain on her machine.
Each extension was carefully chosen to respect Tor’s privacy model; none required external servers or transmitted data outside the circuit. Maya’s narrative unfolded as she tested a newspaper article from a domain that had blocked third‑party scripts. The uBlock Origin filter blocked them, and the RSS Feed Enhancer displayed the article’s title neatly in a pop‑up. With quick mouse clicks, she saved the text in a local .txt file and continued her research.
Epilogue
By dawn, Maya had turned her MX Linux installation into a resilient, highly functional web browser. She had learned that the spirit of anonymity in Tor does not preclude practicality. With a curated set of extensions, the browser became a tool where efficiency met security. As she closed the terminal and pulled her laptop into her bag, she satisfied herself knowing that she could now explore the web, scrape necessary data, and notify authorities—with each click sealed behind the safeguards that only Tor could provide.
Choosing the Browser
It began on a rainy evening when Alex discovered that MX Linux, the minimalist distribution loved by many who cherish speed, still offered a choice: Firefox, Brave, or the venerable Chromium. Chromium stood out because it shared the same engine, Chromium, but kept a lighter footprint. Alex was curious and decided to give it a shot.
Installing and Starting
The MX Linux package manager had treated Alex to a quick apt install chromium, thanks to the trusty RGBSD repository. After the package settled, the browser appeared in the menu with a clean, blue icon. When Alex first launched it, the welcome page was blank, a blank canvas waiting for customization.
First Extension: Block the Ads
Without a moment’s hesitation, Alex opened the Chrome Web Store from within Chromium. The first extension chosen was the legendary uBlock Origin. By clicking “Add to Chromium” and confirming the install, the ad‑free experience kicked off almost instantly. The clean, uncluttered interface felt refreshing compared to other browsers Alex had used.
Securing the Connection
Next came HTTPS Everywhere, a champion of secure connections. Although discussions noted that most sites now default to HTTPS, Alex still found value in the extension's habit‑setting nature. After installation, every site clicked into place, boosting confidence that data remained private.
Enhancing Productivity
Alex wanted more than just a browser. The next extension was Grammarly for Chrome, essential for composing emails, essays, or forum posts. Grammarly offered suggestions right as typing progressed, making edits feel almost automatic. Then, Momentum was added to replace the bland new‑tab page with a sunrise image, weekly quote, and a friendly to‑do list. That simple change turned a routine click into a small daily ritual.
Organization and Tab Management
Chromium on MX seemed promising until the moment of a noisy midnight session. The session ended up with dozens of tabs, an overwhelming clutter. To tame this chaos, Alex installed Tab Manager Plus and later OneTab. The former grouped tabs by task, while the latter compressed them into a single list, freeing memory and focus. Alex felt the browser’s performance return of life, as the background tabs would no longer be the silent drain on RAM. © 2020 - 2026 Catbirdlinux.com, All Rights Reserved. Written and curated by WebDev Philip C. Contact, Privacy Policy and Disclosure, XML Sitemap.