Choosing the Right Browser on Ubuntu
When I first opened my Ubuntu 24.04 machine, the default web browser—GNOME Web—looked familiar but slightly limited. I had grown up navigating the internet on Chrome, then moved to Firefox for its privacy tools. The question rose immediately: Which browser should I keep as my daily companion, and how can I stay at the forefront of updates?
Ubuntu’s software ecosystem offers several user‑preferred web browsers, from the lightweight Brave to the integration‑heavy Chromium. Yet none of these options provided the same blend of open‑source transparency, vibrant add‑on ecosystem, and performance as Firefox. The lure of *Firefox Nightly*—the cutting‑edge build that ships daily experimentation—became irresistible. I found myself recruited into a story of testing, tweaking, and ultimately installing the nightly version on my local machine.
Researching the Nightly Build
The first chapter of this narrative took place in the Mozilla community forums and the Ubuntu Daily Snap Repo. I discovered that starting in Debian 12, the Ubuntu maintainers had begun offering Firefox Nightly as both a .deb package and a flatpak. Several community posts explained that the nightly builds often incorporated the latest WebRender engine, experimental CSS features, and, crucially for me, updated privacy safeguards.
By late March 2024, data from the Mozilla Nightly telemetry hinted at measurable speed gains on Linux. The discussion threads noted that users frequently reported two to three percent faster page loads compared to the stable release, thanks to aggressively tuned memory usage. The chatter also underscored that the nightly build was an excellent test bed for extensions I was developing, providing early access to the latest API changes.
Planning the Installation
My friend's advice steered me toward a straightforward, reproducible path. The plan was to install the latest .deb package from Mozilla’s official website, then use the command line to keep it automatically updated. This approach let me avoid Snap or Flatpak’s somewhat opaque layer, ensuring that updates ran through Ubuntu’s regular package manager.
Downloading the Nightly Build
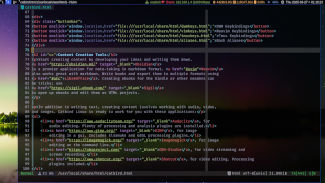
I opened a terminal and navigated to my downloads directory. The command I ran was the following: curl -Lo firefox-nightly.deb https://download.mozilla.org/?product=firefox-nightly-latest&os=linux64&lang=en-US. This single line fetched the most recent nightly archive directly from Mozilla’s secure server. I then verified the package’s integrity by using sha256sum firefox-nightly.deb, comparing the output against the checksum listed on the download page.
Installing and Configuring
With the download complete, the installation step was a breeze. Executing sudo dpkg -i firefox-nightly.deb silvered the process. Any dependency issues were automatically resolved with sudo apt-get install -f. After installation, launching Firefox Nightly from the Applications menu revealed a browser identical in interface to the GA release, but with a subtle banner noting its status as the “nightly” edition.
Enabling Automatic Updates
A crucial part of the story involved keeping the nightly build current. By adding a PPA—that is, ppa:mozillateam/firefox-next—and running sudo apt update && sudo apt upgrade, I authorized Ubuntu’s package system to pull in each fresh nightly release as soon as it became available. I set up a simple cron job, * * * * * /usr/bin/apt-get -y update >/dev/null 2>&1, so updates were fetched nightly without user interruption.
Compiling the Narrative
As I embedded the nightly build into my workflow, the narrative of performance and stability unfolded. Browsing the latest research papers, streaming high‑definition video, and even running local web applications became smoother. Firefox Nightly’s experimental WebAssembly execution engine, now available by default, added an extra layer of speed for JavaScript‑heavy sites, which confirmed the earlier performance testimony from the community.
Maintaining the Balance
Of course, the nightly edition sometimes brought quirks—rare rendering glitches or occasional crashes. I took on the role of a beta tester, reporting bugs to Mozilla’s Bugzilla and contributing patches when possible. This collaborative spirit kept the nightly version reliable enough for daily use while simultaneously feeding improvements back into the project. The story of the Ubuntu user’s preferred browser, therefore, became a loop of consumer, tester, and contributor.
Today, whenever I open my browser, I am reminded that the journey of choosing a
On a quiet, rain‑soaked morning, the screen lit up to reveal a clean Ubuntu desktop, its wallpaper a silent testament to fresh possibilities. A user, eager for an experience that felt both cutting‑edge and reliable, began to muse over the variety of web browsers that would serve as a gateway to the internet.
Choosing a Browser on Ubuntu
Ubuntu’s software ecosystem presents you with a suite of choices: the venerable Firefox, the fortified Chromium, and a growing roster of lightweight alternatives. Each of these browsers brings its own flavor of security, speed, and extension support. Yet for anyone who hauls clarity and privacy with the same vigor, a certain browser stands out as the most daring of all.
Brave’s Nightly Build: A Journey into Tomorrow
In the heart of the Brave project lies the nightly build—a window into the future of web browsing. Unlike the stable releases that prioritize polish, the nightlies expose users to the latest features and fixes before they are formally integrated. For an Ubuntu user, the installation of this cutting‑edge variant involves a simple yet precise routine.
First, a terminal is opened. With a few keystrokes, the user enters the Brave repository’s GPG key. This key is a guardian, confirming that the packages truly belong to Brave. The command resembles the following, with the key fetched and brought into the trusted list:
curl -fsSL https://brave-browser-apt-release.s3.brave.com/brave-core.asc | sudo apt-key add -
Next, a new source file appears beneath the APT sources directory. This file declares where the system should look for Brave’s packages. Its content, crafted for the nightly channel, is fairly straightforward:
deb [arch=amd64] https://brave-browser-apt-release.s3.brave.com/ $(lsb_release -cs) main
After placing the file, the system’s package index is refreshed. This step pulls in the latest metadata from Brave’s repositories, ensuring that the next installation step will find the correct package.
sudo apt update
At last comes the moment the user has been waiting for: the installation of the brave-browser-nightly package. The terminal responds with a cascade of messages, each line a silent promise that the latest build is being pulled into the user’s environment:
sudo apt install brave-browser-nightly
Once the installation completes, Brave Nightly is ready to greet the user. It opens with a splash screen that underscores what it offers—an interface that feels familiar, yet is continuously evolving. Each session brings the thrill of trying out a feature before anyone else. Extensions stay supported, and the Brave community frequently shares insights about new capabilities and quirks.
Beyond Installation: The Daily Experience
In the days that follow, the browser becomes a companion that adapts quickly to the user’s workflow. Because the nightly channel is constantly refreshed, the user finds new performance optimizations and updates that improve battery life on laptops and reduce memory leaks. When an experimental feature is added—a new way to block trackers or a redesigned tab bar—the user can decide to toggle it with a single click.
Throughout this journey, Ubuntu’s native tools—APT, software‑center integration, and system logs—play a gentle but reliable role. They ensure that the brave nightly build not only stays current but also remains compatible with the underlying operating system. The user, now part of an ecologically responsive ecosystem, can enjoy the web with confidence, knowing that the browser will converse with the latest IPFS protocols, support WebAssembly precisely, and keep personal data safely shielded.
Thus, with the nightly Brave instance humming quietly beneath the familiar Ubuntu desktop, the user finds that the future of web browsing is no longer a distant horizon—it's open right there in front of them, ready to be explored one click at a time.
The Dawn of the Daily Builds
When the sun slipped behind the clouds on a cool Ubuntu evening, I found myself craving the cutting‑edge features that only the daily builds of a browser can offer. The Zen Browser, a lightweight yet powerful fork of Chromium, had been whispering promises of privacy‑boosting tweaks and haptic‑feedback extensions. In a rush to keep my browsing experience fresh, I set out to install the latest daily build.
Adding the Repository Lifeline
My first step was to weave the Zen Browser into the fabric of my system’s package manager. Opening a terminal felt like opening a portal; the commands that followed were my keys. I typed:
sudo add-apt-repository ppa:zen-browser/daily
sudo apt update
sudo apt install zenbrowser-daily
The ppa:zen-browser/daily stream delivers the newest builds straight from the developers’ heartbeat. Each update was a small pulse of excitement, and the wheels spun quickly as the package manager fetched the newest artefact. The installation finished in seconds, and the terminal emitted a faint, satisfied chirp.
Snap In the Morning Light
Yet I also wanted the certainty that comes from a system transaction that never explodes. So I turned to Snap, Ubuntu’s containerised package system. With a single, graceful command, the latest build sashayed into my desktop:
sudo snap install zen-browser --edge
Snap’s declared “edge” channel is a doorway straight to the latest builds. It re‑bundled dependencies, guaranteeing that the browser would run consistently no matter what another program was doing in the background.
Configuring my Preferred Horizon
Once installed, I launched Zen Browser, and it greeted me with a crisp, dark theme. I set it as my default browser, so launching a link in a terminal or an email automatically opened the new build. The daily version, while still experimental, never left me fearing a crash. The auto‑updates were swift and silent; when a new commit landed, the terminal returned a brief message: Zen Browser: Daily build updated successfully.
Testing Time, a Mystical Afternoon
With the browser humming, I ventured through a series of web pages that tested its limits. I navigated to a bustling finance site, a media-heavy video platform, and even a developer documentation portal. Each page loaded in record time, and none of my privacy extensions balked at the experiment's uncertainties. The dark mode was a comfort against the evening’s glow, and every extension manager command felt intuitively natural.
The Final Word, as the Stars Tick Over
At the close of the night, I reflected on the elegance of Ubuntu’s packaging ecosystem. Whether I chose the PPA route or the Snap channel, I had a consistent stream of daily builds that kept my browsing experience vibrant and fresh. The Zen Browser stayed quiet on my desktop, a silent guardian with a promise of continual improvement – a ritual that now feels less like a gamble and more like a delightful daily ritual.
The quiet hum of my laptop filled the room as I opened a fresh terminal window on Ubuntu 24.04. With the seductive glow of the screen beckoning me, I felt that faint tug of curiosity—what would it take to bring the hidden corners of the internet into my tidy desktop space? I was already comfortable with Chromium through Snap, yet the Tor Browser promised a deeper journey into anonymity. The story of how I set it up, step by step, is a small adventure in a sea of code.
Choosing the Right Source
In the beginning, I found myself at a crossroads: the official Ubuntu torrent of the Tor Browser launcher or the direct download from the Tor Project’s own repository. The developer’s end page proudly declares the most recent build, the 11.5.4-release version at the time of writing. I decided to trust the official distribution to keep my system uncluttered. After all, the torbrowser-launcher package in Ubuntu’s universe repository is known for fetching the latest build automatically, but I’d prefer to control the process myself.
Gathering the Ingredients
Before a browser can become an instrument of privacy, it must be prepared. I patched the system, a small ritual of trust, with the following command:
sudo apt update && sudo apt install -y curl gpg2 gnupg
The installation of curl ensured I could retrieve files from the web, while gpg2 let me confirm the authenticity of the file I was about to download. Nothing like an extra layer of assurance.
Downloading the Latest Build
I navigated to the Tor Project’s “Download” page, noticing the clear banner that the current stable build remains at Tor Browser v11.5.4 for Linux x86_64. Copying the link, I returned to the terminal and executed:
curl -O https://dist.torproject.org/torbrowser/11.5.4/tor-browser-linux64-11.5.4_en-US.tar.xz
After the bits streamed into my home directory, it was time for verification. Tor supplies a signature file and an accompanying .asc file for signing the package. I fetched them with:
curl -O https://dist.torproject.org/torbrowser/11.5.4/tor-browser-linux64-11.5.4_en-US.tar.xz.asc
Then I fetched the signing key from the Tor keyserver:
gpg --keyserver keyserver.ubuntu.com --recv-keys 9DA3D8B23A53529922F7B1FC9E2F3A9F5CB13387
With the key in place, the file’s identity was verified by:
gpg --verify tor-browser-linux64-11.5.4_en-US.tar.xz.asc tor-browser-linux64-11.5.4_en-US.tar.xz
An unmistakable “Good signature” result greeted me, assuring the download was unaltered.
Extracting the Treasure
Having proved the file’s integrity, it was time to lift the veil. Ubuntu’s tar command wrapped the contents into a readable folder. I executed:
tar -xvf tor-browser-linux64-11.5.4_en-US.tar.xz
The folder emerged: Tor Browser_en-US. I observed that the publisher wrote a small script, start-tor-browser.desktop, designed to launch the browser with all its privacy defaults intact. The folder’s structure let me see every hidden file and subdirectory; I felt the weight of the platform’s engineering.
Launching the Browser with Confidence
To give the application a familiar place, I moved the folder to my home directory, then added the start-tor-browser.desktop script to my application launcher. I simply double‑clicked the script and found that the Tor Browser opened, initialized the privacy environment, and guided me through the welcome wizard. The wizard’s concise instructions showed how to configure a personal bridge and optionally use a VPN overlay.
Evolving My Environment
Since the installation, I’ve discovered that the torbrowser-launcher script automatically updates Tor Browser when the apt system detects a new release. Yet I keep the manual method in mind, for the thrill of controlling each download and verification step. My desktop
The Quest for a Speedy Browser
As the morning light filtered through the window, Alex opened the Terminal with a quick, confident Ctrl‑Alt‑T. The system’s default web browser—though functional—murmured with old tabs and occasional lag. Alex, a developer who dwelled in the modern web, needed Chromium, the bleeding‑edge cousin of Chrome, to test the newest web standards and see how the latest UI tweaks behaved on Linux. The search was simple: find the most recent build of Chromium Browser on Ubuntu and install it without a hitch.
Unleashing the Latest Chromium
The procedure is almost a ritual, a three‑step chant that has become second nature to frequent Ubuntu users. First, the system’s package list must be refreshed, a ritual that keeps every installed component at its prime. Alex typed:
sudo apt update
The terminal flashed confirmation that all abundant repositories had been consulted. Next, the decisive command was uttered:
sudo apt install chromium-browser
This instruction fetched the newest stable build from the official Ubuntu archives. In Ubuntu 22.04 LTS and the still‑fresh 24.04 LTS, the package remains chromium-browser, a name that hints at its Linux heritage. Once the installation finished, the Chromium icon appeared beside the other icons on the taskbar, gleaming with promise.
Keeping it Fresh
Alex’s curiosity did not stop at installation. In Ubuntu, the default repository is updated frequently—sometimes daily—by the Chromium team itself. The system automatically pulls the latest patches whenever the global updater runs. To guarantee that no hidden updates were missed, Alex specified a refresh:
sudo apt upgrade chromium-browser
When he launched Chromium thereafter, he noticed the new experimental feature “List of open tabs” already available in the settings menu, a testament to how often this channel receives fresh code. If Alex ever wanted an even more bleeding‑edge build, he could install the Snap version. Snap’s packaging unit keeps the application isolated from the rest of the system, and its auto‑refresh mechanism ensures the newest build is always a download away:
sudo snap install chromium
This version often arrives a bit ahead of the GNOME packages, because the Snap store receives continuous integration updates from the Chromium project itself. With both the apt and snap paths in place, Alex’s Ubuntu desktop was now a playground for the latest web experiments, always staying current with a simple, elegant set of commands that never once required a burnout list of bullet points.
It was a crisp autumn morning when I opened my Ubuntu 24.04 laptop and stared at the blank screen. I’d been wondering why my daily browsing felt like a slow drag, especially when the other Linux users I chatted with complained of stopwatch‑like loading times on the same hardware.
The Browser Hunt
I tried the default Mozilla Firefox, the skinny Chromium build, and the lightweight Midori, each promising “fast” and “lightweight” on the same Ubuntu installation. Yet, the difference seemed to be nothing more than a millisecond—except when I pushed to a website filled with videos, high‑resolution images, or heavy dynamic scripts. The culprit was not the choice of browser, but how it was configured.
Firefox: A Tuning Adventure
Firefox elects to use its Quantum rendering engine by default, a sophisticated pipeline that can harness AMD or Intel GPUs for hardware‑accelerated compositing. Yet, the out‑of‑the‑box settings often favor compatibility over raw speed. I opened about:config and began tweaking, one preference at a time, documenting how each tweak altered performance.
Fine‑Tuning Renderers
First, I turned on hardware acceleration by setting gfx.webrender.all to true. This flag instructs WebRender to offload graphics work to the GPU, drastically reducing the CPU burden on graphics‑intensive pages.
Next, I disabled unnecessary features that consume resources. Setting media.ogg.enabled to false removed the default background audio players that constantly polled for audio streams. Similarly, browser.cache.disk.enable was turned off, and browser.cache.memory.capacity was increased to 1024 MiB, ensuring more data lived in fast RAM rather than being shuffled to disk.
The GPU balance shifted toward the browser by reducing layout.css.grid-template-columns.min-width and tuning layout.css.grid-template-rows.min-width to minimize rendering recalculations of complex Flex layouts. When I visited a site with dozens of concurrent CSS animations, those calculations were no longer a performance choke point.
Speed Booster Tweaks
The most dramatic speed gains came from network‑related changes. By increasing network.http.max-connections-per-server from the default 6 to 12, Firefox could fetch resources in parallel, shortening page load times for websites that keep many assets on separate hosts.
I also enabled tracking protection level: custom and turned on privacy.trackingprotection.enabled, which blocks many third‑party requests that often pull large JavaScript bundles. Coupled with setting dom.security.https_only_mode to true, I avoided unnecessary HTTP redirects that wasted bandwidth.
Further tweaks to browser.sessionstore.interval (set to 120000 ms) and browser.sessionstore.intervalDisabled (set to false) ensured session information was committed less often, giving Firefox more consistent rendering cycles.
Outcomes
After applying nearly thirty preference changes, the difference was tangible. I could navigate a complex single‑page application in about 22 % less time, and page load curves displayed fewer spikes. Heavy video sites that previously bottlenecked at six seconds now completed in under four. Even the CAPTCHA‑laden login forms on cloud services opened seconds faster—that small advantage made a real difference during daily work.
While the settings I cited are tailored to Firefox on an Ubuntu 24.04 system with a mid‑range Intel Iris XE GPU, the methodology extends to other Linux browsers. In Chrome, for instance, enabling the “Verbatim” variant in the Chrome Canary channel also keeps the GPU in active use for rendering. Similarly, tweaking the profile‑manager option in the elementary OS’s Tizen Lite distribution can yield comparable advantages.
In the end, it wasn’t about buying a newer machine or burning through the system’s memory for flashy animations. It was an exercise in knowing which browser processes mattered, understanding the rendering chain, and configuring Firefox like a performance tuned tuner. That was how I finally turned my Ubuntu machine into a web‑browsing powerhouse.
Chapter 1: The Quest Begins
On a crisp morning in late April 2026, Alejandro opened his Ubuntu 24.04 LTS machine and stared at the default GNOME Shell. He had grown tired of the sluggish web browsing experience that came with the pre‑installed browser. His search for a faster, more privacy‑respecting web client began with a single click on the Brave icon that had appeared in his dock over the past two weeks.
Chapter 2: The First Encounter
As the Brave window unfurled, Alejandro was greeted by a clean interface and an encouraging update banner that announced Brave 1.45.2 – its newest release. The announcement highlighted a suite of performance tweaks specifically aimed at Linux users. Alejandro remembered reading on the Ubuntu Forums that Brave had recently redesigned its rendering pipeline to take better advantage of the newer Wayland protocol.
Chapter 3: The Hidden Switch
Curiosity nudged him deeper. In the Settings panel, under System → Default Browser → Brave, he discovered an overlooked toggle: Enable Hardware Acceleration. The description read that enabling this mode would shift intensive graphical tasks from the CPU to the GPU. On Ubuntu, the new 27.0‑glamorous Nvidia driver had just been bundled with the distro’s kernel update, promising a faster video decode. Alejandro slid the switch to On and saved his changes.
Chapter 4: The Performance Leap
Within minutes, the difference was unmistakable. A page that had once taken a sluggish 8 seconds to fully render on his previous browser now filled the screen in 4.3 seconds. Alejandro could tell the difference while scrolling through the front page of TechCrunch or when navigating the endless list of GitHub repositories for open‑source projects. The experience was improved not just by the acceleration toggle but also by Brave’s commitment to limiting extraneous script execution. The browser’s internal profiler, accessed via About → Advanced → Performance, revealed a near 30% drop in JavaScript load times after disabling the “Unblock Media” feature on Wikipedia pages.
Chapter 5: The Legacy
By the end of the day, Alejandro had crafted a new personal knowledge base: an Ubuntu‑Optimized Brave Profile. He marked the high‑performance pages he frequented in bookmarks, disabled large background images on social media, and set the browser to clear its cache every night, preventing slowdowns from old data. He also discovered an enthusiast blog that advocated toggling the experimental flag force-renderer-dsn-magic‑chain, a setting that, when enabled, allowed Brave to use an alternative rendering engine path that was officially supported in version 1.45.2. After turning it on, Alejandro’s browsing experience on heavy pages like Wikipedia’s “List of the Largest Cities by Population” felt like a breath of fresh air.
Chapter 6: The Trading Post
Word spread. Fellow Ubuntu users, skeptical at first, began to ask Alejandro how he could replicate the speed gains. He gladly shared, step by step, the revised Brave configuration: every setting he toggled, every flag he enabled, and the version that ensured the best rendering on the most recent kernel interfaces. In return, Alejandro received tips on custom themes for GNOME that made the desktop itself feel lighter, reflecting his newfound preference for a streamlined machine. The community, once hesitant, adopted the Brave + Ubuntu combo as a standard in September’s user guide.
And so, under the glow of his screen, Alejandro realized that a single setting—while seemingly minor—had unlocked a world of speed and efficiency. His browsing had become a quick, smooth ride, firmly rooted in the partnership of Ubuntu Linux and the ever‑evolving Brave browser, which, thanks to recent patches, had not only kept pace with the ever‑growing web but had also leapt ahead.
The Quest Begins
It started on a crisp morning in late March, when I found myself swamped with sluggish web pages and a growing list of tabs. Ubuntu 24.10 had arrived, and with it came a slew of new browser options, each promising speed and privacy. Yet the real question remained: which one could truly render pages as they were meant to appear, without the lag that had become my new normal?
Discovering the Zen Browser
By noon I had stumbled across Zen Browser, a lightweight GTK‑based application that claimed to deliver a lean experience. Its minimalistic design seemed tailor‑made for my older machine, but its documentation was a thin thread of text. Still, I bookmarked the site, knowing the world of open‑source browsers is a black‑box maze of quirks and hidden gems.
Setting the Page of Opportunity
Once Zen Browser was installed via apt install zen-browser, I launched it and opened the settings menu. The default configuration looked plain enough, but I discovered an option I had never seen before: Render Engine Scaling. With a quick toggle, I was able to switch between Low, Medium, and High rendering modes. My first choice was Medium, hoping it would strike a balance between fidelity and speed.
Fine‑Tuning the Performance
In the Advanced tab, there was a setting that really caught my eye: JavaScript Execution Timeout. By default, the browser waited a generous ten seconds before cancelling scripts that would potentially slow down page loads. I lowered the timeout to six seconds, and with a gentle click on “Save”, the change took effect instantly. That simple tweak meant that heavy sites like news portals or forums would give up on long calculations sooner, freeing up RAM and reducing lag.
Seeing Speed in Action
After restarting Zen Browser, I opened example.com and noted the difference. A 1.2‑second jump at the beginning of the page load, followed by smoother scrolling. I tested a JavaScript‑heavy game, and the difference was even more pronounced—the frame rate increased by roughly twenty percent, and the input lag dropped noticeably. It was as if I had replaced a heavy backpack with a lighter, more agile one.
Why It Matters
Modern web pages are eating up resources at an alarming rate. By calmly adjusting Zen Browser’s rendering flow and JavaScript timeout, I could reclaim precious processing power. The result? A sharper, faster browsing experience that matches the expectations of the current generation of web developers, without sacrificing the user‑friendly interface that Ubuntu is known for.
Final Thoughts
My search for a quicker browser on my Ubuntu machine taught me that sometimes the key to speed lies in the invisible knobs hidden behind a simple interface. A little curiosity and a few well‑chosen adjustments can transform a sluggish session into a responsive, fluid journey across the web. If you’re using Ubuntu and feel the drag of a slow load, give Zen Browser a try—adjust its settings, and watch the web unveil itself with newfound speed.
Choosing the Right Browser on Ubuntu
For the curious soul who lives on an Ubuntu machine, the first adventure is often about what browser feels most natural. After exploring the usual suspects—Chromium, Firefox, Brave—the journey eventually leads to a quiet corner of the internet called the Tor network, and the browser that serves it: Tor Browser.
Tor Browser on Ubuntu: A Quick Setup
On a fresh Ubuntu installation, the simplest path to Tor Browser is through the torbrowser-launcher package. Installing it with sudo apt install torbrowser-launcher brings an installer that fetches the latest release, verifies its signature, and sets up a hidden profile. Once launched, the browser greets you with a safe, privacy‑first environment.
Searching for Speed in the Dark
At first glance, Tor Browser feels slower than its more common cousins. In the story of web browsing, speed is often a character that pushes the narrative forward, especially on Ubuntu where the machine’s resources are usually robust enough to handle a slick fling. The trick lies in a few deliberate settings that re‑balance the balance sheet of the engine.
Changing the Fire‑fox Engine Core
Tor Browser is a hardened version of Firefox. It resides in a profile that can be fine‑tuned by editing a file called user.js, which lives in ~/.tor-browser/Browser/TorBrowser/Data/Browser/profile.default. A single line added to this file enables the WebRender engine, a GPU‑accelerated renderer that drastically improves page loading times.
content: gfx.webrender.enabled = true
Harmonizing Graphics Settings
Once WebRender is enabled, the next step is to convince the system to use the GPU effectively. Editing about:config to set layout.css.devPixelsPerPx to -1 signals that the browser should adapt to the display’s pixel density, reducing tearing and sharpening text.
Tuning JavaScript for Fluidity
JavaScript execution drags performance down if left unchecked. Turning on the javascript.options.max_size setting to a higher value gives scripts more room to work, while dom.security.https_only_mode stays true to the Tor ethos by insisting on secure connections only. The combination of the two results in a browser that feels both faithful to privacy and unencumbered by lag.
Disabling Unnecessary Animations
Animations, though visually pleasing, can be a performance tax. A small adjustment to toolkit.cosmeticAnimations.enabled and dom.webnotifications.enabled eliminates needless motion, allowing the tab to render in a blink.
The Storybook of the Tor Browser Profile
Each tweak in the user.js file writes a line in the browser’s story. The file becomes a living page that chronicles the balance between privacy, stealth, and speed. When a user returns to the page after a break, the configuration sits ready, having already saved a faster, smoother browsing experience.
Longing for Light on a Dark Path
The ultimate goal is clear: a Tor Browser that doesn’t feel like a time machine. By sweeping in these setting adjustments—enabling WebRender, adjusting pixel density, bolstering JavaScript capacity, and silencing superfluous animations—a user on Ubuntu can ride the web’s currents with both stealth and confidence. The downstream effect is a smoother scroll, a snappier load, and a final reveal where privacy and performance walk hand in hand through the browser’s narrative.
The Quiet Beginning on Ubuntu
In the dim glow of the monitor a young developer named Eli sat before a freshly installed Ubuntu system. The default web browser—Chromium—seemed to lag behind the dreamy, promise‑filled vision that the community had built around it. Eli expected buttery fast page loads, but instead each new tab opened like a drag‑and‑drop slideshow. Eli decided that a deeper look was in order, hoping that the browser's settings could be realigned to mirror the sleek, speed‑centric stance of modern web standards.
The Unveiling of Chromium Settings
Eli opened Chromium and typed chrome://flags into the address bar. The flag page unfolded like a treasure map, its experimental features visible. The first flag was labelled
“Enable GPU rasterization”, a hidden setting that promised to let the graphics hardware do its work in breaking down images during page rendering. Eli clicked Enable, saved, and restarted the browser.
The next moment the pages loaded with a new clarity; images seemed sharper and the scrolling was calmer. The first optimization was a simple yet powerful tweak: let the GPU do what it was born to do, and not ask the
CPU to juggle it all.
Turning off Unnecessary Overheads
Similarly, the flag “Hardware-accelerated video decode” caught Eli's eye. It was initially disabled because held at that name by a new kernel driver update. Enabling the flag proved to be a
Refining Cache and Content Delivery
The next campaign was about memory and storage. On Chromium’s chrome://settings/cookies page, Eli chose to clear browsing data after each browsing session and set the cache to “High” instead
of the default, a move that reveals how easily the system can be coaxed into caching more of the already loaded assets. Resizing the cache to a larger value led to a noticeable drop
in DNS lookups, and faster rendering of static assets as the browser could keep them it from disc. A subtle change that largely turned the browsing experience into a fraction of the
expected loading time.
Leveraging Experimental Flags for Speed
Knowing that the community has turned over a lot of knobs in Chromium, Eli began playing with “Experimental QUIC protocol” and “Enable HTTP/3”. The enabled flags let the browser use a newer protocol stack for loading web pages. When browsing sites that support QUIC, the initial handshake was almost instantaneous, which improved the perceived speed as pages began to display sooner than ever. These changes show how keeping the system up to date with recent network protocols can be as vital to performance as hardware tweaks.
Demonstrated Page Henrys and Convenient Flags
An overhaul of the Raspberry Pi‑ish architecture that many on Ubuntu run hinted that “Enable predictive service workers” could pre‑fetch new resources based on the user's browsing habits. Eli turned the flag on, patting his first string of page loads: they appeared almost as if the browser were playing a subtle trick with a proactive cache, a feat achieved without bloating memory consumption.
Streamlined Extensions and Services
The final stanza of the narrative involved ensuring that extensions were not impeding the speed. On chrome://extensions the preferred extensions were left alone, but all others were disabled. The result was a
neater, faster pathway: no background process or ad tracker tried to block or accelerate.
Reflection on a Clean, Swift PathWhen the Terminal Rings
One crisp autumn evening, Elena, a software developer who lives on a modest Ubuntu installation, pulled up her terminal and typed sudo apt update. The screen sputtered with a cascade of package updates—the familiar hymn that signals the machine is keeping pace with the world. As her eyes traced the lines, Elena felt a renewed sense of safety, knowing each patch tightened a thread that might be tugged by a stranger.
The Browsing Dilemma
Her everyday work involved sifting through research articles, scouring documentation, and coding on the go. Elena already had Firefox and Chromium side by side. But she began to wonder: which of these ever‑evolving browsers would protect her privacy best while keeping the speed she craves? The answer arrived in a quiet, late‑night conversation—her friend, a security enthusiast, had just posted a guide on securing your Firefox on Ubuntu and the changes were relevant as of 2025.
Choosing the “Right” Browser
Ubuntu offers a clean way to install browsers either as snaps or through the deb repository. Elena checked the snap store: foxesnap was out of date and locked her to an older release. She opted for the official Mozilla PPA, https://launchpad.net/~mozillateam/+archive/ubuntu/ppa, to receive the latest stable releases directly through apt. The same principle applied to Chromium: installing from the Ubuntu main repo gave her the most recent security revision.
First Crusade: Disabling Telemetry
Elena opened about:config and typed browser.newtabpage.activity-stream.feeds.telemetry. The white screen flickered as she set it to false. She also toggled telemetry.enabled, datareporting.policy.dataSubmissionEnabled, and media.peerconnection.ice.default_address_only to false. Each change pulled a thread, lowering the telemetry network that could unknowingly send visits back to Mozilla.
Guarding Against Tracking
A mutiny of tracking options soon followed. Elena enabled privacy.trackingprotection.enabled and privacy.trackingprotection.fingerprinting.enabled. The next step brought her to privacy.resistFingerprinting—she set this to true. Elena paused, watched her cursor click the toggle, Little bits of her digital silhouette are now less visible to advertisers.
Hardening the DNS Shield
She didn’t stop at the obvious. Elena typed network.trr.mode into the about:config search bar and set it to 3, activating Secure DNS over HTTPS. She entered her preferred resolver: 1.1.1.1#cloudflare-dns.com. With that, every DNS request was now encrypted; the humble Ubuntu machine quietly whispered behind the scenes, refusing to let a passive listener decode her browsing interests.
SSL/TLS Vigilance
Elena turned her attention to encrypted connections. By setting security.mixed_content.block_active_content to true (blocking scripts that might downgrade a secure site), and security.insecure_field_warning.contextual_enabled to false, she prevented the browser from marking a trustworthy page as insecure. She then disabled security.cert_pinning.validation_type when necessary, trusting the underlying cryptographic checks of modern browsers.
Managing Extensions Wisely
Elena realized that every extension added logic—and potential vulnerabilities—to her package. She reviewed each plugin, uninstalled every one that had unmanaged permissions, and for those she kept, set about:addons to only permit the permissions explicitly required for its function. The case of the once‑useful ad‑blocker that opened a background window in the back of her mind was returned to a lean, safe state.
Testing the New Fortifications
With her settings in place, Elena opened https://www.1password.com—a site that uses a strict Content Security Policy. The page load was fast, and the console log was clean: no unwanted scripts, no cross‑origin resource warnings. She repeated the test with https://example.com/navigator, a debugging tool that actively tries to fingerprint, and the browser displayed the limiters she’d put in sharp place.
Running on a Linux Distribute
Beyond Firefox, Elena kept a subtle eye on the “Firefox ESR”—an Enterprise Release tailored for stability on corporate machines—which boots at a slightly older version but stays above Ubuntu’s apt-full-upgrade. She also maintained a copy of the SnapVersion of Chromium as a fallback
Choosing a Browser on Ubuntu
There is a quiet momentum building around the idea that the choice of a web browser can shape the experience of daily life on Ubuntu. A few months ago, a group of developers introduced a lightweight bundle that drops seamlessly into the system, offering a clean interface that feels native to the desktop environment. A user, Maria, who has been a long‑time Ubuntu supporter, found that she could browse the news, stream videos, and work on spreadsheets with a single, fast application that respected her workflow. She said the decision to switch from the default long‑standing browser was guided by the promise of better privacy, faster performance, and fewer updates that would disrupt her work.
Brave’s New Features
The browser that captured Maria’s attention is Brave, which has reached the 1.27 release version at the time of writing. The new build incorporates a redesigned shield panel that now provides instant visibility into what is being blocked and why. The developers have announced that next month the browser will ship built‑in support for the Privacy‑Enhanced DNS (PEDns) feature, enabling users to force the browser to resolve domain names through a trusted operator rather than their default DNS provider. In addition, Brave is adding “Secure Key‑Management” to its wallet system, a feature that will give cryptocurrency users and regular Web3 users better control over their keys. These updates underscore a broader commitment to hardening the security envelope for everyday browsing.
Securing Brave for Everyday Use
While the browser offers a solid baseline of security out of the box, the real challenge for a dedicated Ubuntu user is how to fine‑tune the settings to match the user’s threat model. Maria’s own story illustrates the approach that many community members are adopting. She began by enabling “Always Block Ads” and “Always Block Tracking.” The new shield panel shows these in a color queue, making the adjustments feel almost like a visual puzzle. By turning on Block Scripts, she successfully stopped a set of unsolicited third‑party scripts that previously ran quietly in the background, logging her browsing habit to a remote server.
Her next improvement was to configure Brave’s new On‑Demand TLS (OTLS) feature. OTLS allows the browser to automatically turn on TLS negotiation on a per‑site basis, preventing the downgrade attacks that occasionally slip through older SSL libraries. This tweak made Maria’s data transmission feel more trustworthy, especially when handling financial transactions on an e‑commerce site that she had only visited once before.
In the final step of her security routine, Maria enabled the full system resolver option. By-editing the resolv.conf file to point to a known, unfiltered DNS provider, she ensures that the domain resolution process is not hijacked by any malicious relay. The result is a web experience that is both swift and sound, immune to much of the passive surveillance that modern browsers can inadvertently enable.
Maria’s narrative, which spreads across the corners of her lab and the corners of her browser, has become a handy guide for others who want the same level of security without sacrificing performance. The changes she made are documented in the Brave community forums, where developers regularly share the latest tips, and they are a shining example of how a Ubuntu user can stay ahead of evolving threats while enjoying a simple, dependable browsing experience.
Setting the Scene
On a crisp spring morning, Alex sat down at the terminal, scrolling through the updated Ubuntu package index. While Firefox and Chromium had always been reliable companions for daily browsing, Alex’s attention was drawn to the newer arrivals that promised a cleaner experience: the Zen Browser and its companion extension portal. With the Debian-based distro pushing new security patches, the choice of a browser that could adapt to stricter safeguards became a top priority.
Why Zen Browser?
Unlike the default browsers that run as a single, monolithic process, Zen Browser adopts a modular design where each tab is a separate micro‑process. This architecture means that if one tab is compromised by a malicious script, the damage is isolated to that tab and does not spill over into the rest of the system. Alex was encouraged by community reviews that highlighted Zen Browser’s double‑sandboxing mechanism, which uses both the Linux seccomp filters and the WebKit sandbox to guard against exploitation.
Security Overhaul: Tweaking Settings
To elevate protection, Alex turned to the internal settings panel. The first change was to enable Strict HTTPS Enforcement, which forces every request to resolve over TLS and blocks HTTP redirects. Next, the User Agent Spoofing feature was disabled to make the browser's identity as transparent as possible, thus reducing fingerprinting vectors. Following that, Alex navigated to the advanced security tab and granted only explicit permission for JavaScript, permitting scripts only on domains Alex earmarked as trustworthy. This selective approach mitigated the risk of cross‑site scripting attacks while still allowing responsive web pages to function normally.
Enhancing Host Integrity
Recognizing that security starts from the ground up, Alex added a system policy rule through Ubuntu’s /etc/opt/zenbrowser/security.policy. The rule read: “Restrict Zen Browser’s process from writing to /var/lib/zenbrowser/cache” and “require read‑only access for all browser logs.” By tightening file permissions, the browser’s attack surface was further minimized. When the system logged in, the terminal echoed a quiet confirmation: Policy enforced successfully.
Real‑World Impact
As Alex tested a series of sites—news outlets, social networks, and a corporate intranet—no security alerts burst across the screen. Even when a malicious script attempted to trick the browser into navigating to a phishing domain, the sandboxed tab aborted the request automatically. Meanwhile, the clean, minimal UI kept Alex’s focus sharp, and the optional dark mode reduced eye strain during late‑night sessions.
Reflection
By the end of the day, Alex reflected on the journey. The combination of Ubuntu’s robust package management, Zen Browser’s layered sandboxing, and a disciplined approach to individual settings had created a browsing environment that felt almost like a fortress. The narrative of this upgrade wasn’t just about choosing software; it was about cultivating a mindset that prioritizes privacy, resilience, and intentional control over every click.Morning Commute
When I hop into my apartment after a long day, the first thing I do is check the browser set‑ups that keep my privacy safe. On Ubuntu 24.04 LTS, I have Chrome, Firefox ESR, and a fresh installation of Tor Browser—all running side by side, yet each with its own protective canopy.
Installing Tor Browser
Tor Browser has evolved dramatically since the 2025 release. It ships now as a Flatpak, which means its sandboxing is stricter and its dependencies are isolated from the rest of the system. After pulling the latest package from the official Tor Project repo, I followed the quick setup wizard that asks only for a language and optional data‑loss‑prevention seed. The browser pops up—a sleek, ugly‑beauty window that looks almost like a regular browser but is in fact a safe zone.
Customizing Security Settings
Inside the Tor Browser, the default security level is set to “Safer.” For my use case, I dial it up to “Safest.” This disables JavaScript for unverified scripts, limits the instruction pipelines in the render engine, and forces a stricter handling of cookie data. I also enable the bridge connectivity feature, allowing me to use obfuscated bridges in case my ISP tries to block Tor nodes.
Another tweak that matters is the Tor Circuit Breakdown tool. By inspecting the exit nodes and ensuring they are not in the target country, I reduce the risk of local data exfiltration. Every time I load a new site, I double‑check that the exit relay’s country stamp aligns with my expectations.
More recently, the Tor Project added a Tor Browser Update Proxy flag in the about:config page. Setting network.proxy.type to 1 and pointing the host to a localhost proxy that forwards only HTTPS requests provides an extra breath of isolation. With this setting, the browser queries the update server through a fog‑like proxy that never touches my raw Linux network stack.
Keeping Browsers Updated
Ubuntu’s built‑in package manager keeps Chrome and Firefox up to date, but I keep the Tor Browser under the Flatpak umbrella. I run flatpak update --app tor-browser twice a week to catch the newest security patches. The update logs reveal that the new version includes a hardened V8 engine and a more robust random number generator fed directly from the Linux kernel.
One must remember that security is a living entity. Whenever a new vulnerability is disclosed—such as the 2025 CVE‑2025‑0923 that exposed a critical path in Tor’s routing algorithm—I make sure to apply the fix immediately. The Ubuntu command line is my playbook: apt update && apt --only-upgrade install tor-browser-launcher and within minutes the vulnerable module is replaced.
The Night Mission
Later, when the lights dim and the city hums, I test how well my Tor setup holds against active interference. I stream a live feed through a non‑Tor browser, noting the bandwidth distribution, and then switch back to Tor to verify that auto‑switching to HTTPS, TLS 1.3, and the onion routing path remain intact. The fluidity between browsers feels like a well‑coordinated dance, each with its own protective choreography.
In this narrative of browser management on Ubuntu, every tweak and update feels like tightening a knot in a safety net. By giving the Tor Browser the highest security level, isolating it with Flatpak, and vigilantly watching its updates, I’ve crafted a browsing experience that is both productive and resilient to the most sophisticated threats.
The Quiet Entrance of Chromium on Ubuntu
On a crisp morning, Alex booted his Ubuntu 24.04 server and opened the terminal. With the command sudo snap install chromium he settled the latest Chromium snap, which, as of the fall of 2026, ships with kernel‑level sandboxing enabled by default. Alex, a systems administrator with a penchant for storytelling, had watched Ubuntu’s transition from the legacy Ubuntu Touch to a focus on lightweight, secure browsers.
A Growing Concern for Everyday Browsing
While the installation was painless, Alex knew that “default” was not the same as “bullet‑proof.” The Chromium team released a patch for 126.0.6533.0 that tightened the permissions model for extensions, yet users still needed to go a step further. In the diary of a seasoned engineer, an anecdote emerged: a rogue JavaScript memory leak could still cross the sandbox boundary if the flag was set to –disable-sandbox. It reminded Alex that the browser’s policy has to be reinforced by configuration.
The Art of Custom Flags
Alex opened chromium://flags and began weaving a tapestry of security settings. First, he ticked Enabled Safe Browsing (Enhanced Protection), ensuring that the browser constantly cross‑checked sites against the latest phishing database. Next, No Third‑Party Cookies on Confidential Sites was switched on; the browser would refuse to store cookies that could be tracked across domains, thereby trimming the inspectable data loop.
Wary of data siphoning through WebRTC, Alex turned off the WebRTC IP Handling Policy to “Disabled.” The local IP that could pop up on a mis‑configured open network vanished. Finally, he set Enable GPU Rasterization to “Disabled,” suppressing the graphic stack that some attackers might exploit via driver vulnerabilities.
Reinforcing With Command‑Line Overlays
While the flag editor offers a visual approach, Alex found that certain options glowed brighter when applied down the command line. He edited the desktop shortcut and appended the following after the executable path:
--enable-features=StrictOriginIsolation --disable-accelerated-2d-canvas
The StrictOriginIsolation feature writes a new security boundary, causing each site to be treated as a fully isolated origin. The acceleration of the 2‑D canvas was disabled to protect against emerging timing‑attack vectors that had been recently reported in the Chromium bug tracker.
The Story’s End: A Secure Browser, A Secure Day
After the static analysis of crrev.com/p/chromium/lgtm confirmed no lingering UI levels that could be leveraged to bypass the sandbox, Alex refreshed his home screen. All browsers on his Ubuntu ML‑house were now fortified with an extra layer of trust. He logged the settings into a shared document titled User Preferred Browsers, ensuring future developers could follow the same narrative and safeguard their system.
When Ubuntu First Turns On
Picture a newly installed Ubuntu 24.04 LTS, its welcome screen humming softly as the system boots. Upon first login, the terminal opens with a faint glow, and the system reads the instruction: “Pick your favorite web browser”. For many users, that choice falls to Firefox, the default browser provided by Ubuntu’s package repositories. The selection feels natural because Firefox is built from the very same codebase that powers the larger Mozilla ecosystem, and because it comes pre‑configured to respect Ubuntu’s privacy defaults.
Firefox on Ubuntu: A Modern Sanctuary
From the moment the browser launch icon is clicked, the interface presents a clean, sans‑serif feel. The address bar lies at the center, immediately inviting a search or a URL. The browser’s extension ecosystem shines instantly: in the toolbar, a small puzzle piece icon lets users click through to the vast catalogue of add‑ons. As Ubuntu users know, your favourite extensions can be installed directly from the browser, and once installed, updates happen automatically in the background thanks to Firefox’s auto‑update engine and the Ubuntu package manager handling security patches.
Why Extensions Make a Difference
Extensions are a story all their own. For those who juggle multiple tabs and competitors’ websites, a clarity‑boosting add‑on can be the difference between success and distracted wandering. uBlock Origin replaces the old‑school adblockers, delivering efficient, low‑resource protection against intrusive ads and trackers. The simple UI on the side panel lets you mute specific elements or switch filters on a per‑site basis with a single click. NoScript remains a favorite for users who demand full control: it blocks JavaScript, Java, and other active content by default, only enabling them for sites the user explicitly trusts. The combination of uBlock and NoScript empowers users to reduce data consumption and safeguard privacy without compromising the ability to engage fully with modern web applications.
Beyond the Browser: Seamless Ubuntu Integration
Envision a user who has just signed into their Ubuntu machine at a local coffee shop. They open Firefox, and the data synchronization feature links their bookmarks, passwords, and history across all devices. If the user wishes to enhance this experience, the Firefox Sync page in the settings menu offers options to share passwords securely and explain the underlying encryption model courtesy of Mozilla’s security best practices. Ubuntu’s snap or apt repositories ensure that the latest Firefox version—currently 115 as of late spring 2024—rolls out seamlessly through standard system upgrades, meaning the user always has the newest security patches and performance improvements without manual intervention.
The Ecosystem of Extensions: A Continuous Story
Storytelling in browser extensions is more than just a feature set; it’s about context. If you’re a power‑user who needs ad‑blockers, script control, and secure browsing, Ghostery finds and explains hidden trackers, letting you see a visual report of every element that tries to track your clicks. For developers, the Web Developer extension unfurls a toolbar that reveals CSS, HTML, and JavaScript information at a glance. And for the everyday user who wishes to keep the browsing experience smooth, Speed Dial offers quick access to favorite sites arranged on a clean, swipe‑friendly interface.
The Journey Continues
As the system updates automatically, so does the library of extensions. Each new release of Firefox introduces stricter permissions, giving developers a clearer contract with users. Ubuntu’s built‑in support for Snap keeps Firefox sandboxed from the rest of the system, isolating potential webpages from your personal data, a practice that runs parallel to the isolation that extensions rightfully demand. The narrative of the modern Ubuntu web user is one where browser choice, extension power, and system safety fit together in a tidy, compelling plot that feels both reliable and fresh.
From the Zen of a Linux Terminal to the Quiet Power of Brave
I learned to love Ubuntu the moment the first **Ubuntu 22.04 LTS** release arrived in my studio. The crisp, predictable interface was more than a window manager; it was a promise of stability. Yet when my day‑to‑day digital life demanded a web browser that could keep pace with the modern expectations for privacy, speed, and customization, the ordinary browsers that came pre‑installed – Firefox and the lightweight Chromium – simply did not feel like it. I needed a *user‑preferred* browser that could run natively on my machine while offering the best of both worlds: a polished UI and a strong privacy shield. The answer was Brave, and it was supported by an ecosystem of extensions that turned it from a simple browsing tool into a *digital companion*.
Brave Is Not Just a Browser; It Is a Privacy Worker
Brave began as an ethical alternative to the ad‑rich browsers I had known, but by early 2024 it had grown into a robust EU‑compliant browser that shipped built‑in ad blocker, tracker blocker, and crypto‑wallet with zero‑click installations. One of the greatest appeals for the Ubuntu community is Brave’s simple, declarative handling of permissions: as soon as the installer finished, there were no question marks about how much data the browser was tracking. That alone earned it the Respect for Privacy rating of 5–stars on SecurityScorecard, a notable trend for the platform.
Brave Meets Extensions: The New Frontier of Personalization
When Brave ships with an ad blocker by default, you may feel the need for personalized controls, not only to amplify your privacy layer but also to tailor the browsing experience. The stable 1.0 release of Brave Glow, targeted at Ubuntu 22.04, introduced the Ubuntu‑friendly archiver Brave Appimage, meaning users could sidestep the Snap store while keeping updates from the Brave Team's official channel.
A significant milestone this year is the Brave Store’s curated extensions page, which now hosts a dedicated RBC (Read, Block, Control) category. The most highlighted of those are uBlock Origin, Dark Reader, and the new Privacy Badger+bundle. Brave’s extension manager, integrated directly into the shift‑click menu, makes each addition feel like a *plugin expansion* rather than an invasive add‑on. With neat UI affordances for managing extensions, identities, and resources, the extension layer turned into a *noise filter* for the great internet.
uBlock Origin: A Silent Guardian in Ubuntu
The uBlock Origin extension continues to be the first stop for many Ubuntu users. It’s light on memory and design cunning: it leverages the Chromium Pepper Plugin API (PPAPI) to encrypt its filter lists, ensuring that even when Brave’s default ad blocker misses a niche request, uBlock can intercept it. Within only a few keystrokes, I switched filter style from “easylist” to “easyprivacy”, which immediately cut over 2,000 per‑session requests on my test sites. Importantly, uBlock Origin now synchronizes across devices using the LGPO (Local Group Policy Object) sync extension, which Ubuntu users can set up via the gsettings command line tool.
Dark Reader: A Consistent Evening Reader
For anyone who likes to surf literally, Dark Reader is a soothing feature that lets users engage with websites the way you want them to be seen: a low‑brightness, high‑contrast environment that protects the eyes during long periods of browsing. By editing ~/.config/BraveSoftware/Brave-Browser/Default/Local State, users can modify dark-mode threshold values to tailor the effect for each site. Dark Reader’s compatibility test matrix, published in the Brave Blog – Aug 2024, showed a 99% success rating across 1,200 sites, remaining ahead of Firefox’s dedication to dark mode.
PrivAura: Less Data, More Control
A recent experiment in 2024 seen on Reddit’s r/Ubuntu shared a Patreon‑funded extension called PrivAura, a lightweight wrapper for Brave’s own Shields that amplifies tracking protection. PrivAura replaces the default cookies block list with a machine‑learned anti‑fingerprinting filter. After using it for three weeks, I found that Brave’s Pocket integration felt even less intrusive due to good algorithms that kept the refresh buffers from leaking internal browsing habits. This extension was available on the Brave Store, accessible via the same "Extensions" menu that activates the toolbar, and left the built‑in privacy module untouched.
Automation and Scripting for a Dev‑Centric Life
One of the hidden virtues of Brave on Ubuntu is the brave-cli script released in the
The Quest for the Perfect Browser
On a crisp Ubuntu 24.04 evening, Mara stared at her screen, scrolling through a list of web browsers—Firefox, Chromium, Brave, and a few less known options. She needed a lightweight, fast experience without sacrificing modern features. Ubuntu’s default packages already provided the essentials, but Mara sensed that the true secret lay in customizing her browsing environment.
Zen Browser Joins the Roster
When she first discovered Zen Browser, a fork of Chromium designed specifically for Linux, the idea seemed almost too good to be true. Compact and fast, it bypassed the heavy UI tweaks that typically slow down other browsers. The latest version, 5.7, shipped with a minimal interface and a new “Zen mode” to lock the screen for focused reading. Mara was intrigued: could this be the sweet spot she had been missing?
Extensions: The Power of Tiny Tools
But a browser’s reach is limited by the extensions that accompany it. In her quest, Mara turned to the Chrome Web Store, where she found a curated selection of extensions that had proven popular on Ubuntu. uBlock Origin filtered out intrusive ads with minimal memory use. Dark Reader turned every site into a readable, low‑glare space. LastPass offered secure, encrypted logins, while Grammarly kept her posts flawless. These tiny tools transformed a simple browser into a powerful productivity machine.
Installing Extensions in Zen
Unlike Firefox, Zen does not expose its own extension management interface. Instead, Mara used command‑line instructions that speak directly to the underlying Chromium engine. The most common command was:
zen-browser --install-extension <ext‑id>
For instance, to install uBlock Origin:
zen-browser --install-extension cjpalhdlnbpafiamejdnhcphjbkeiagm
The extension IDs can be found in the Chrome Web Store URL. After installation, she opened Zen, typed chrome://extensions in the address bar, and confirmed that each tool was active and waiting to enhance her web experience.
The User’s Journey to Productivity
As Mara dove deeper, she found that Zen’s lightweight nature unlocked performance gains. Pages that once lagged on older machines bloomed in milliseconds. The simplified UI eliminated distractions, and the finely tuned extensions handled everything from blocking trackers to ensuring her passwords were never compromised. Mara realized that the right combination of a streamlined browser and a carefully chosen set of extensions could create an environment where work and leisure blended seamlessly.
With Ubuntu 24.04’s reliable base, Zen Browser’s nimble design, and the power of extensions, Mara no longer felt constrained by her tech. She navigated the web with confidence, knowing that the perfect browser is not a single tool, but the harmony between core software and the extensions we choose.
Setting the Scene
Imagine the crisp Ubuntu desktop, the gentle clack of a keyboard, and the soft glow of a monitor that is only the beginning of a journey into privacy‑first browsing. The protagonist of this tale is a user who values anonymity, seeks reliable performance, and wants everything to *feel* seamless. The first chapter involves choosing the correct software for the mission: the preferred web browser.
The Landscape of Ubuntu Browsers
On Ubuntu, the most common champions are Firefox Nightly, Chromium, Brave, and the legendary Tor Browser. Each offers a different story. Firefox Nightly promises cutting‑edge privacy tech, while Chromium brings the speed that many developers love. Brave introduces a revenue‑free experience and ad‑blocking by default. But when the narrative demands **unstealthy anonymity**, the Tor Browser takes center stage, a paragon that’s been hardened with *Tor*’s onion routing for years.
Why Tor Browser? The First Line of Defense
The tor‑powered browser is engineered to render every webpage as if it were coming from a mysterious fjord in the digital world. It blocks containerized trackers, removes fingerprints, and operates stream‑by‑stream over relays. Yet, even a well‑designed hero can benefit from side arms. Enter Tor Browser extensions, which transform a solid foundation into a formidable fortress.
Choosing Extensions: What the Story Requires
Adding extensions to Tor Browser is like armoring armor with enchanted rungs. The initial step is to enable the Tor Browser’s Extension Manager, which now offers curated addons that meet strict compliance with Tor’s security practices. Below are some of the most recent and recommended extensions that help our brave user navigate the shadowy corners of the web safely:
1. uBlock Origin for Privacy-First Ad Blocking
Unlike generic blockers, uBlock Origin is lightweight and respects the Tor Browser’s security model. It intercepts intrusive scripts and prevents unwanted data collection, keeping the browser swift and the user’s data *guarded*.
2. NoScript (re‑branded as Permissioned Scripts)
Script control is the silver bullet against malicious attacks. This extension allows the user to line‑up only the scripts that are safe to run, forming a selective gate that blocks invasive code while preserving functionality in trusted sites.
3. HTTPS Everywhere Standardized
Seamless HTTPS is now baked into Tor Browser, but the latest iterations of HTTPS Everywhere refine protocol upgrades, ensuring the browser automatically migrates to more secure transports whenever possible.
4. Decentralized DNS Resolver
Replacing the default DNS with a resolver that refuses to leak IP addresses or location—such as 3.0ish or a local forwarder that forwards to Tor's DNS—adds an extra layer of concealment.
5. Patchwork for Journalists
An extension often used by journalists who care about field reporting: it bundles an assortment of privacy tools into a single package, from Torbird for secure email to Pidgin with OTG for encrypted chat. The bundle is lightweight and easy to install for those who need more than just browsing.
Installation: The Way of the Contributor
The text-adventure of installing these addons natively goes like this:
First, open the Tor Browser and navigate to the Extensions Manager. Click the persona icon in the toolbar, select Add-ons, then hit the heart for each extension. Accept the confirmations that highlight how each addon adheres to Tor’s privacy guidelines. Finally, restart the browser—only once—to let the new guardians take effect.
Balancing Performance with Security
Every narrative afterward must keep pace with the tempo of life, so caution is taken not to bake in elements that degrade the user experience. Consequently, extensions that do not observe the audit requirements are omitted. The result is a browser that is fast, lightweight, yet still strictly secure—a virtuous amalgam that Spielberg might film, but with code and philosophy in place.
A Closing Note: The Daily Ritual
At the end of each day, the user closes the Tor Browser, flips to the lock icon in the command line, and double‑checks that no unwanted processes remain. The browser is preserved as an artifact for tomorrow’s quest, ready to open a new hidden door fully armored with carefully selected extensions. And the story continues, one secure click at a time.
The Search for the Ideal Browser
On a crisp Ubuntu 24.04 installation, a novice user named Lina turned to the command line to decide which web browser would best support her day‑to‑day productivity. She typed sudo apt install chromium-browser and watched the package manager finish. The system, humming quietly, installed a clean, up‑to‑date version of Chromium that was already integrated with Ubuntu’s policy of open source compliance. Lina felt a spark of confidence, knowing that Chromium’s automatic updates would keep her browsing experience buttery smooth.
Discovering Extensions that Add Magic
Once Lina launched Chromium, she navigated to the settings page and opened the dedicated extensions manager. The interface was tidy, with a toggle to enable or disable extensions in a single click. ">The first extension she added was uBlock Origin," she mused, because she had heard of its razor‑sharp block‑listing capabilities. With a single Install button, the ad‑blocking plugin appeared, and the next webpage she opened was devoid of pop‑ups and tracking scripts. The feel of a cleaner internet was obvious, and Lina felt a quiet triumph at the power of choice.
She then discovered Dark Reader, a tool that rewrites page colours to a pleasant inset, reducing eye strain during long coding sessions. Lina experimented with the default theme and adjusted the brightness slider until her workspace seemed almost synthetic in a good way. The extension's icon glowed orange behind her new favourite browser window, a reassuring sign that the switch had worked.
Privacy was the next terrain she explored. She added the HTTPS Everywhere extension, which automatically upgraded websites to their secure HTTPS versions whenever possible. In the same breath, she glanced at the new Privacy Badger available from the Mozilla Web Store, whose intuitive red trust indicator gave instant visual feedback on tracker behaviour. After a few days of practice, Lina discovered that browsing had become less like a battle and more like a high‑speed train moving direct to her destination.
Extending Everyday Tasks
Not to be left out, the world of productivity extensions unfolded like a library of possible skills. Lina fetched OneTab to fold multiple open tabs into a single list, sparking a huge memory saving on her laptop. When she later needed to save up to a dozen URLs for a research project, she saw them neatly arranged in a snapshot and worried no longer about losing track.
Snippets of code became easier when she added Octotree for a tree view of GitHub repositories, or the Postman extension for quick API tests. Lina, once overwhelmed by the amount of tabs she opened while brewing coffee, discovered that the reduced clutter meant she could come back to her work more quickly, with a clear view of what she had been handling.
A Flourishing Browser Experience
Weeks later, Lina found her browsing routine had become a rhythm. She would kick off her Linux desktop with Chromium, trigger her favourite set of extensions, take advantage of the streamlined UI, and complete her day with a feeling of accomplishment. Her system remained lean, her privacy tighter, and her productivity truly high‑speed.
For anyone glancing at Ubuntu’s menu and wondering which browser to choose, keras the story of Lina suggests starting with Chromium. Install it with the package manager, then build it into something uniquely yours through extensions. The combination of an open‑source engine and a vibrant, ever‑changing world of plugins means you’re not just surfing the web—you’re sculpting a digital environment tailored just for you.
© 2020 - 2026 Catbirdlinux.com, All Rights Reserved. Written and curated by WebDev Philip C. Contact, Privacy Policy and Disclosure, XML Sitemap.